本地提权
Download
聚焦模式
字号
本文档将为您介绍如何对提权事件详情进行查看和处理,同时指导您如何创建白名单,用于设置被允许的提权行为。
背景信息
若出现以低权限进入系统,通过某些手段提升权限,获取到高权限的事件,很有可能为黑客的攻击行为,该行为会危害到主机安全。本地提权功能可实时监控您云服务器上的提权事件,并能对提权事件详情进行查看和处理,同时也支持白名单创建功能,用于设置被允许的提权行为。
前提条件
操作步骤
告警列表
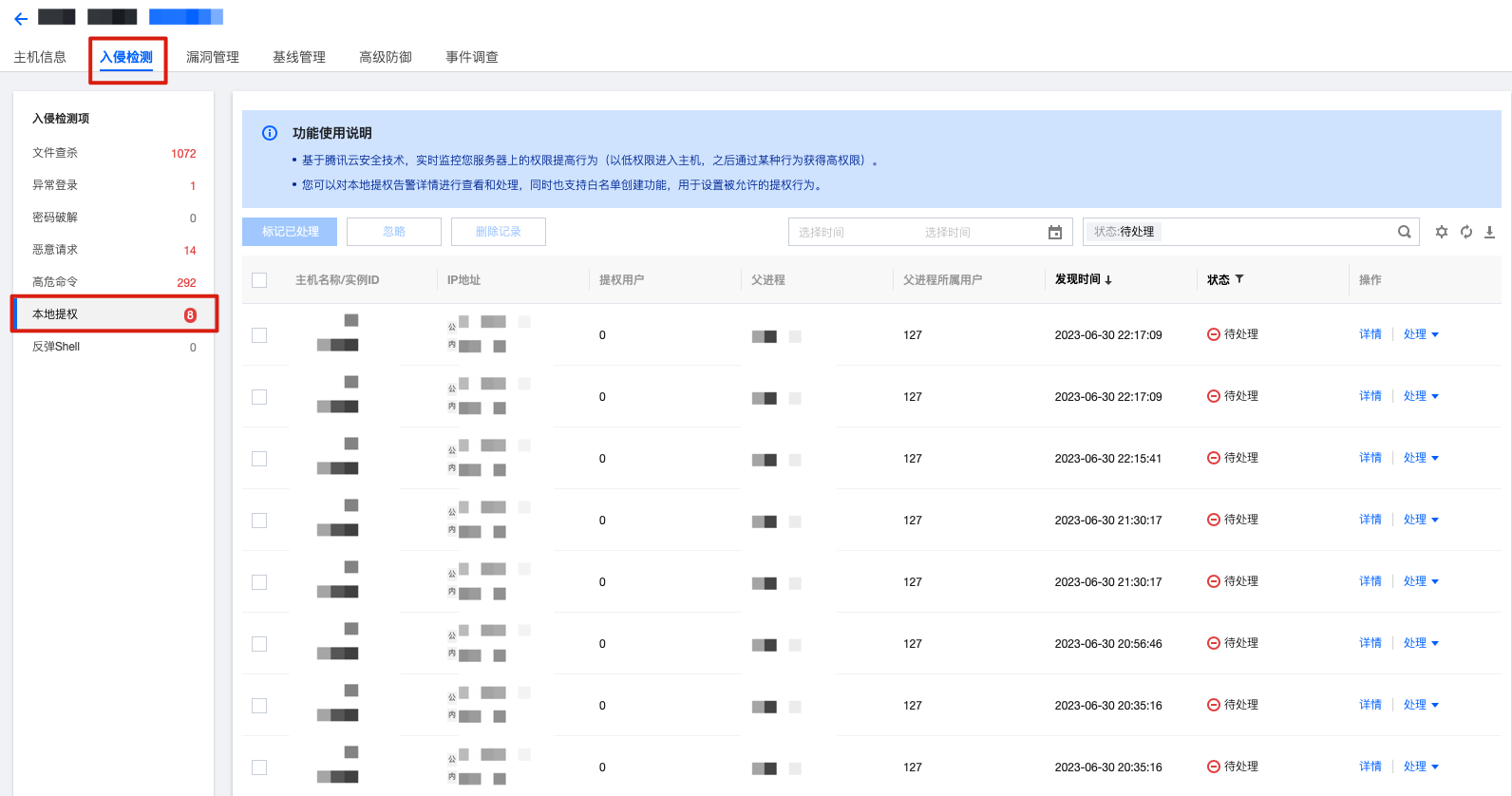
1. 登录 主机安全控制台,在左侧导航栏选择入侵检测 > 本地提权,进入本地提权的告警列表标签页。
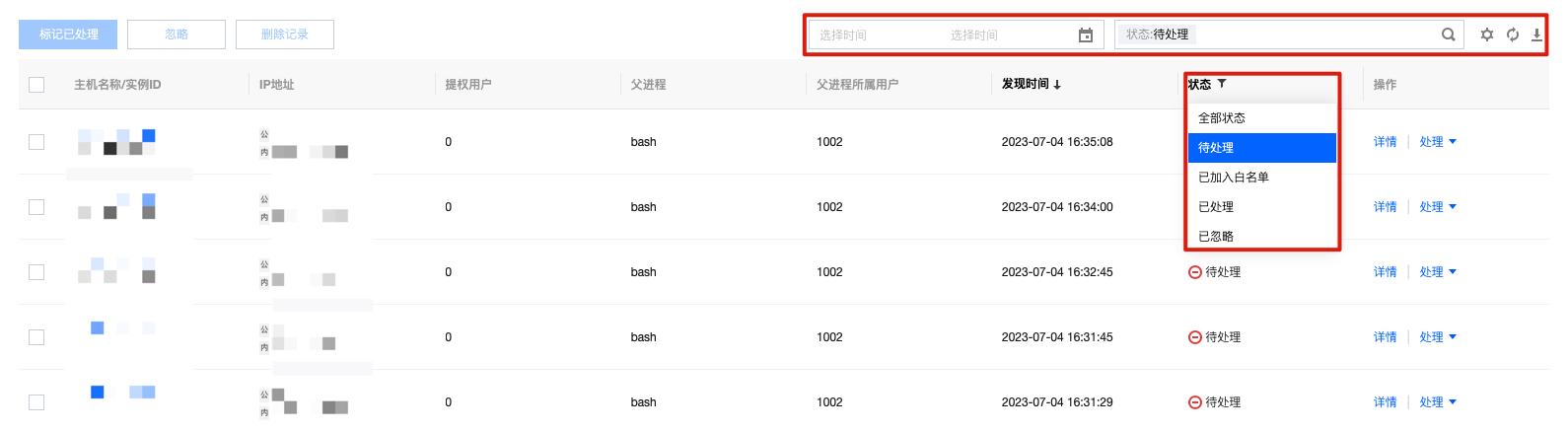
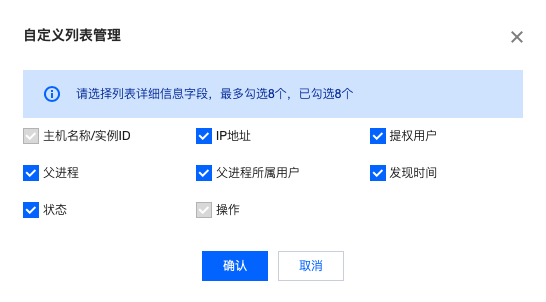
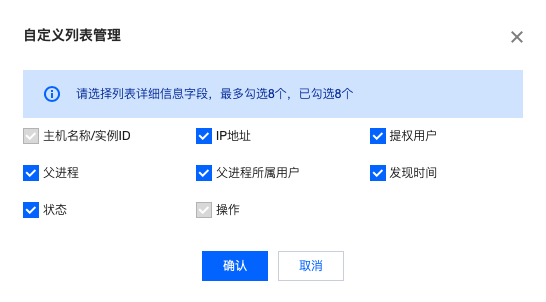
2. 在本地提权的告警列表标签页,可查看本地提权告警事件列表,并进行相关操作。可查看发生提权事件的主机名称/实例 ID,IP 地址、提权用户、父进程、父进程所属用户、发现时间、状态、操作(详情 | 处理)共8个字段,展示列表详情信息可进行自定义。
筛选/查询:本地提权告警列表支持选择日期查看相应的告警信息,支持按关键字及标签查询(多个关键字用竖线 “|” 分隔,多个过滤标签用回车键分隔)事件,同时支持按状态筛选事件。
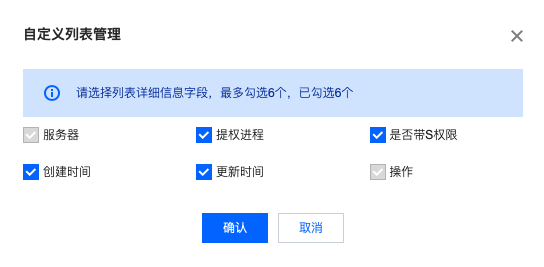
自定义设置列表字段:在本地提权告警列表上方,单击

事件导出:在本地提权告警列表上方,单击

详情 > 告警详情:在本地提权告警列表的右侧操作栏,单击详情选择告警详情标签页,可查看告警详情。

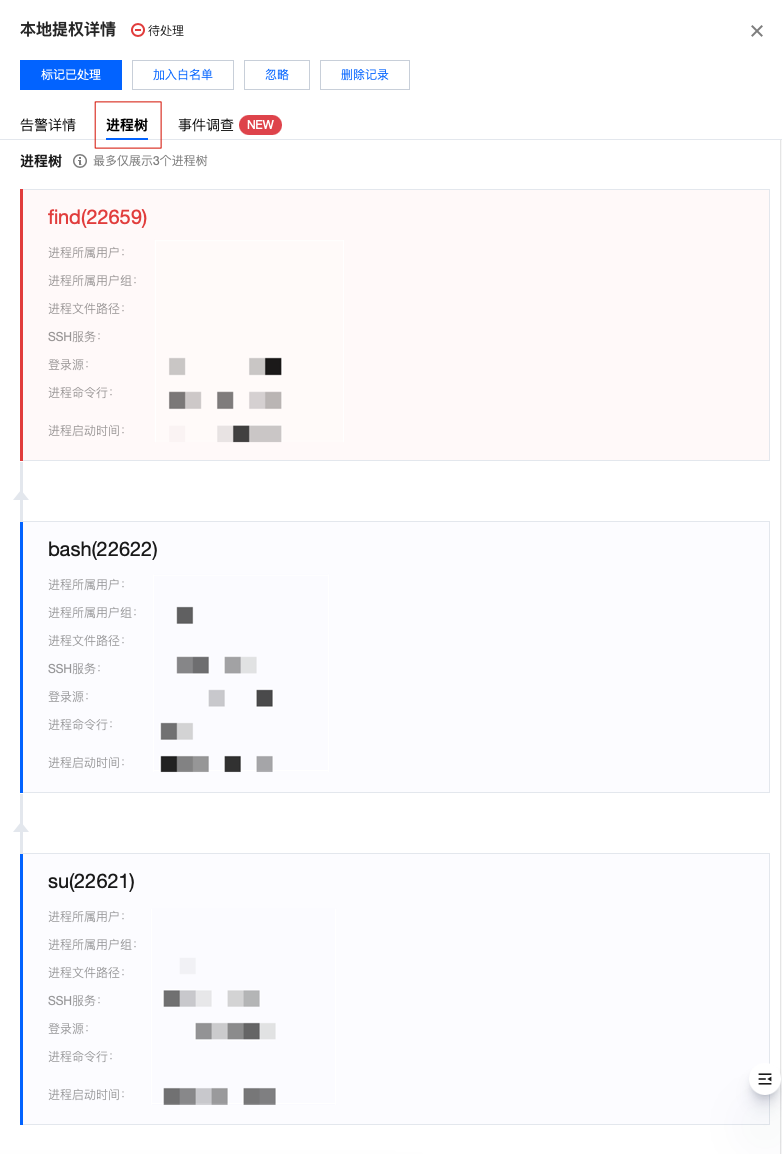
详情 > 进程树:在本地提权告警列表的右侧操作栏,单击详情选择进程树标签页,可查看以时间倒序排列的三个最新进程详情。
详情 > 事件调查:在本地提权告警列表的右侧操作栏,单击详情选择事件调查标签页,可进入对应主机列表的 事件调查。
说明
Windows 机器暂不支持事件调查功能。
仅旗舰版支持事件调查功能。
标记已处理:支持单选或多选本地提权告警信息,人工对该告警进行处理,处理后可将告警标记为已处理。


加入白名单:
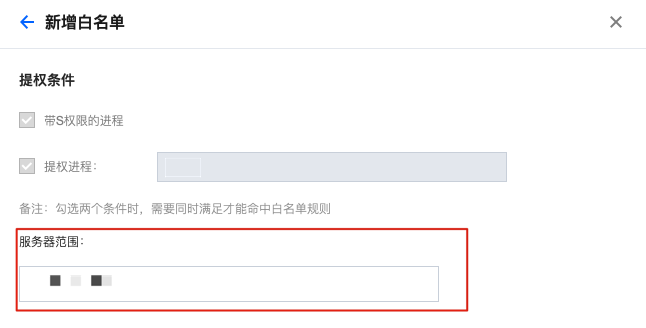
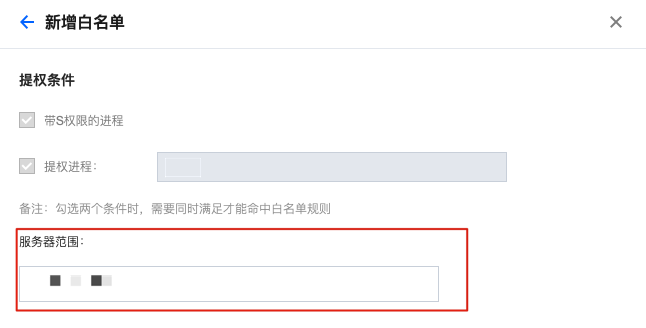
2.1.1 如需将本地提权告警事件加入白名单,可在告警信息列表的右侧操作栏,单击处理 > 加入白名单,或在详情页单击加入白名单。


2.1.2 在新增白名单页面,填写服务器范围后单击确定,即可将该本地提权告警加入白名单。
忽略:支持单选或多选本地提权告警信息,仅将本次选中的告警进行忽略,若再有相同情况发生依然会进行告警。
删除记录(慎重操作):支持单选或多选本地提权告警信息,删除选中的告警记录,控制台将不再显示且无法恢复记录。

3. 单击本地提权告警的主机名称/实例ID,可查看该主机列表入侵检测标签页详情。
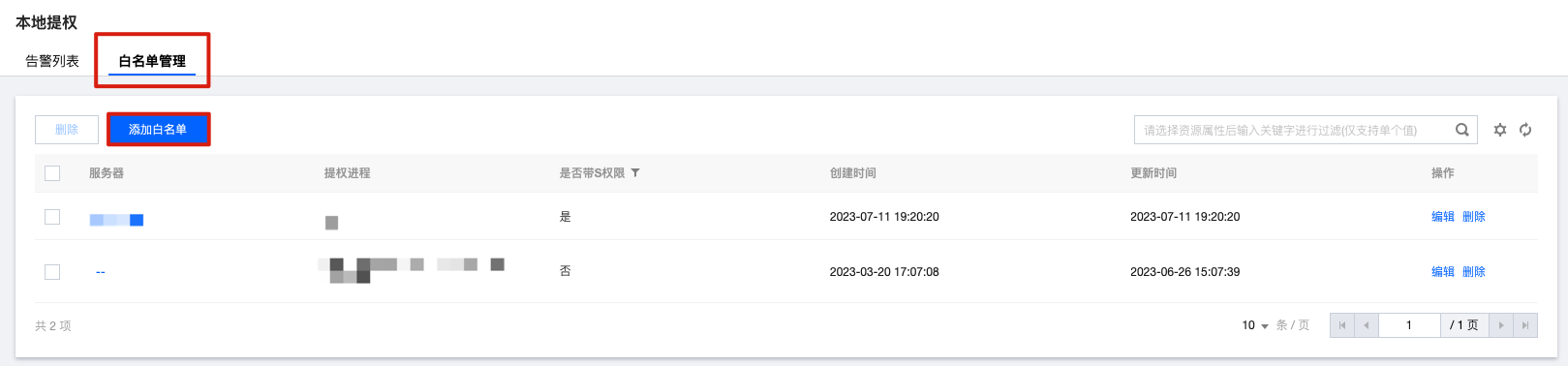
白名单管理
本地提权功能支持添加白名单,通过设置白名单提权条件,将满足条件的事件标记为白名单。
1. 登录 主机安全控制台,在左侧导航栏,选择入侵检测 > 本地提权。
Log in to the Host Security Console, and in the left navigation bar, select Intrusion Detection > Local Privilege Escalation.
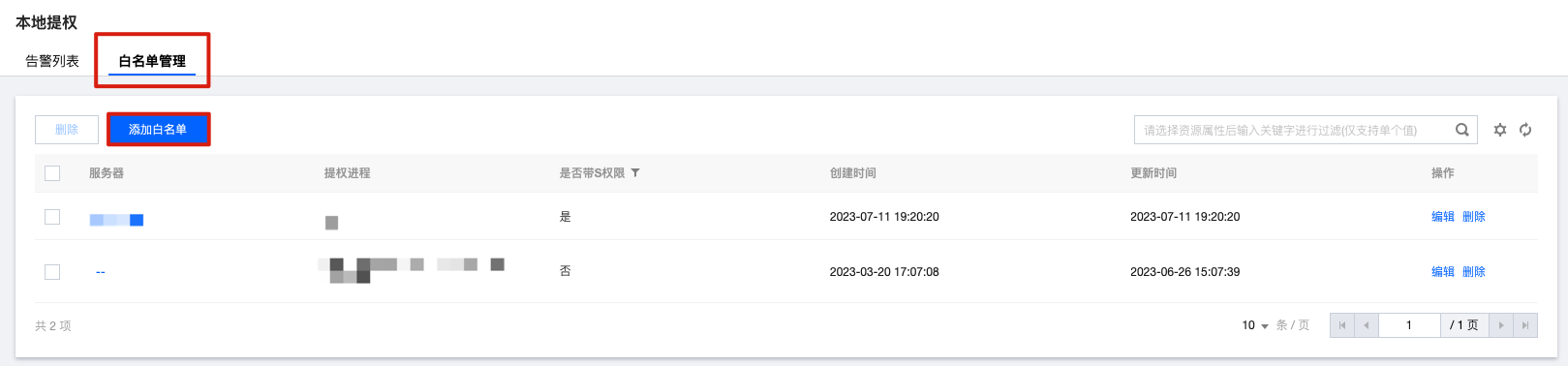
2. 在本地提权页面,单击白名单管理 > 添加白名单。
3. 在新增白名单页面,设置提权条件,包括:带 S 权限的进程、自定义提权进程(支持多个进程名,以英文逗号分隔,例如 123.exe,test.exe),同时选择该条件覆盖的服务器范围,单击确定。
注意
S 权限: 设置使文件在执行阶段具有文件所有者的权限,相当于临时拥有文件所有者的身份。
勾选两个条件时,需要同时满足才能命中白名单。
若服务器范围选择全部服务器,将对用户 APPID 下所有服务器添加信任该白名单条件,请谨慎操作。

4. 设置完成后,可在白名单管理列表查看该条件,且在事件列表满足该条件的事件即会被标记为白名单事件。
5. 在白名单管理页面,可对白名单进行筛选删除等操作。
筛选:已配置的白名单支持按关键字及标签查询(多个关键字用竖线 “|” 分隔,多个过滤标签用回车键分隔)筛选,同时支持按是否带 S 权限进行筛选。


自定义设置列表字段:在白名单列表上方,单击

编辑:在目标白名单的右侧操作栏,单击编辑,可对已创建的白名单进行编辑。
删除:在白名单列表中,支持单选或多选已配置的白名单进行删除。


文档反馈