恶意文件处理
Download
聚焦模式
字号
当用户腾讯云账号下的服务器被检出存在恶意文件,主机安全若发现该文件没有命中文件白名单,则会触发实时告警。
处理步骤
在收到恶意文件告警后,请按照下列步骤进行操作:
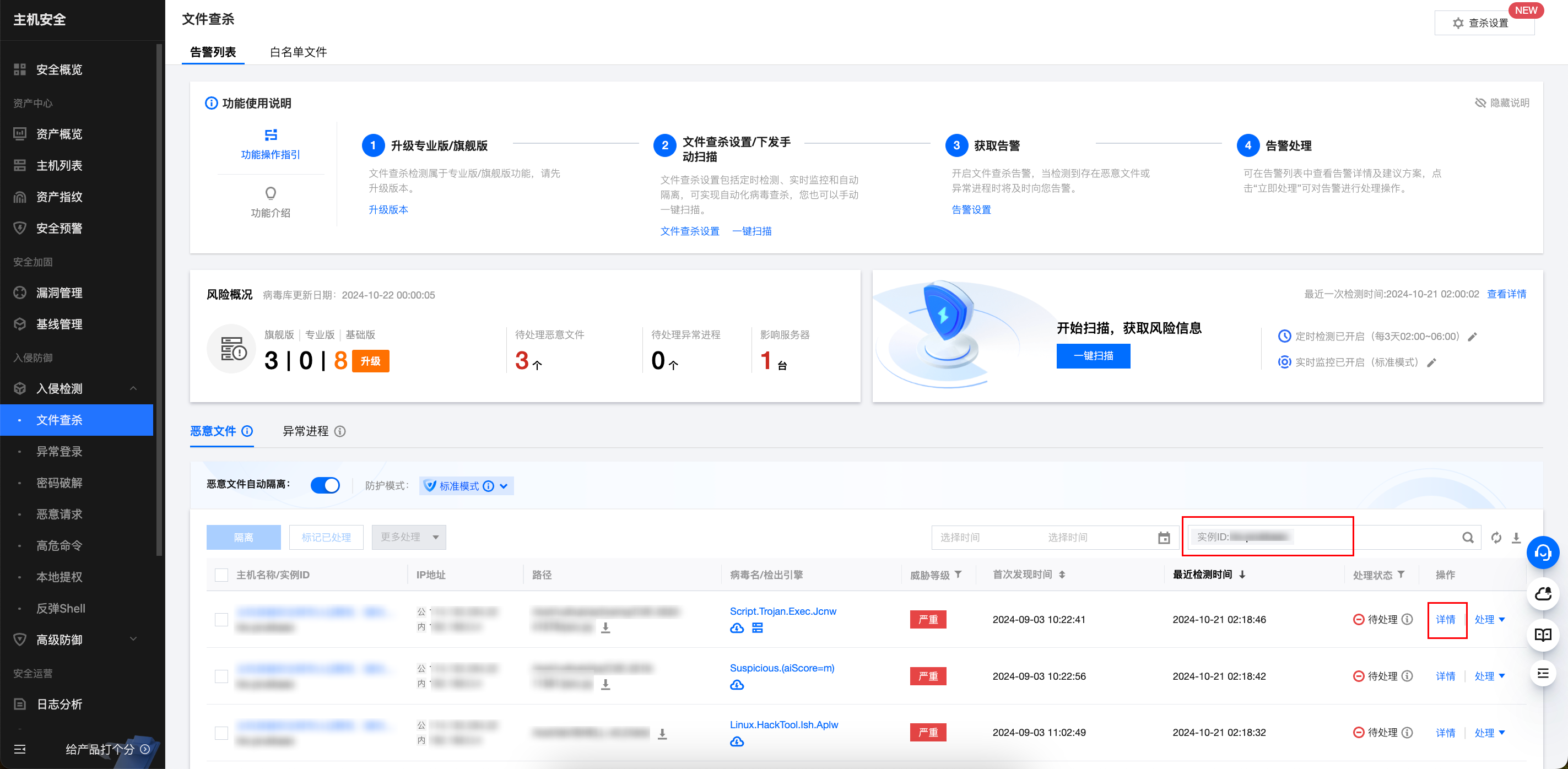
1. 登录 主机安全控制台,在左侧导航栏,选择入侵检测 > 文件查杀。
2. 在文件查杀页面,通过告警资产 ID 进行搜索,定位到具体告警并单击详情。
3. 查看告警详情后,请确认该恶意文件是否误报,若是误报,请执行步骤4,若不是误报,请执行步骤5。
说明:
该恶意文件是否误报,可结合以下几种方式判定:
联系业务团队判断该文件是否是业务正常运行所需文件。
查询威胁情报,判断该文件是否被外网标记为恶意样本。
该文件行为是否导致进一步触发更多告警。
联系 安全专家服务。
4. 明确是误报,请将该文件加入白名单,后续再次检出此文件将被忽略,不会产生告警,并联系我们 反馈误报。

5. 明确不是误报,请参考告警详情中的修复建议进行处理。

可单击隔离,对该文件进行隔离并结束相关进程的操作,该告警处理状态将变为“已隔离”。
可登录该主机,找到对应文件,手动进行删除或隔离并结束相关进程,然后在控制台对该告警标记已处理,该告警处理状态将变为“已处理”。
6. 在文件查杀页面,单击右上角的查杀设置,建议开启自动隔离开关,检出恶意文件则立即自动隔离。

说明:
并非所有检出的恶意文件均能被自动隔离,部分恶意文件仍需用户手动确认隔离,建议检查文件查杀中的告警列表,确保已全部处理。
若出现误隔离,请在已隔离列表中对文件进行恢复。
开启或关闭自动隔离,均需要进行配置,实际生效存在几分钟延迟。
热点问题
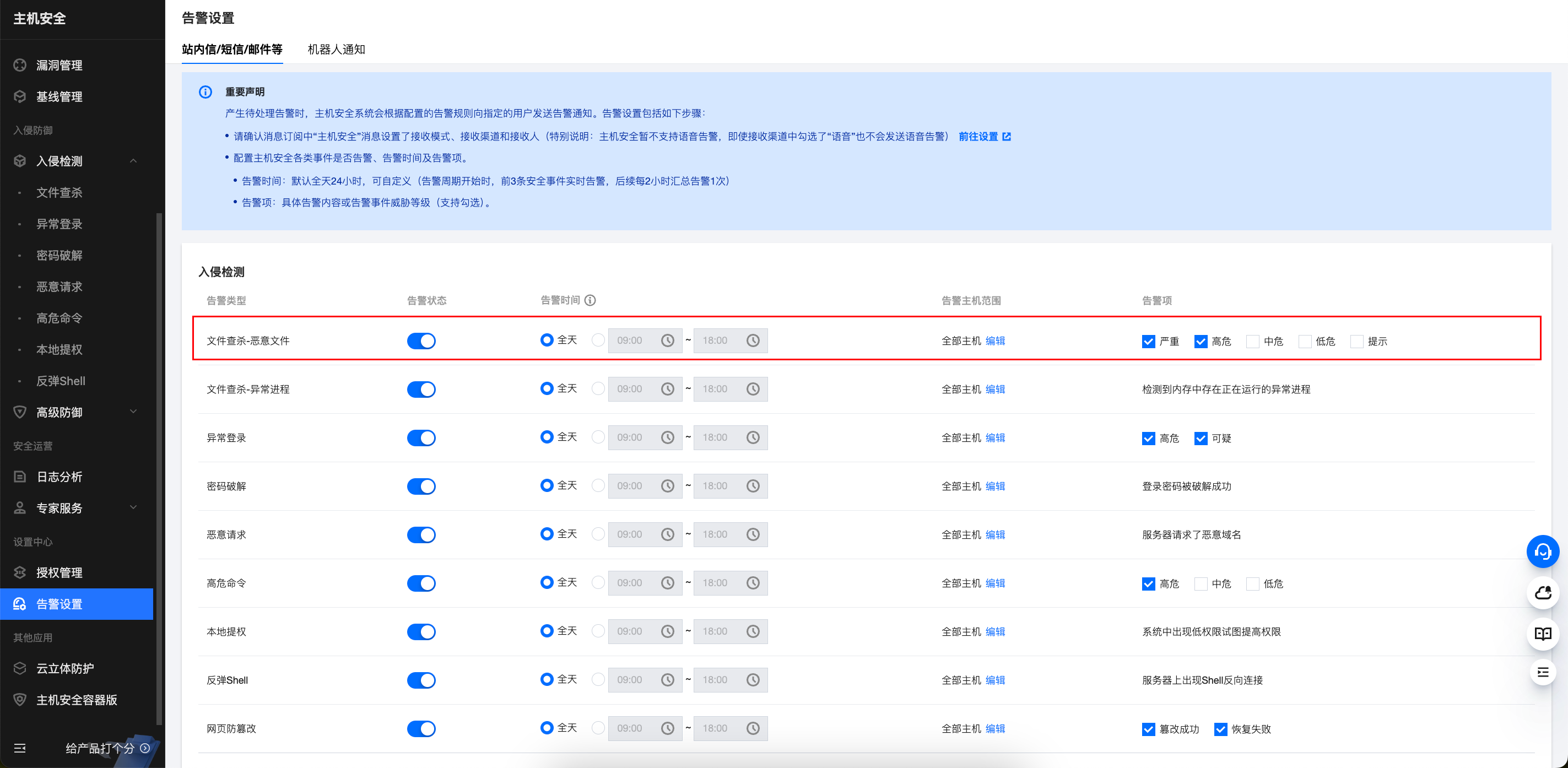
恶意文件在哪里配置告警?
恶意文件如何设置定期检测?


若文件已被删除,再次对进行恶意文件扫描,原告警处理状态会变成什么?
原告警处理状态将变为“已清理”。
文档反馈