- Tutorial
- Release Notes and Announcements
- Public Image Release Notes
- Announcements
- Updating Some Image Pip Package Management Tools for CentOS 7
- CentOS 8 End of Maintenance
- Discontinuation of Support for SUSE Commercial Images
- Price Reduction in Selected Availability Zones
- OrcaTerm Proxy IP Addresses Updates
- Pay-as-you-go Price Adjustments for Standard S3 CVMs in the Silicon Valley Region
- Vulnerability repairing for Linux images
- Stopping supporting for Ubuntu 10.04 images
- Solution to Tomcat Start Failure on Ubuntu14.04
- Upgrading Virtio network card drive for Windows CVMs
- About Configuration of Security Group Port 53
- Windows Server 2003 System Images End of Support Announcement
- End of Support for Windows Server 2008 R2 Enterprise Edition SP1 64-bit System Images
- Product Introduction
- Purchase Guide
- Getting Started
- Operation Guide
- Operation Guide Overview
- Use Limits
- Convenience Features
- Instances
- Creating Instances
- Managing Instance Launch Template
- Batch Sequential Naming or Pattern String-Based Naming
- Logging In to Linux Instances
- Logging in to Windows instance
- Adjusting Configuration
- View Instance Details
- Renaming Instances
- Resetting Instance Password
- Managing Instance IPs
- Changing Instance Subnet
- Changing Security Group
- Conversion from Pay-As-You-Go to Monthly Subscription
- Searching for Instances
- Exporting Instance List
- Renewing Instances
- Starting Up Instances
- Shutting Down Instances
- Restarting Instances
- Reinstalling System
- Using Tencent Cloud Automation Tools to execute commands
- Terminating/Returning Instances
- Enabling Instance Termination Protection
- Instance Repossession or Recovering
- Spot Instances
- Querying the Repossession Status of a Spot Instance
- No Charges When Shut Down for Pay-as-You-Go Instances
- Managing Roles
- Enabling and Disabling Hyper-Threading
- Reserved Instances
- Images
- Migrating Servers
- Maintenance Tasks
- Cloud Disks
- Networking
- Security
- Security Groups
- Protection of Sensitive Operations
- Managing Login Password
- Managing SSH Keys
- Spread Placement Group
- Unblocking Port 25
- Tags
- Monitoring and Alarms
- Sample Console Configuration
- Best Practice
- Best Practices
- Choosing the CVM Model
- Setting up a Website
- Building an Environment
- Building a Website
- Building an Application
- Building a Visual GUI
- Data Backup
- Uploading Local Files to CVM
- Copying Local Files to CVMs
- Uploading Files from Windows to a Windows CVM via MSTSC
- Uploading Files from MacOS to Windows CVM Using MRD
- Uploading Files from Linux to Windows CVM using RDP
- Uploading files via WinSCP to a Linux CVM from Windows
- Uploading Files from Linux or MacOS to Linux CVM via SCP
- Uploading Files from Linux to a CVM Using FTP
- Uploading Files from Windows to a CVM Using FTP
- Other CVM Operations
- CVM Access to COS via a Private Network
- Best Practices for Boot Mode Legacy BIOS and UEFI
- Recovering Data on Linux CVMs
- Managing Disk Space on Windows CVMs
- Changing Kernel of a Linux Instance Manually
- Setting Up Windows-based AD Domain on a CVM
- Network Performance Test
- High-throughput Network Performance Test
- Using USB/IP to Share USB Devices in Linux
- Using RemoteFx to Redirect USB Devices in Windows
- Using AVX-512 Instructions to Accelerate AI Applications on CVM
- Building Tencent SGX Confidential Computing Environment
- Configuring Persistent Memory in M6p Instances
- Calling Cloud APIs via Python to Share Custom Images in Batches
- Operations Guide
- Initializing Data Disks
- Environment Configurations
- Installing Software
- User Data
- Work with Operating Systems
- System Activation
- System Updates
- System Shutdown
- Configuring High-performance Power Management
- Windows Recovery Mode
- Updating the Virtio ENI Driver
- Modifying SID
- Modifying VNC Resolution
- Ensuring Unique SIDs for CVMs Using Sysprep
- Use of the atop Monitoring Tools by Linux Instances
- Introduction to Linux Kernel Parameters
- Others
- Troubleshooting
- Instance-Related Failures
- CVM Login Failures
- Windows Instance Login Failures
- Windows Instance Login Failures
- An authentication error occurred when you tried to log in to a Windows instance remotely
- Failed to Reset the CVM Password or the CVM Password Is Invalid
- Connection to a Windows CVM through Remote Desktop was denied
- Requires network-level identity verification
- Problems occurred when you tried to log in to a Windows CVM remotely on Mac
- Failed to log in to a Windows CVM due to high CPU and memory usage
- Failed to connect to a remote computer through Remote Desktop
- Credentials Not Work
- Windows instance: no remote Desktop license server can provide license
- Remote Login Failure Due To Port Issues
- Linux Instance Login Failures
- Linux Instance Login Failures
- Unable to Log in to a Linux Instance via SSH Key
- Failing to log in to a Linux CVM due to high CPU and memory usage
- Remote Login Failure due to Port Issues
- VNC Login Error (Module is Unknown)
- VNC Login Error (Account Locked due to XXX Failed Logins)
- VNC Login Error (Login Failed with Correct Password)
- VNC or SSH Login Error (Permission Denied)
- Login Failure Due to /etc/fstab Configuration Errors
- sshd Configuration File Permissions
- Infinite Loop Call in /etc/profile
- Login Failure Due to Server Isolation
- Login Failure Due to High Bandwidth Occupation
- Remote Connect Failure Due to Security Group Settings
- Troubleshooting Linux Instance Issues via VNC and Rescue Mode
- Failed to shut down or restart a CVM
- Network Namespace Creation Failure
- Kernel and IO Issues
- Missing System bin or lib Soft Link
- Suspected Infection with Virus
- "no space left on device" Error During File Creation
- Linux CVM Memory Issues
- Network Related Failures
- Instance-Related Failures
- API Documentation
- History
- Introduction
- API Category
- Making API Requests
- Region APIs
- Instance APIs
- DescribeInstances
- DescribeInstanceFamilyConfigs
- DescribeZoneInstanceConfigInfos
- DescribeInstanceTypeConfigs
- DescribeInstancesOperationLimit
- DescribeInstanceVncUrl
- InquiryPriceRunInstances
- InquiryPriceResetInstance
- InquiryPriceResetInstancesType
- InquiryPriceResizeInstanceDisks
- RunInstances
- StartInstances
- RebootInstances
- StopInstances
- ResetInstance
- TerminateInstances
- ResetInstancesType
- ResizeInstanceDisks
- ResetInstancesPassword
- ModifyInstancesAttribute
- ModifyInstancesProject
- InquirePricePurchaseReservedInstancesOffering
- DescribeReservedInstancesConfigInfos
- DescribeInstancesStatus
- PurchaseReservedInstancesOffering
- Cloud Hosting Cluster APIs
- Placement Group APIs
- Image APIs
- Key APIs
- Security Group APIs
- Network APIs
- Instance Launch Template APIs
- Data Types
- Error Codes
- FAQs
- Related Agreement
- Glossary
- Tutorial
- Release Notes and Announcements
- Public Image Release Notes
- Announcements
- Updating Some Image Pip Package Management Tools for CentOS 7
- CentOS 8 End of Maintenance
- Discontinuation of Support for SUSE Commercial Images
- Price Reduction in Selected Availability Zones
- OrcaTerm Proxy IP Addresses Updates
- Pay-as-you-go Price Adjustments for Standard S3 CVMs in the Silicon Valley Region
- Vulnerability repairing for Linux images
- Stopping supporting for Ubuntu 10.04 images
- Solution to Tomcat Start Failure on Ubuntu14.04
- Upgrading Virtio network card drive for Windows CVMs
- About Configuration of Security Group Port 53
- Windows Server 2003 System Images End of Support Announcement
- End of Support for Windows Server 2008 R2 Enterprise Edition SP1 64-bit System Images
- Product Introduction
- Purchase Guide
- Getting Started
- Operation Guide
- Operation Guide Overview
- Use Limits
- Convenience Features
- Instances
- Creating Instances
- Managing Instance Launch Template
- Batch Sequential Naming or Pattern String-Based Naming
- Logging In to Linux Instances
- Logging in to Windows instance
- Adjusting Configuration
- View Instance Details
- Renaming Instances
- Resetting Instance Password
- Managing Instance IPs
- Changing Instance Subnet
- Changing Security Group
- Conversion from Pay-As-You-Go to Monthly Subscription
- Searching for Instances
- Exporting Instance List
- Renewing Instances
- Starting Up Instances
- Shutting Down Instances
- Restarting Instances
- Reinstalling System
- Using Tencent Cloud Automation Tools to execute commands
- Terminating/Returning Instances
- Enabling Instance Termination Protection
- Instance Repossession or Recovering
- Spot Instances
- Querying the Repossession Status of a Spot Instance
- No Charges When Shut Down for Pay-as-You-Go Instances
- Managing Roles
- Enabling and Disabling Hyper-Threading
- Reserved Instances
- Images
- Migrating Servers
- Maintenance Tasks
- Cloud Disks
- Networking
- Security
- Security Groups
- Protection of Sensitive Operations
- Managing Login Password
- Managing SSH Keys
- Spread Placement Group
- Unblocking Port 25
- Tags
- Monitoring and Alarms
- Sample Console Configuration
- Best Practice
- Best Practices
- Choosing the CVM Model
- Setting up a Website
- Building an Environment
- Building a Website
- Building an Application
- Building a Visual GUI
- Data Backup
- Uploading Local Files to CVM
- Copying Local Files to CVMs
- Uploading Files from Windows to a Windows CVM via MSTSC
- Uploading Files from MacOS to Windows CVM Using MRD
- Uploading Files from Linux to Windows CVM using RDP
- Uploading files via WinSCP to a Linux CVM from Windows
- Uploading Files from Linux or MacOS to Linux CVM via SCP
- Uploading Files from Linux to a CVM Using FTP
- Uploading Files from Windows to a CVM Using FTP
- Other CVM Operations
- CVM Access to COS via a Private Network
- Best Practices for Boot Mode Legacy BIOS and UEFI
- Recovering Data on Linux CVMs
- Managing Disk Space on Windows CVMs
- Changing Kernel of a Linux Instance Manually
- Setting Up Windows-based AD Domain on a CVM
- Network Performance Test
- High-throughput Network Performance Test
- Using USB/IP to Share USB Devices in Linux
- Using RemoteFx to Redirect USB Devices in Windows
- Using AVX-512 Instructions to Accelerate AI Applications on CVM
- Building Tencent SGX Confidential Computing Environment
- Configuring Persistent Memory in M6p Instances
- Calling Cloud APIs via Python to Share Custom Images in Batches
- Operations Guide
- Initializing Data Disks
- Environment Configurations
- Installing Software
- User Data
- Work with Operating Systems
- System Activation
- System Updates
- System Shutdown
- Configuring High-performance Power Management
- Windows Recovery Mode
- Updating the Virtio ENI Driver
- Modifying SID
- Modifying VNC Resolution
- Ensuring Unique SIDs for CVMs Using Sysprep
- Use of the atop Monitoring Tools by Linux Instances
- Introduction to Linux Kernel Parameters
- Others
- Troubleshooting
- Instance-Related Failures
- CVM Login Failures
- Windows Instance Login Failures
- Windows Instance Login Failures
- An authentication error occurred when you tried to log in to a Windows instance remotely
- Failed to Reset the CVM Password or the CVM Password Is Invalid
- Connection to a Windows CVM through Remote Desktop was denied
- Requires network-level identity verification
- Problems occurred when you tried to log in to a Windows CVM remotely on Mac
- Failed to log in to a Windows CVM due to high CPU and memory usage
- Failed to connect to a remote computer through Remote Desktop
- Credentials Not Work
- Windows instance: no remote Desktop license server can provide license
- Remote Login Failure Due To Port Issues
- Linux Instance Login Failures
- Linux Instance Login Failures
- Unable to Log in to a Linux Instance via SSH Key
- Failing to log in to a Linux CVM due to high CPU and memory usage
- Remote Login Failure due to Port Issues
- VNC Login Error (Module is Unknown)
- VNC Login Error (Account Locked due to XXX Failed Logins)
- VNC Login Error (Login Failed with Correct Password)
- VNC or SSH Login Error (Permission Denied)
- Login Failure Due to /etc/fstab Configuration Errors
- sshd Configuration File Permissions
- Infinite Loop Call in /etc/profile
- Login Failure Due to Server Isolation
- Login Failure Due to High Bandwidth Occupation
- Remote Connect Failure Due to Security Group Settings
- Troubleshooting Linux Instance Issues via VNC and Rescue Mode
- Failed to shut down or restart a CVM
- Network Namespace Creation Failure
- Kernel and IO Issues
- Missing System bin or lib Soft Link
- Suspected Infection with Virus
- "no space left on device" Error During File Creation
- Linux CVM Memory Issues
- Network Related Failures
- Instance-Related Failures
- API Documentation
- History
- Introduction
- API Category
- Making API Requests
- Region APIs
- Instance APIs
- DescribeInstances
- DescribeInstanceFamilyConfigs
- DescribeZoneInstanceConfigInfos
- DescribeInstanceTypeConfigs
- DescribeInstancesOperationLimit
- DescribeInstanceVncUrl
- InquiryPriceRunInstances
- InquiryPriceResetInstance
- InquiryPriceResetInstancesType
- InquiryPriceResizeInstanceDisks
- RunInstances
- StartInstances
- RebootInstances
- StopInstances
- ResetInstance
- TerminateInstances
- ResetInstancesType
- ResizeInstanceDisks
- ResetInstancesPassword
- ModifyInstancesAttribute
- ModifyInstancesProject
- InquirePricePurchaseReservedInstancesOffering
- DescribeReservedInstancesConfigInfos
- DescribeInstancesStatus
- PurchaseReservedInstancesOffering
- Cloud Hosting Cluster APIs
- Placement Group APIs
- Image APIs
- Key APIs
- Security Group APIs
- Network APIs
- Instance Launch Template APIs
- Data Types
- Error Codes
- FAQs
- Related Agreement
- Glossary
A security group is a virtual firewall that features stateful data packet filtering. It is used to configure the network access control of CVM, Cloud Load Balancer, TencentDB, and other instances while controlling their outbound and inbound traffic. It is an important means of network security isolation.
You can configure security group rules to allow or reject inbound and outbound traffic of instances within the security group.
Security Group Features
A security group is a logical group. You can add CVM, ENI, TencentDB, and other instances in the same region with the same network security isolation requirements to the same security group.
If a security group has no rules, it will reject all traffic by default, and you need to add rules to it to allow traffic.
Security groups are stateful. Inbound traffic you have allowed can automatically become outbound and vice versa.
You can modify security group rules at any time, and the new rules will take effect immediately.
Usage Limits
Security Group Rules
Components
A security group rule consists of:
Source: IP address of the source data (inbound) or target data (outbound)
Protocol type and protocol port: Protocol type such as TCP and UDP
Policy: Allow or reject the access request.
Rule priorities
The rules in a security group are prioritized from top to bottom. The rule at the top of the list has the highest priority and will take effect first, while the rule at the bottom has the lowest priority and will take effect last.
If there is a rule conflict, the rule with the higher priority will prevail by default.
When the traffic goes in to or out from an instance bound to a security group, the security group rules are calculated from top to bottom. If a rule is matched and executed (allow/reject requests), the subsequent rules will not be matched.
Multiple security groups
An instance can be bound to one or multiple security groups. When it is bound to multiple security groups, the security group rules are calculated from top to bottom. You can adjust the priorities of security groups at any time.
Security Group Templates
Tencent Cloud provides the following two security group templates:
Open all ports: All inbound and outbound traffic are allowed
Open common ports : It opens port TCP 22 (for Linux SSH login), ports 80 and 443 (for Web service), port 3389 (for Windows remote login), the ICMP protocol (for Ping commands), and allows all traffic from the private network.
Note:
If these templates cannot meet your actual needs, you can create custom security groups. For more information, see Creating a Security Group and Security Group Use Cases.
If you need to protect the application layer (HTTP/HTTPS), please activate Tencent Cloud Web Application Firewall (WAF), which provides web security at the application layer to defend against web vulnerabilities, malicious crawlers, and CC attacks, protecting your websites and web applications security.
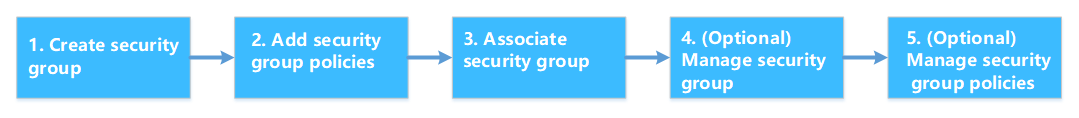
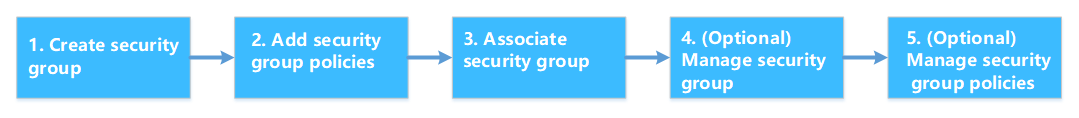
Directions
The following figure shows you how to use a security group:
Security Group Best Practices
Creating a security group
We recommend that you specify a security group while you’re purchasing a CVM via the API. Otherwise, the default security group will be used. The default security group cannot be deleted, and it adopts the default security rule (i.e., allowing all IPv4 addresses). You can modify the security rule after the security group is created.
If you need to change the instance protection policy, we recommend modifying the existing rules rather than creating a new security group.
Managing rules
Export and back up the security group rules before you modify them, so you can import and restore them if an error occurs.
To create multiple security group rules, please use the parameter template.
Associating a security group
You can add instances with the same protection requirements to the same security group, instead of configuring a separate security group for each instance.
It's not recommended to bind one instance to too many security groups, which may cause rule conflicts and result in network disconnection.

 Yes
Yes
 No
No
Was this page helpful?