証明書をCLBに配置(双方向認証)
ダウンロード
フォーカスモード
フォントサイズ
操作シナリオ
従来の単方向認証は、クライアントはサーバーの識別情報のみを検証しますが、より高いセキュリティが求められるシナリオでは、単方向認証はセキュリティ要件を満たすことができません。双方向認証は、クライアントとサーバーの双方が互いの識別情報を検証する必要があります。これにより、通信の安全性が強化され、中間者攻撃、なりすまし、データ漏洩を効果的に防止できます。単方向認証と双方向認証の詳細については、単方向認証と双方向認証の説明をご参照ください。
前提条件
1. CLBインスタンスを作成しました。具体的な操作については、CLBインスタンスの作成をご参照ください。
2. ドメイン名でアクセスする場合は、ドメイン名を所有していること、およびCLBのドメイン転送が設定されていることを確認していください。具体的な操作については、CLBのドメイン転送の設定をご参照ください。
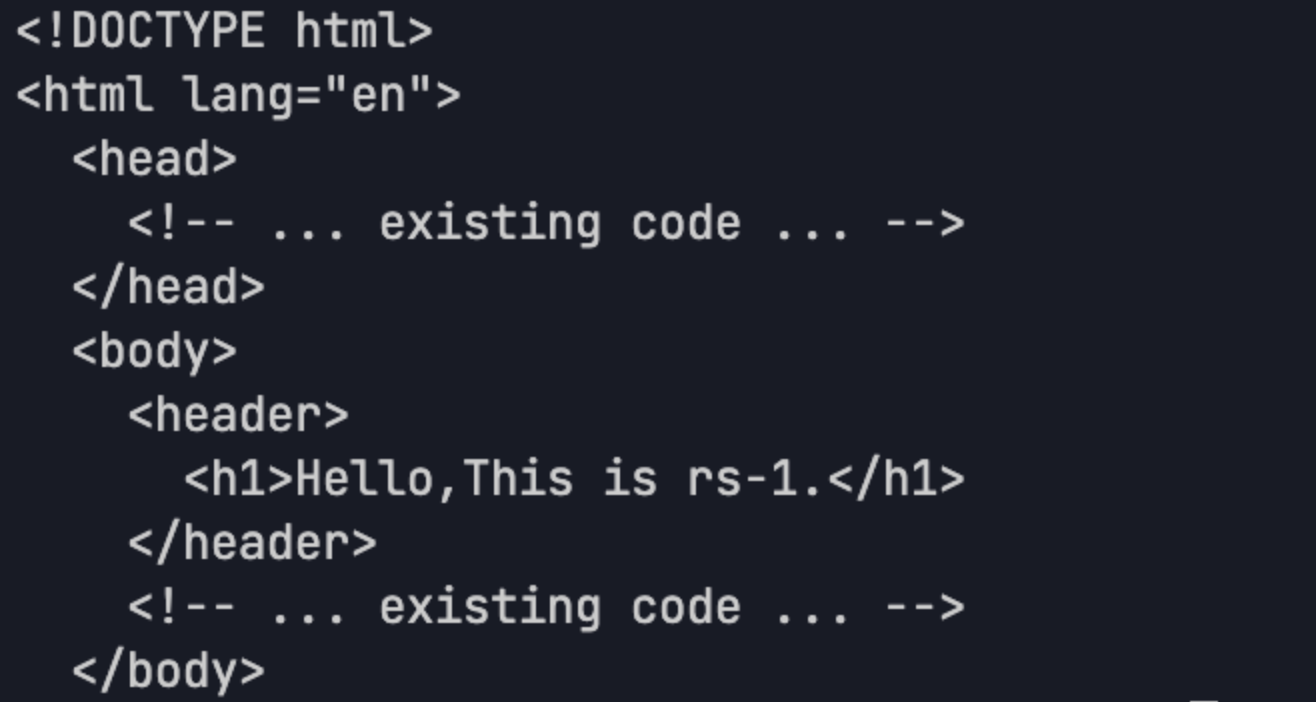
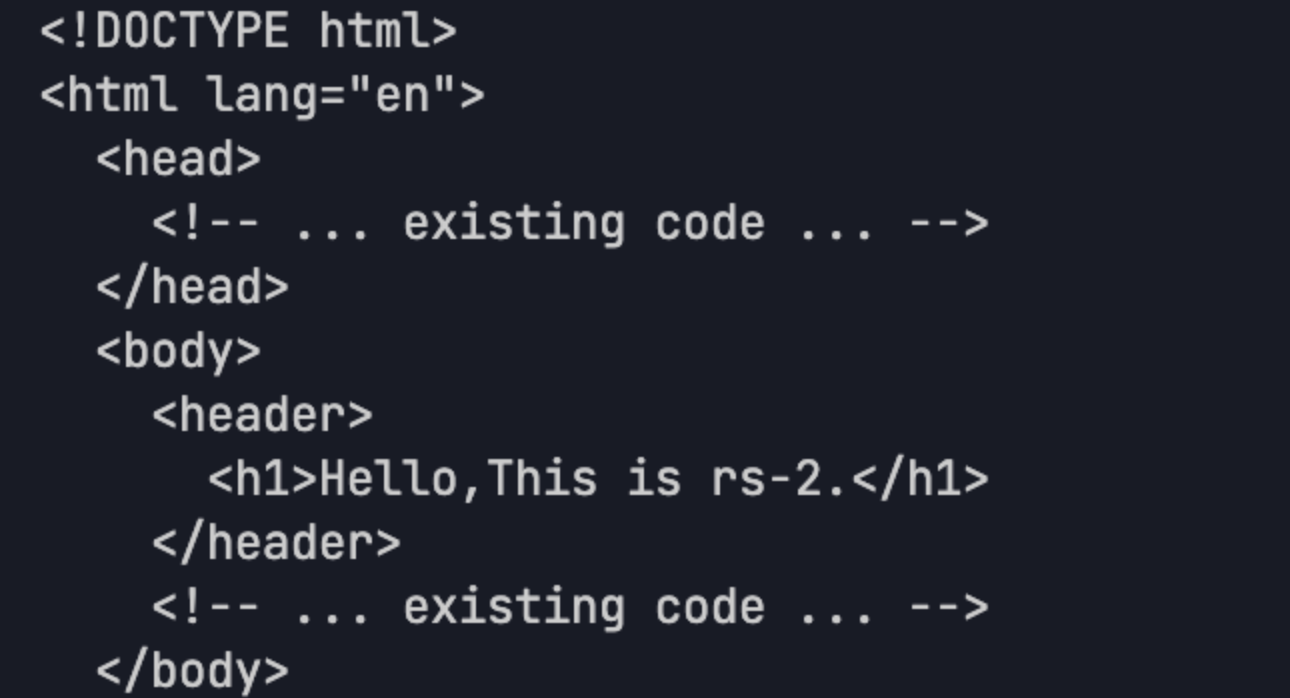
3. CLBインスタンスのバックエンドサーバーとして、CVMインスタンスrs‐1とrs-2を作成しました。具体的な操作については、バックエンドサーバーをご参照ください。
設定手順
自己署名証明書を例として,HTTPS双方向認証CLBを設定する具体的な手順について説明します。
1. CA証明書:証明書を発行する証明機関の証明書です。サーバ証明書またはクライアント証明書の発行に使用できます。
2. サーバ証明書:購入または自己署名の方法でサーバ証明書を取得できます。
3. クライアント証明書:取得したCA証明書を使用してクライアント証明書を発行できます。
4. 証明書をアップロード:CA証明書を証明書プラットフォームにアップロードし、購入または自己署名サーバ証明書をアップロードする必要があります。
5. CLBを設定:HTTPSリスナーを設定する際、双方向認証を有効にする必要があります。サーバ証明書にはアップロードした証明書を選択し、CA証明書は自己署名証明書を選択してください。
6. クライアント証明書をインポート:クライアントにアクセスする時に使用するクライアント証明書をインポートする必要があります。
ステップ1:CA証明書を取得
1. 以下のコマンドを実行し、CA証明書の秘密鍵ファイルca.keyを作成します。
# CA秘密鍵を生成openssl genrsa -out ca.key 2048
2. 以下のコマンドを実行し、CA証明書のリクエストファイルca.csrを作成します。
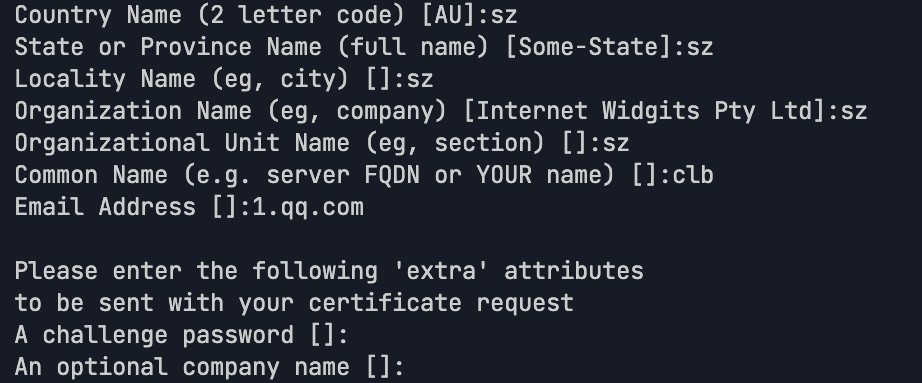
# CA証明書リクエストファイルを生成openssl req -new -key ca.key -out ca.csr
注意:
以下のパラメーターを入力し、そのCommon Nameがサーバ証明書またはクライアント証明書のCommon Nameと異なることを確保lしてください。
3. 以下のコマンドを実行し、自己署名CA証明書ca.crtを作成します。
# 有効期間は3650日の自己署名CA証明書を生成openssl x509 -req -in ca.csr -out ca.crt -signkey ca.key -days 3650
実行成功すると、以下の図のようになります:
ステップ2:サーバ証明書を取得
1. 以下のコマンドを実行し、サーバ証明書の秘密鍵ファイルserver.keyを作成します。
サーバ秘密鍵を生成openssl genrsa -out server.key 2048
2. 以下のコマンドを実行し、サーバ証明書のリクエストファイルserver.csrを作成します。
# サーバ証明書のリクエストファイルを生成openssl req -new -key server.key -out server.csr
3. 以下のコマンドを実行し、CA証明書を使用してサーバ証明書server.crtを発行します。
# CA証明書を使用し、有効期間は365日のサーバ証明書を発行openssl x509 -req -in server.csr -out server.crt -CA ca.crt -CAkey ca.key -CAcreateserial -days 3650
ステップ3:クライアント証明書を取得
1. 以下のコマンドを実行し、クライアント証明書の秘密鍵ファイルclient.keyを作成します。
# クライアント秘密鍵を生成openssl genrsa -out client.key 2048
2. 以下のコマンドを実行し、クライアント証明書のリクエストファイルclient.csrを作成します。
# クライアント証明書のリクエストファイルを生成openssl req -new -key client.key -out client.csr
3. 以下のコマンドを実行し、CA証明書を使用してクライアント証明書client.crtを発行します。
# CA証明書を使用し、有効期間は365日のクライアント証明書を発行openssl x509 -req -in client.csr -out client.crt -CA ca.crt -CAkey ca.key -CAcreateserial -days 3650
4. 以下のコマンドを実行し、生成されたクライアント証明書client.crtをブラウザで認識可能なp12形式のファイルに変換します。
# クライアント証明書の形式を変換openssl pkcs12 -export -clcerts -in client.crt -inkey client.key -out client.p12
ステップ4:CA証明書をアップロード
1. CLBコントロールパネルにログインします。
2. 証明書管理をクリックし、新規作成をクリックします。
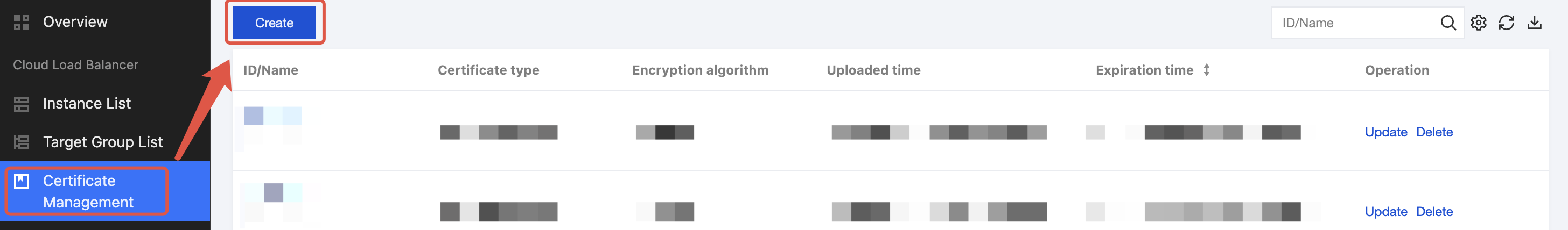
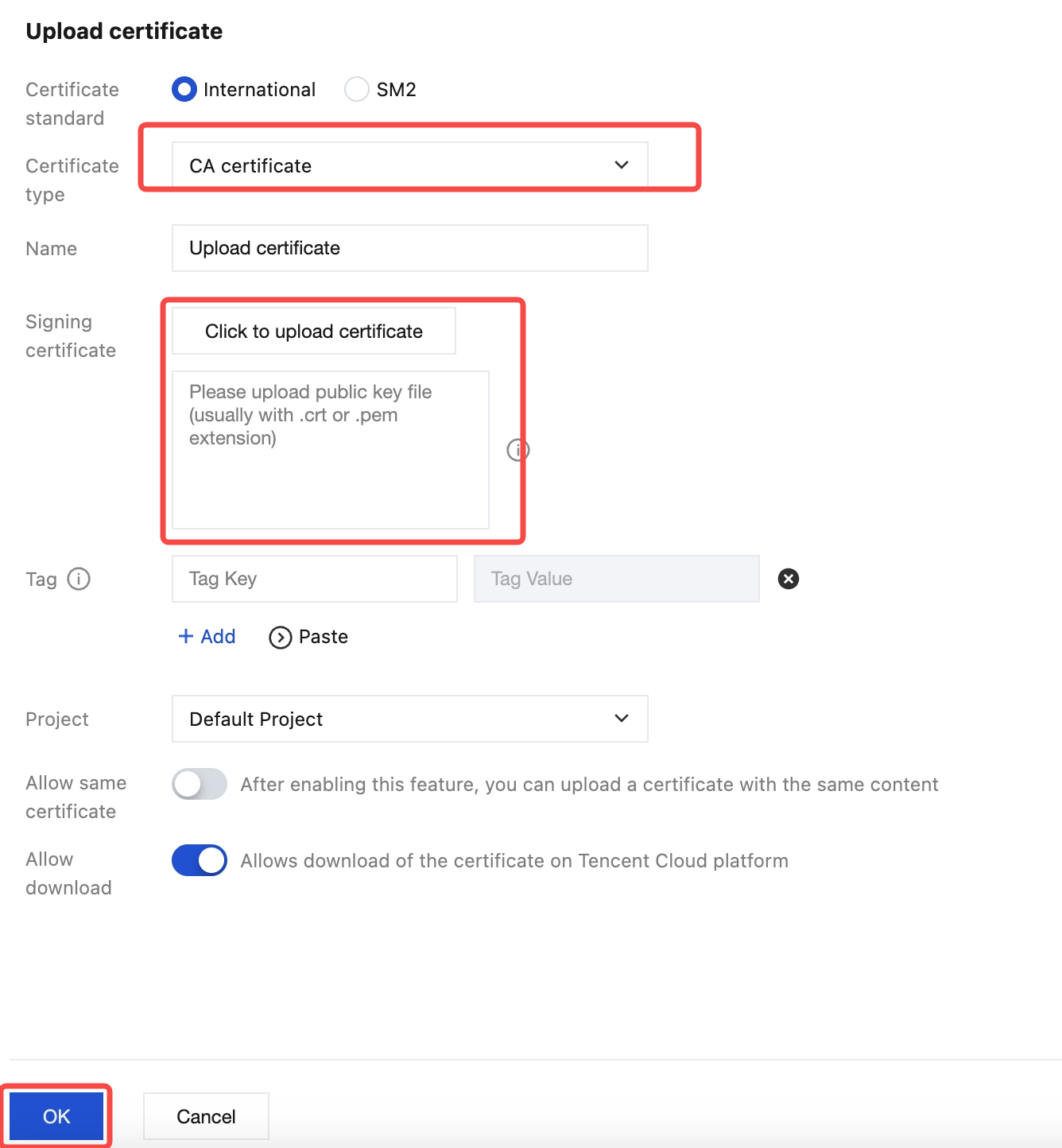
3. 証明書のアップロードページで、証明書タイプにCA証明書を選択し、ステップ1で生成されたCA証明書ca.crtの内容を署名証明書エリアにコピーし、確認をクリックします。
注意:
エラーを防ぐため、コピーする際は最後の改行記号を削除してください。
ステップ5:サーバ証明書をアップロード
1. CLBコントロールパネルにログインします。
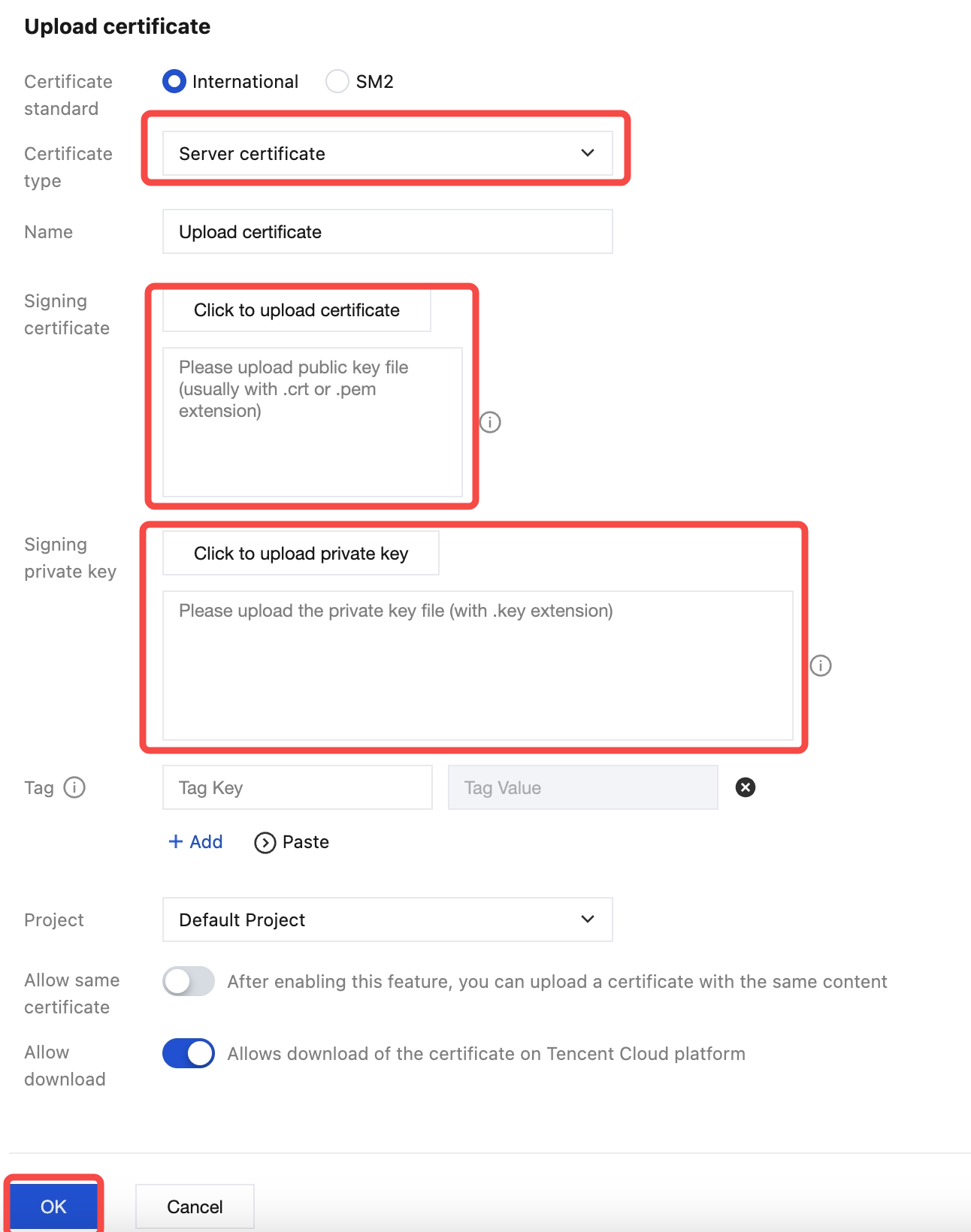
2. 証明書管理をクリックし、新規作成をクリックします。
3. 証明書のアップロードページで、証明書タイプにサーバ証明書を選択し、ステップ2で生成されたサーバ証明書server.crtとサーバ秘密鍵server.keyの内容を署名証明書エリアにコピーし、確認をクリックします。
ステップ6:HTTPS双方向認証リスニングの設定
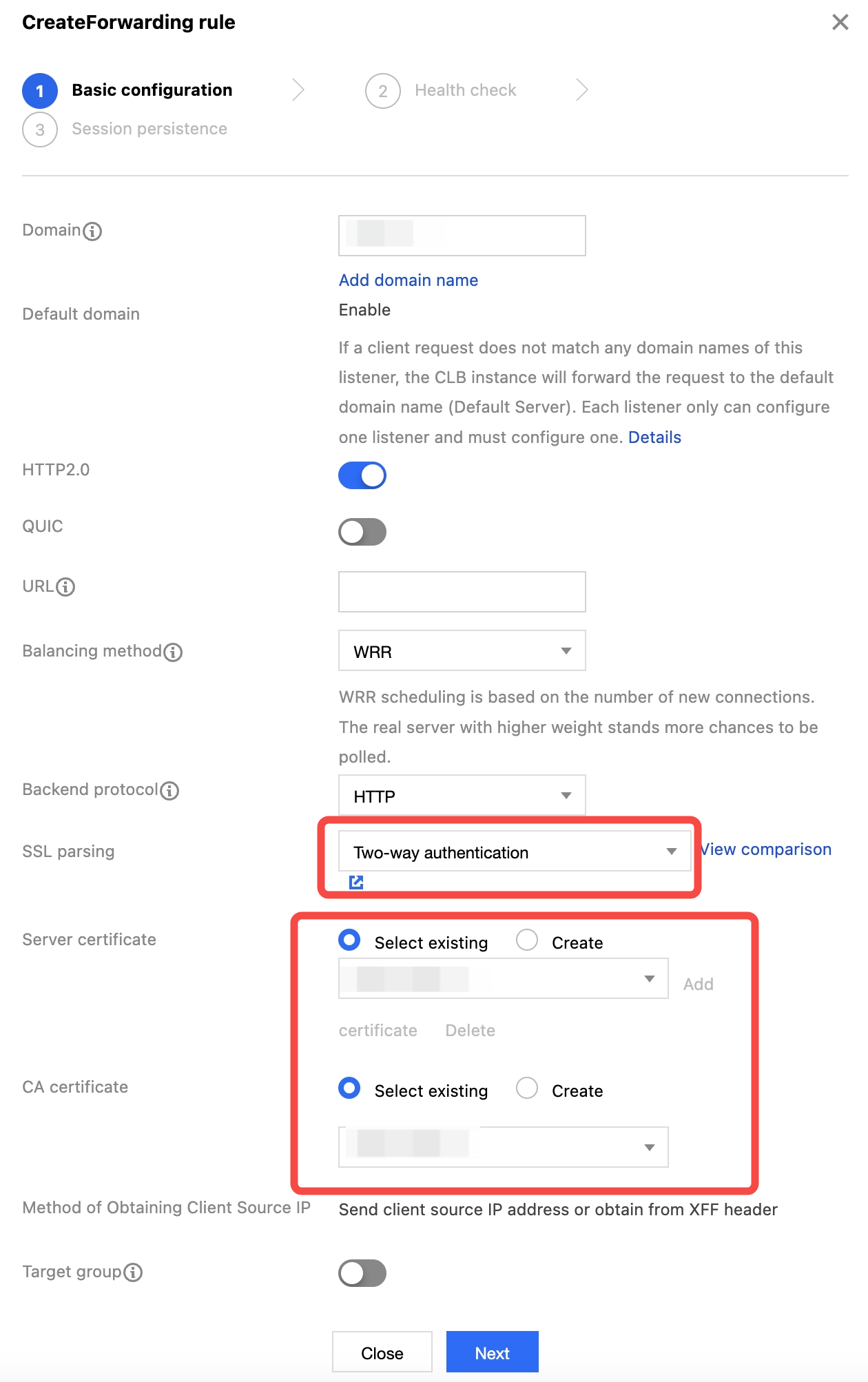
方法1:SNIを無効にする
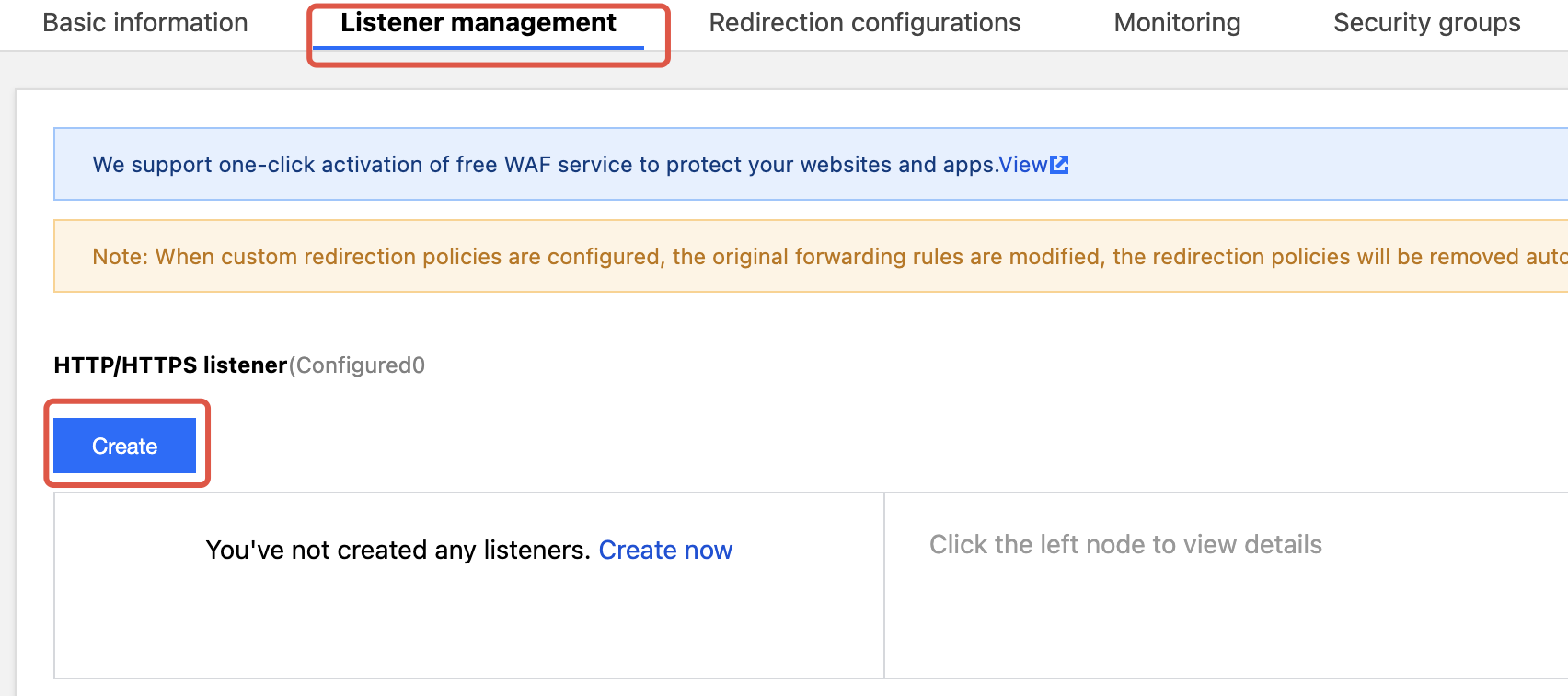
1. CLBコントロールパネルにログインします。インスタンスページで対象のCLBインスタンスを見つけ、インスタンスIDをクリックし、リスナー管理ページで新規作成をクリックします。
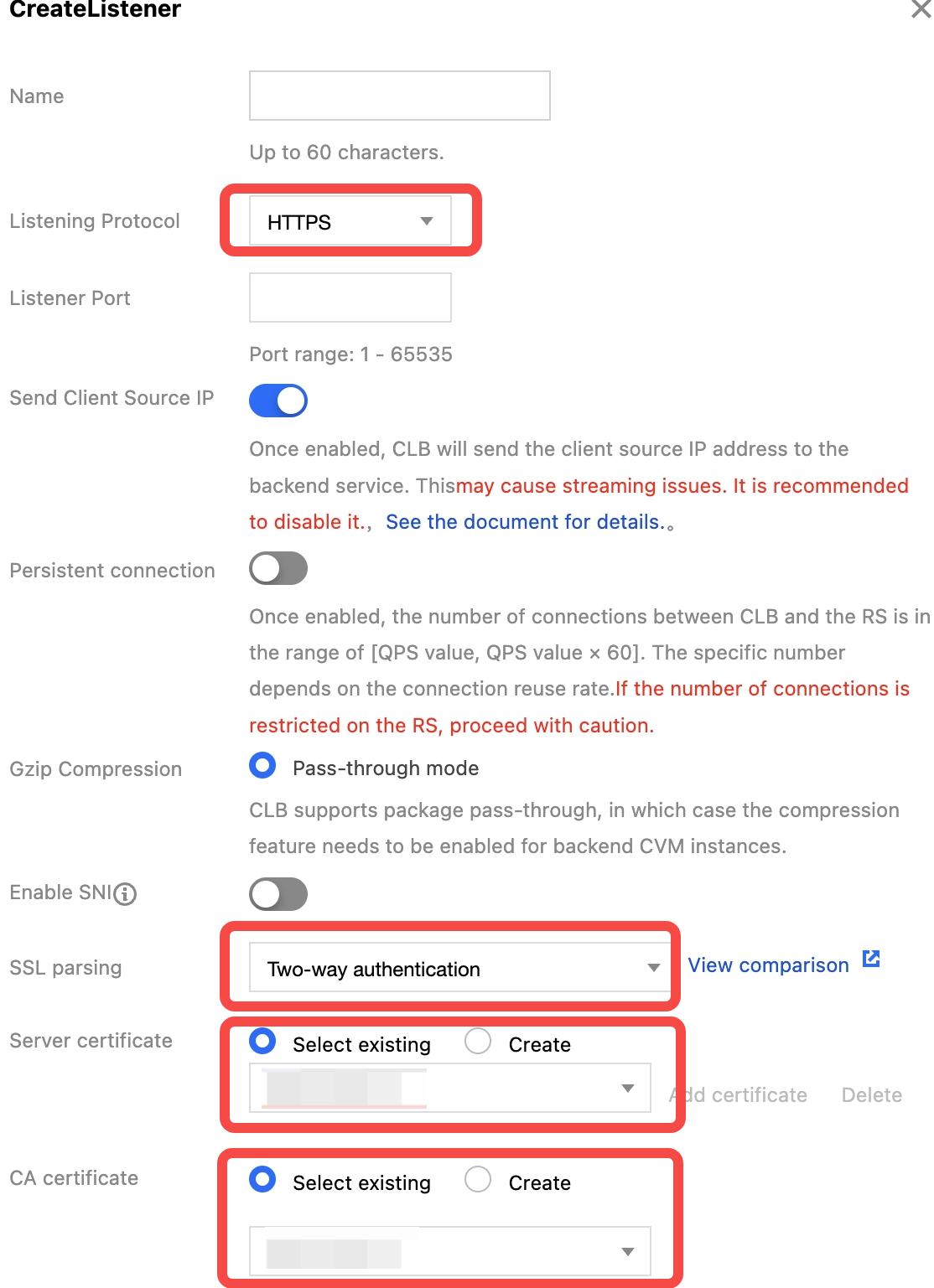
2. 設定画面で、リスニングプロトコルにHTTPSを選択し、指定ポートを入力します。SNIを無効にする場合は、双方向認証方法を選択します。また、取得済みのサーバ証明書とCA証明書をアップロードします。設定情報を確認後、提出をクリックします。
3. プラス記号をクリックして転送ルールを作成します。CLBのドメイン名とURLパスを入力します。バランシング方式とバックエンドプロトコルを選択して基本設定を完了します。
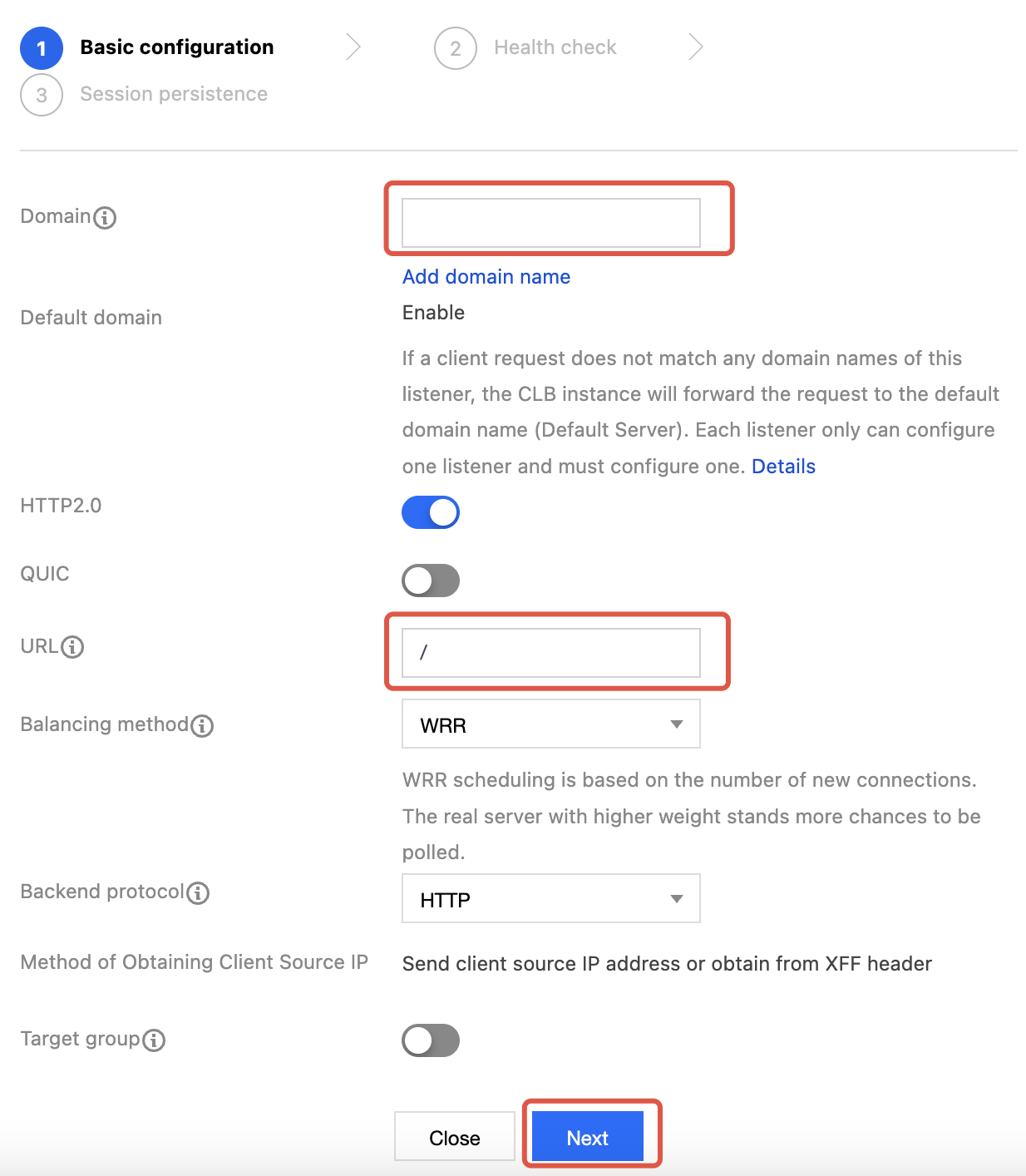
説明:
HTTPSリスニングプロトコルを選択する場合、クライアントからCLBへのアクセスはHTTPSを使用します。CLBからバックエンドサーバーへの転送プロトコルは、HTTPまたはHTTPSを選択できます。
4. ヘルスチェックポートを設定し、選択に応じてセッション維持を設定します。
5. ルールを展開し、バインドをクリックし、作成した2つのバックエンドrs-1、rs-2を選択します。
方法2:SNIを有効にする
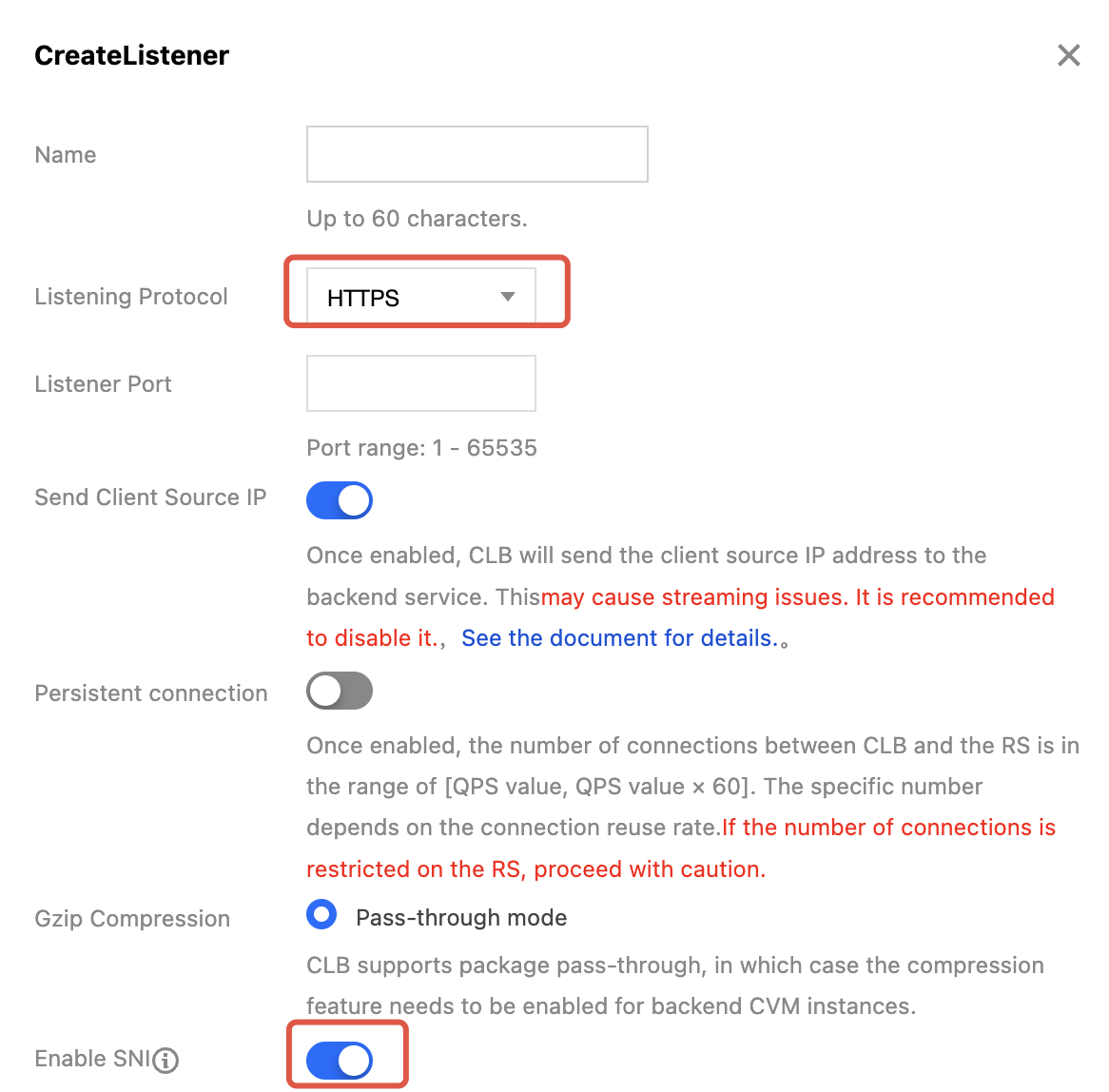
1. 設定画面で、リスニングプロトコルにHTTPSを選択し、指定ポートを入力します。SNIを有効にした後、提出をクリックします。
2. プラス記号をクリックして転送ルールを作成し、CLBのドメイン名とURLパスを入力し、バランシング方式とバックエンドプロトコルを選択して基本設定を完了します。そのドメイン名に対応するサーバ証明書と自己署名CA証明書を入力します。
3. その後の手順は、SNIを無効にするの設定方法と同じです。SNIの詳細な説明については、CLBによるSNIマルチドメイン名証明書のサポートをご参照ください。
ステップ7:クライアント証明書をインポート
方法1:ブラウザ方式
1. 発行されたクライアント証明書client.p12をローカルにダウンロードします。
2. クライアント証明書をダブルクリックし、証明書のインポート案内に従ってクライアント証明書をインストールします。
方法2:コマンドライン方式
1. クライアント証明書client.crtとクライアント秘密鍵ファイルclient.keyを新しいディレクトリにコピーします。
2. 指定ディレクトリのクライアントファイルを使用して、コマンドラインでの検証を実行します。
ステップ8:双方向認証を検証
方法1:ブラウザ方式
1. ブラウザでCLBにバインドされたドメイン名を入力します。ドメイン名がバインドされていない場合は、IPポートにアクセスできます。アクセスする際は、インポート済みのクライアント証明書を選択してください。

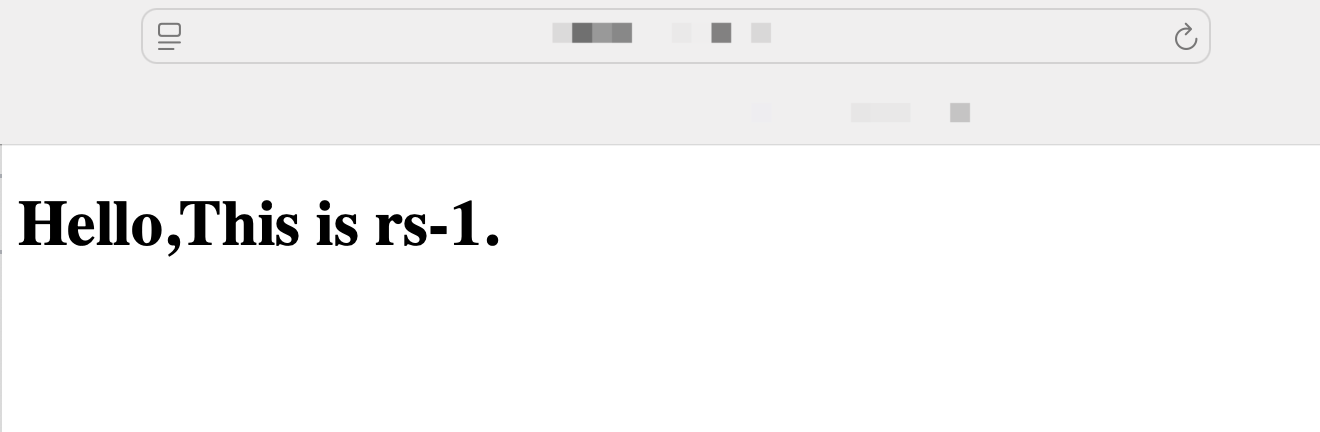
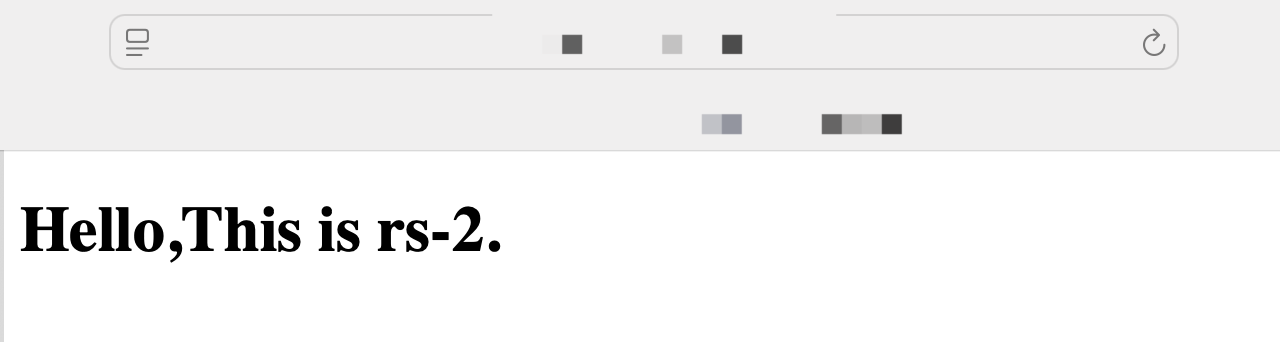
2. ブラウザをリフレッシュし、クライアントからのリクエストがrs-1とrs-2のサーバ間で切り替わることを確認でき次第、検証済みとなります。
方法2:コマンドライン方式
1. shell画面で以下のコマンドを入力し、証明書アドレスとキーアドレス、およびアクセスするCLBのアドレスを確認します。
curl --cert client.crt --key client.key --cacert ca.crt https://xxx.xxx.xxx
2. 対応する正しいステータスコードの出力を確認でき次第、検証済みとなります。
フィードバック