- Updates and Announcements
- Product Introduction
- New/Legacy Anti-DDoS Advanced Version Differences
- Comparison of Anti-DDoS Protection Schemes
- Purchase Guide
- Getting Started
- Operation Guide
- Best Practice
- API Documentation
- FAQs
- Troubleshooting
- Anti-DDoS Advanced (Global Enterprise Edition)
- Legacy Anti-DDoS Advanced (Legacy)
- Service Level Agreement
- Contact Us
- Glossary
- Updates and Announcements
- Product Introduction
- New/Legacy Anti-DDoS Advanced Version Differences
- Comparison of Anti-DDoS Protection Schemes
- Purchase Guide
- Getting Started
- Operation Guide
- Best Practice
- API Documentation
- FAQs
- Troubleshooting
- Anti-DDoS Advanced (Global Enterprise Edition)
- Legacy Anti-DDoS Advanced (Legacy)
- Service Level Agreement
- Contact Us
- Glossary
Anti-DDoS supports blocking the source traffic accessing Anti-DDoS instances based on specified protocols, such as ICMP, TCP, UDP, and other protocols. After the configuration is completed, all matched access requests will be directly blocked. Due to the connectionless feature of UDP protocol (unlike TCP, which requires a three-way handshake process), it has natural security vulnerabilities. If you do not have UDP businesses, we recommend blocking the UDP protocol.
Prerequisites
- You have purchased an Anti-DDoS Advanced instance and set the target to protect.
Directions
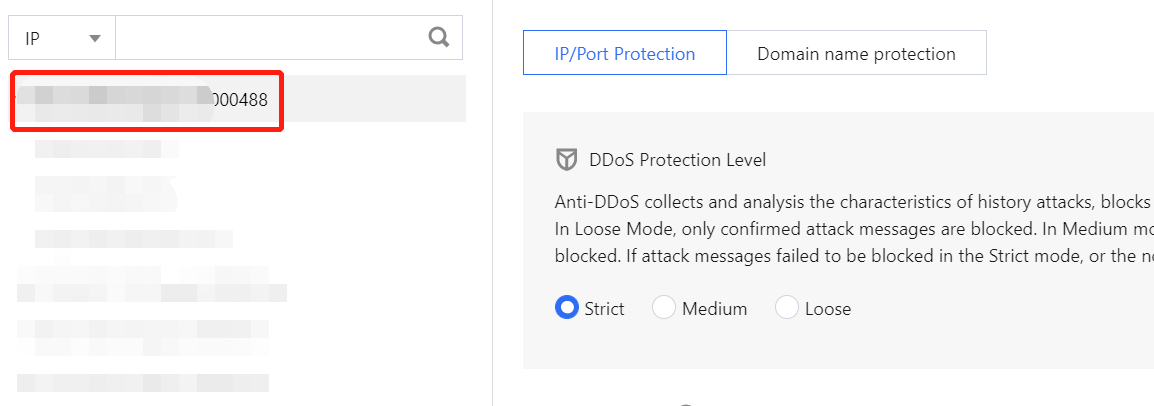
Log in to the Anti-DDoS console and select Anti-DDoS Advanced (New) > Configurations on the left sidebar. Open the DDoS Protection tab.
Select an Anti-DDoS Advanced instance ID in the list on the left, such as "bgpip-xxxxxx".
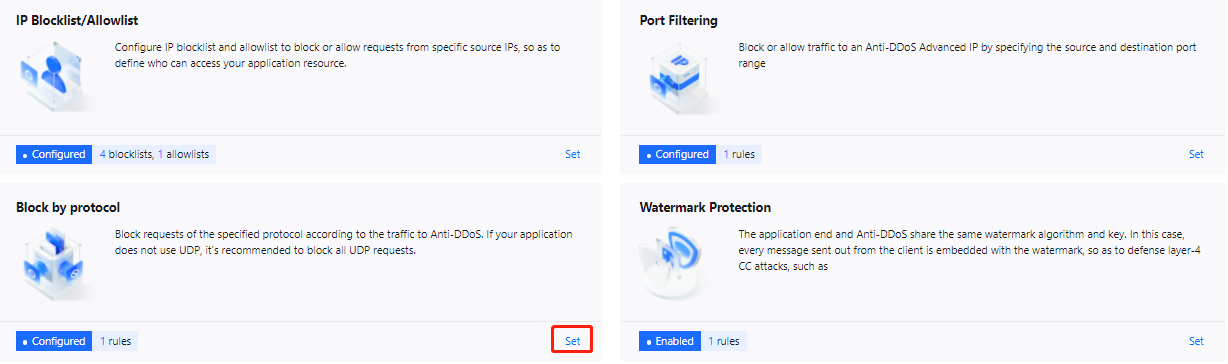
Click Set in the "Protocol blocking" section.
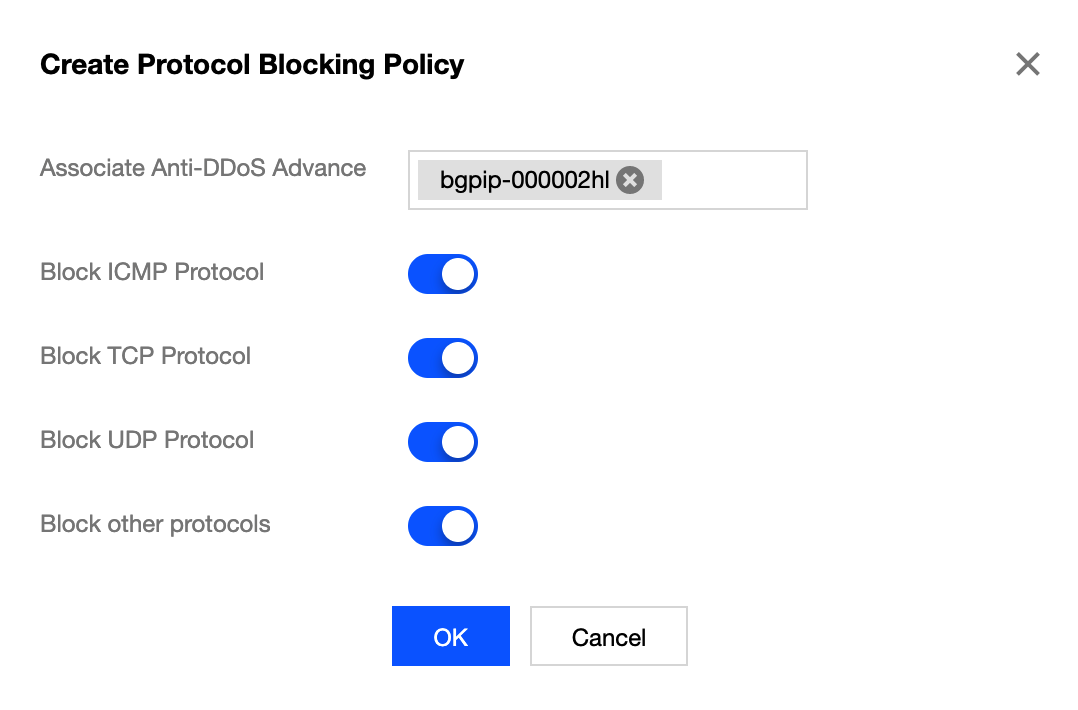
Click Create.
Note:The Create button appears only when you use this feature for the first time.
In the pop-up window, click the button on the right of a protocol, and click Confirm.
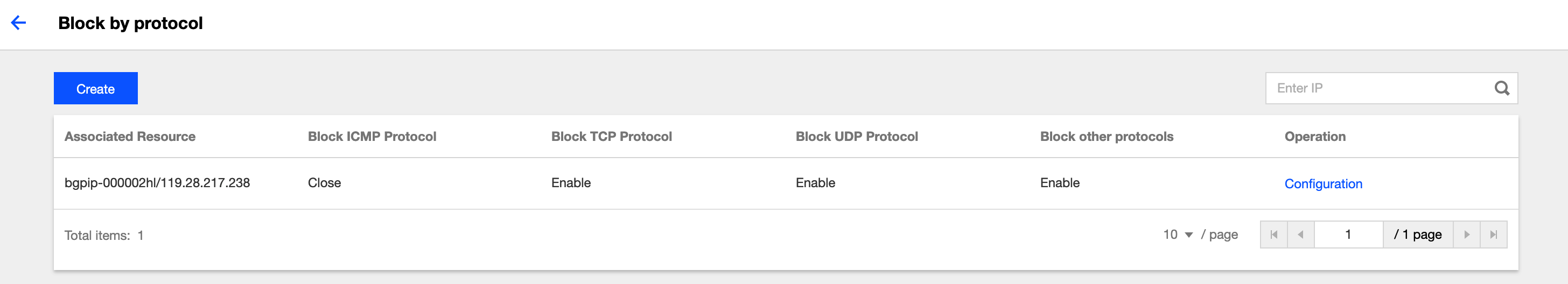
After the rule is created, it is added to the list. You can click Configuration on the right of the rule to modify it.

 Yes
Yes
 No
No
Was this page helpful?