开启威胁情报
下载
聚焦模式
字号
开启威胁情报后,云防火墙会将互联网边界流量接入威胁情报检测与分析引擎,识别访问控制规则以外的未知风险。针对重保场景,推出了重保情报包功能,加强了风险抵御能力。
操作步骤
1. 登录 云防火墙控制台,在左侧导航栏中,单击入侵防御。
2. 在入侵防御页面,单击威胁情报处的

注意

3. 开启威胁情报后,云防火墙会将互联网边界流量接入威胁情报检测与分析引擎,识别访问控制规则以外的未知风险:
外部恶意访问:监控并识别来自外部的恶意扫描、暴力破解、挖矿木马、勒索软件、远程控制等恶意 IP 和威胁样本,对云上资产发起的访问。
主动外联行为:监控并识别云上资产向外部恶意 IP 地址或域名发起的主动外联,并根据威胁情报提供的大数据对比分析,判断可能发生的主机失陷风险。
4. 在威胁情报模块,单击查看详情,进入高级设置页面。
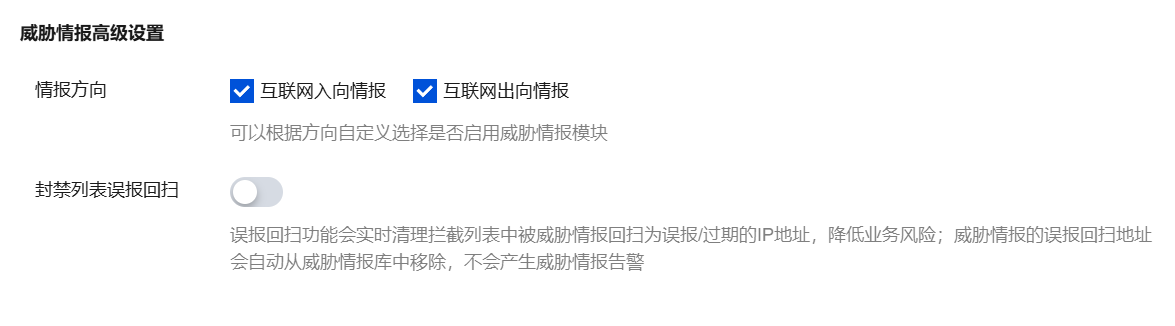
威胁情报高级设置:
情报方向:可根据方向自定义选择互联网入向情报和互联网出向情报。
封禁列表误报回扫:误报回扫功能会实时清理拦截列表中被威胁情报回扫为误报/过期的 IP 地址,降低业务风险。开启此开关后,威胁情报的误报回扫地址会自动从威胁情报库中移除,不会产生威胁情报告警。
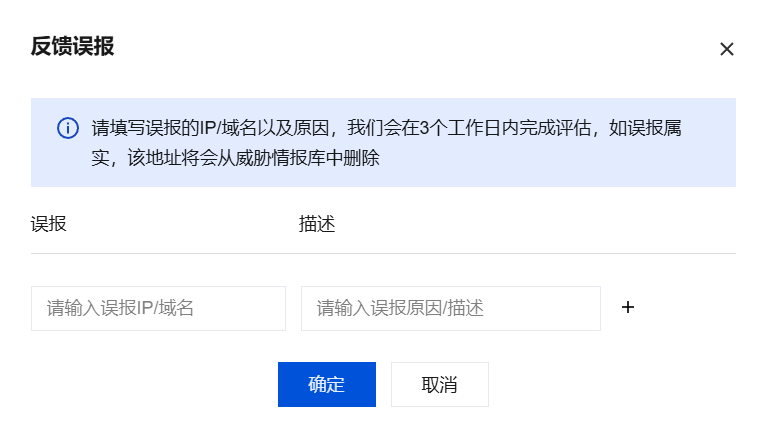
反馈误报:
单击反馈误报,填写误报的 IP /域名以及原因,我们会在3个工作日内完成评估,如误报属实,该地址将会从威胁情报库中删除。
可查看误报回扫记录和反馈记录。支持选择多种资源属性进行查询。
相关信息
文档反馈