开启透明数据加密
下载
聚焦模式
字号
操作场景
云数据库 MySQL 提供透明数据加密(Transparent Data Encryption,TDE)功能,透明加密指数据的加解密操作对用户透明,支持对数据文件进行实时 I/O 加密和解密,在数据写入磁盘前进行加密,从磁盘读入内存时进行解密,可满足静态数据加密的合规性要求。
密钥管理说明
透明数据加密功能不会额外收费,但密钥管理系统会产生额外费用,请参见 计费概述。
密钥管理系统(后付费版)将于2024年12月30日停止服务,即密钥管理系统将不支持按量计费这种后付费模式,仅支持预付费的计费模式。
对于存量使用密钥管理系统(后付费版)的用户,当账号处于欠费状态时将无法从 KMS 获取密钥,可能导致迁移、升级等任务无法正常进行。
对于新购密钥管理系统(预付费版)的用户,当账号处于欠费状态时,由于密钥管理系统已经预付费了一定周期,在此周期内,不会影响获取 KMS 密钥,迁移、升级等任务不会受此影响。请注意 KMS 密钥续费时间,如果到期后 KMS 密钥没有续费,也会影响透明数据加密功能的使用,管理 KMS 密钥可前往 密钥管理系统控制台。
云数据库 MySQL 实例和密钥管理系统支持的地域情况不同,在创建密钥时,若密钥管理系统上无境内对应的地域,您可选择在广州地域创建,若无境外对应的地域,您可选择在中国香港地域创建。
开启 TDE 加密功能后,若一个账号(UIN)下没有创建过加密表,则在密钥列表中可能无法显示对应密钥信息,若一个账号(UIN)下创建过加密表,则可以看到对应密钥信息。创建加密表的操作请参考 常见问题。
限制条件
实例架构须为通用型或独享型的双节点、三节点。
实例的数据库版本须为 MySQL 5.7、MySQL 8.0。
已开通 KMS 服务。如未开通,可在开通数据加密过程中根据引导开通 KMS。
已授予 KMS 密钥权限。如未授予,可在开通数据加密过程中根据引导进行授权。
操作账号需具有 QcloudAccessForMySQLRole 的权限,如无权限,可在开通数据加密过程中根据引导进行授权。
注意事项
撤销授权关系后,重启会造成 MySQL 数据库不可用。
TDE 加密功能开通后无法关闭。
开启 TDE 加密功能后,用户如果要恢复数据到本地,需要先解密数据。
开启 TDE 加密功能后,可提高静态数据的安全性,但同时会影响访问加密数据库的读写性能,请结合实际情况选择开启 TDE 加密功能。
如果主实例关联只读实例或灾备实例,只需主动开通主实例的 TDE 功能即可,只读实例和灾备实例的数据加密会一并开通。
使用 TDE 功能时,请确保 KMS 密钥处于正常使用状态,否则将无法从 KMS 获取密钥,可能导致迁移、升级等任务无法正常进行。
开启 TDE 加密功能后,会增加 CPU 资源的消耗,约影响5%的性能。
开启 TDE 加密功能后,经过数据库身份验证的应用和用户可以透明地访问应用数据。
开启 TDE 加密功能后,备份压缩效果可能降低。
开启 TDE 加密功能后,MySQL 8.0版本的实例会自动加密,即开启 TDE 加密功能后创建的表都是默认加密的。
操作步骤
开启 TDE 加密功能
1. 登录 MySQL 控制台,在实例列表中,单击实例 ID 或操作列的管理,进入管理页面。
2. 选择数据安全页,单击加密状态后的开关。
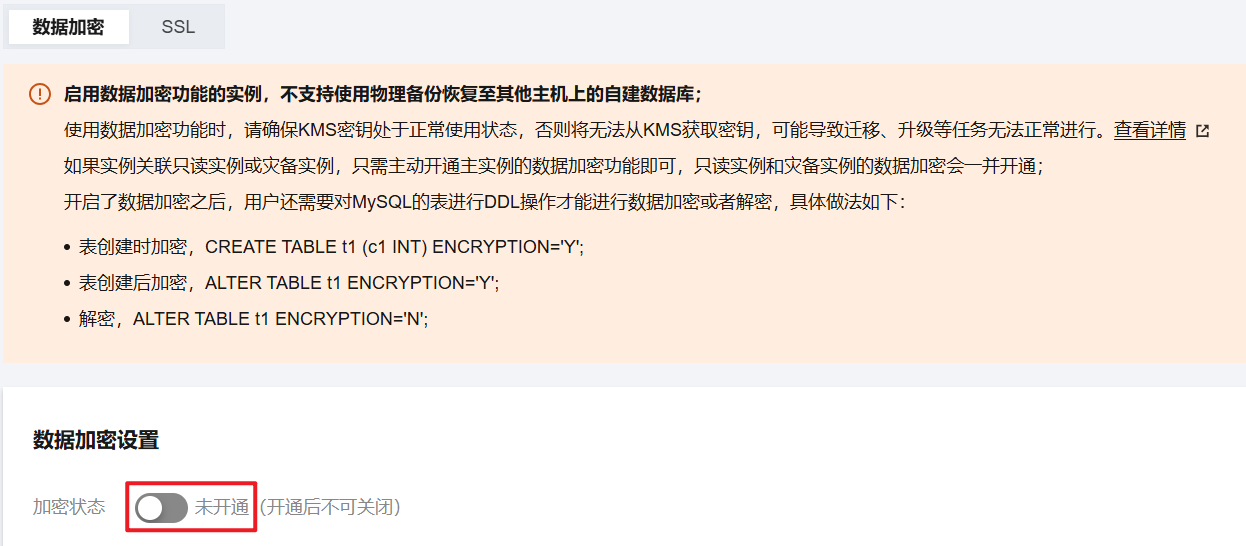
注意:
启用数据加密功能的实例,不支持使用物理备份恢复至其他主机上的自建数据库。
数据加密开通后不可关闭。
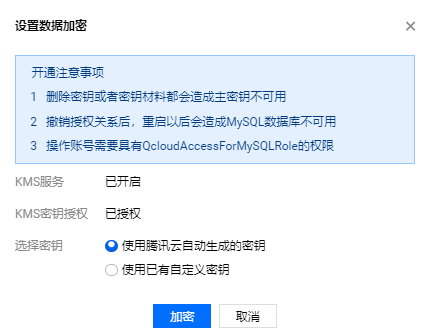
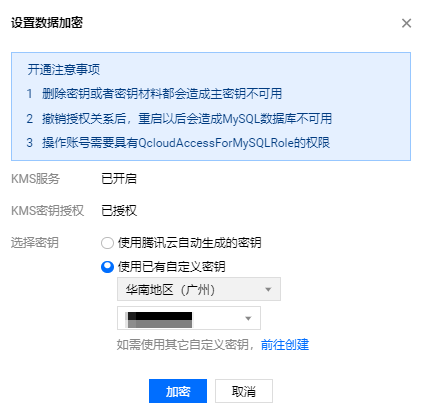
3. 在弹出的对话框,开通 KMS 服务和授予 KMS 密钥权限,选择密钥后,单击加密。
选择使用腾讯云自动生成的密钥时,由腾讯云自动生成密钥。
选择使用已有自定义密钥时,可选择自己创建的密钥。
说明:
加密数据表
开启 TDE 加密功能后,用户需对 MySQL 的表执行如下 DDL 操作才能进行数据加密。
如果您在创建表时对表进行加密,请执行如下命令:
CREATE TABLE t1 (c1 INT) ENCRYPTION='Y';
如果您对已创建的表进行加密,请执行如下命令:
ALTER TABLE t1 ENCRYPTION='Y';
解密数据表
开启 TDE 加密功能后,用户还需要对 MySQL 的表进行如下 DDL 操作才能进行数据解密。
如果您要对加密的表进行解密,请执行如下命令:
ALTER TABLE t1 ENCRYPTION='N';
常见问题
为什么开启 TDE 加密后,密钥列表中无密钥信息?
问题现象
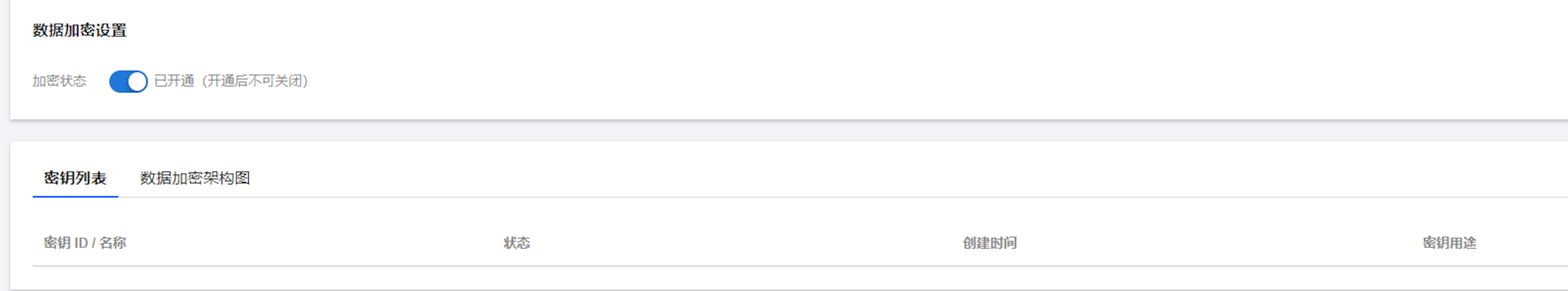
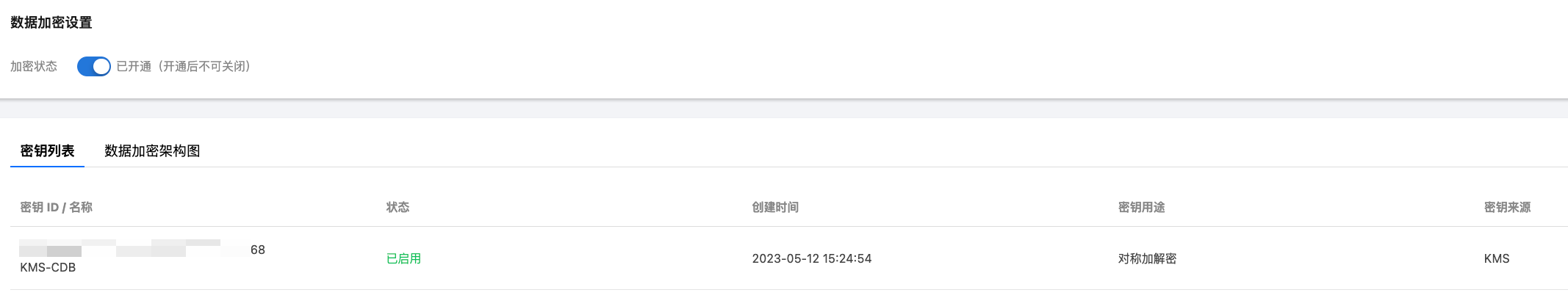
开启 TDE 加密后的正常密钥列表
处理建议
1. 首先查询 KMS 加密状态是否正常,账号是否欠费,云数据库 MySQL 实例和密钥管理系统是否存在到期未付费情况。请确保以上几项都正常后重试。
2. 如果您是首次使用 TDE 加密,在您的账号(UIN)下未创建过加密表,则密钥列表中会没有密钥信息,请参考以下命令,在您的数据实例中创建加密表后重试。
CREATE TABLE `user_test` (`id` bigint(20) NOT NULL AUTO_INCREMENT,`userId` int(11) NOT NULL,`age` int(11) NOT NULL,`name` varchar(64) DEFAULT NULL,`ins_date` varchar(10) DEFAULT NULL,PRIMARY KEY (`id`),KEY `idx_ins_date` (`ins_date`),KEY `idx_userId` (`userId`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 ENCRYPTION='Y';
为什么开启 TDE 加密后,密钥无法使用?
请确认您的 KMS 加密状态是否正常,账号是否欠费,云数据库 MySQL 实例和密钥管理系统是否存在到期未付费情况。由于密钥管理系统(后付费版)已无法创建,新购密钥管理系统仅支持购买预付费版,因此,存量使用密钥管理系统(后付费版)的用户,当 KMS 加密状态异常或账号欠费时,密钥将无法使用,请为账号充值后重试。
文档反馈