Resource-Level Authentication Guide
Download
Focus Mode
Font Size
GData Lake Compute (DLC) supports resource-level authentication based on the Cloud Access Management (CAM) tags. You can use tags to classify and manage the existing DLC engine resources and engine-related API permissions, enabling multidimensional classification management and fine-grained authorization of the resources.
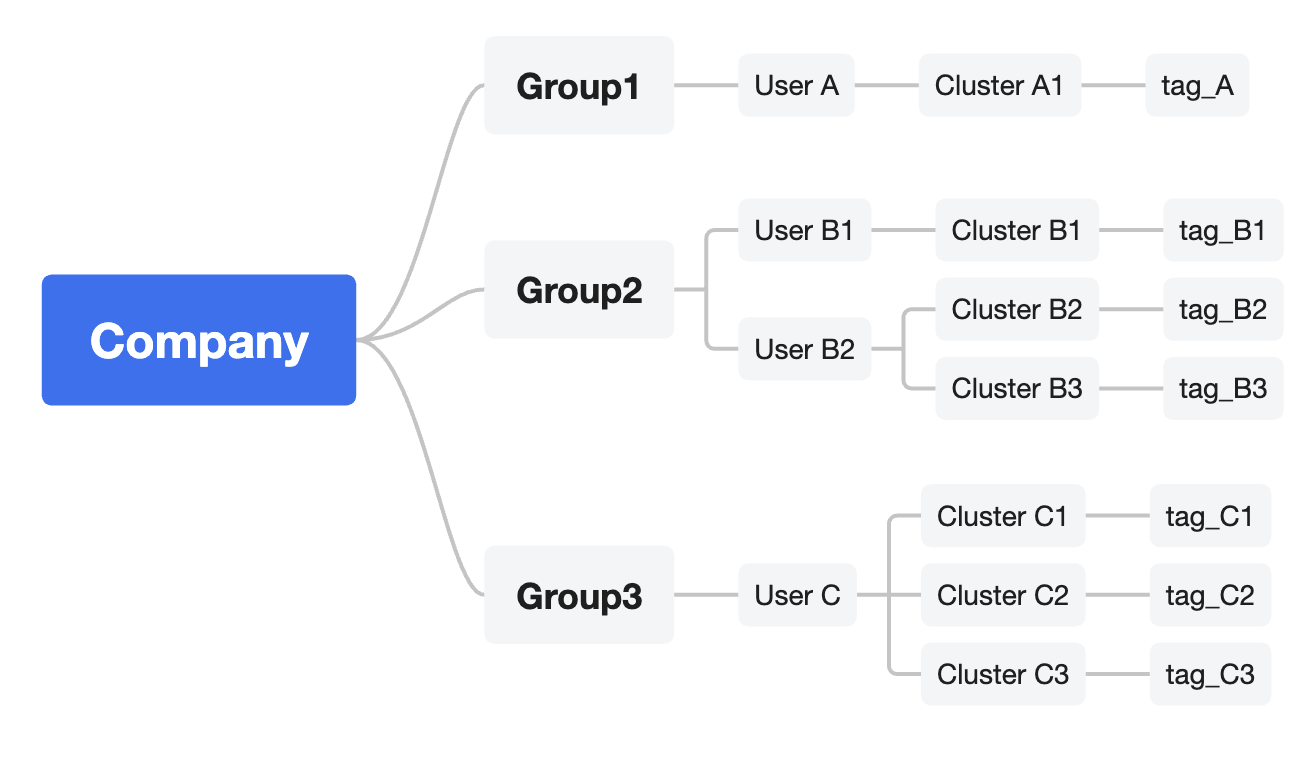
You can plan tags based on your company's departments or organizational structure. For example, in the diagram below, departments A, B, and C are each assigned corresponding usernames, clusters, and tags. For details about tag-related operations, refer to Tag.
Based on Tencent Cloud Tag, you can quickly achieve the following results when managing DLC engine resources and engine-related API permissions:
1. Authorize in batches: Grant sub-users the permissions on all resources under a specific tag.
As shown in the diagram above, for all users belonging to the Department A, access to DLC engine resources tagged with tag_A and the corresponding TencentCloud API permissions are granted in batches based on resource_tag.
For details about related operations, refer to Scenario 1: Granting Resource Permissions Under a Specific Tag Key.
2. Resource control: Enforce the binding of fixed tag key-value pairs during the DLC resource creation.
If you want to ensure that the Department A users tag their DLC engine resources with the Department A tag during the resource creation, avoiding untagged public resources and minimizing resource waste, you can enable the forced tagging feature.
For details about related operations, refer to Scenario 2: Enforcing Tags During the DLC Engine Resource Creation.
Note:
You can flexibly select and configure one or more of the 2 authentication configuration methods mentioned above based on your business scenario needs.
Scenario 1: Granting Resource Permissions Under a Specific Tag Key
Scenarios
Your company has purchased multiple DLC computing engine resources, which are grouped and managed by tags, and you want to grant the permissions on all resources associated with a specific tag key (resource_tag).
The following conditions apply:
The enterprise account CompanyExample has a sub-account User A.
The enterprise account CompanyExample has a tag key Dept_A.
The enterprise account CompanyExample wants to grant the sub-account User A the permissions on all DLC engine resources and the corresponding TencentCloud API permissions under the Dept_A tag key.
Operation Steps
1. Creating Tags and Assigning Tags to Engines
Note:
The following steps will use the tag tag_A as an example.
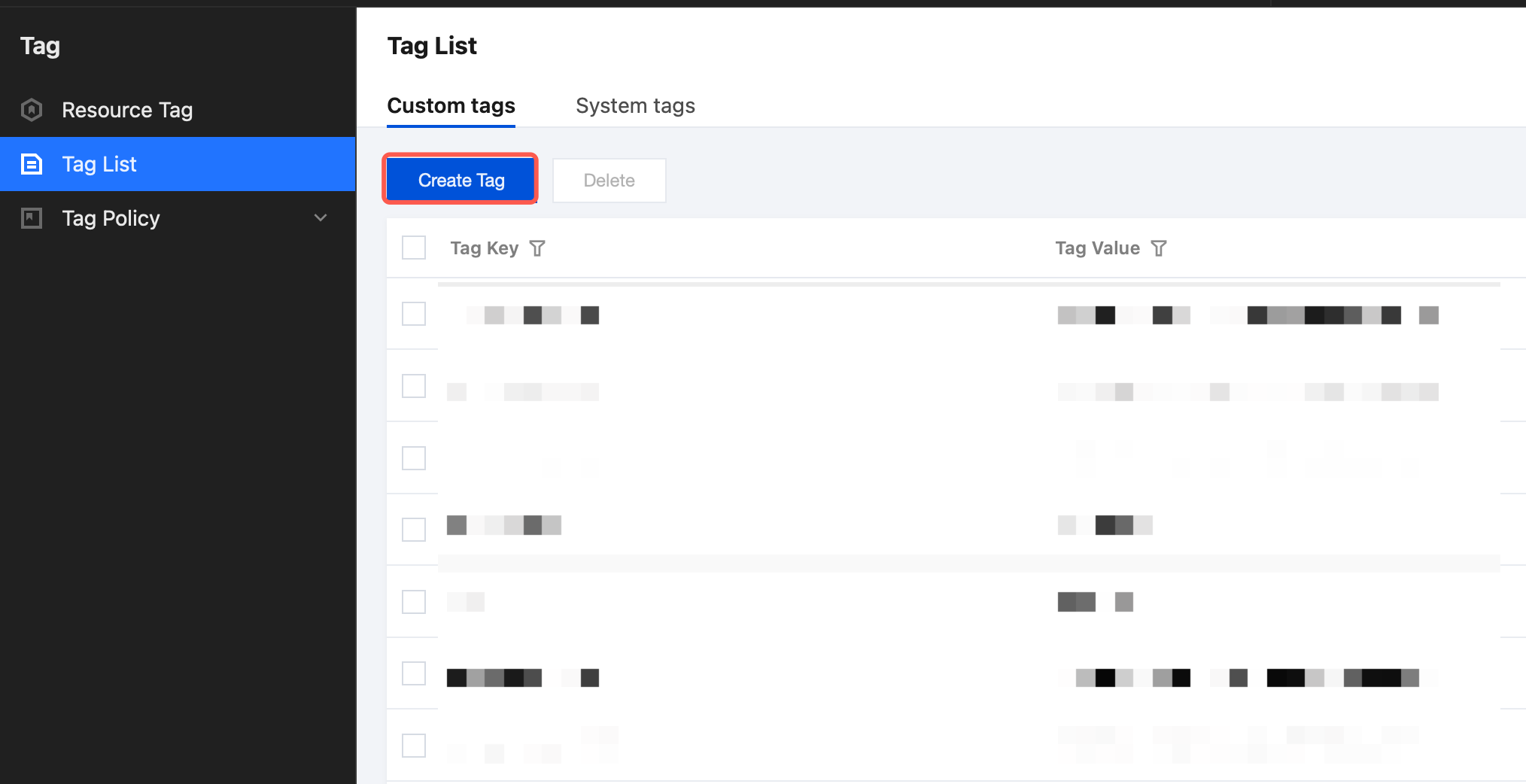
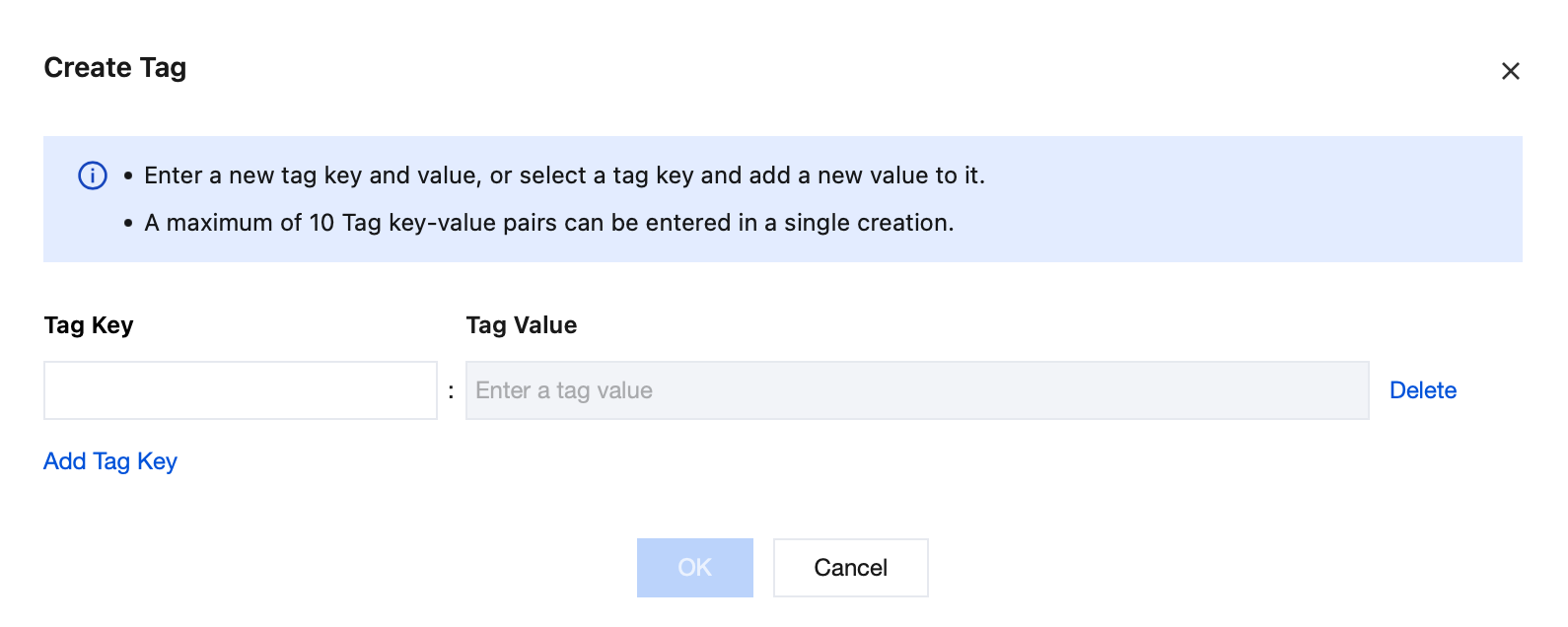
Enter the tag key and tag value, then click Confirm to create the tag.
Go to the DLC console, access the Engine List page, click the resource name to enter the resource details page, and click the Edit button. The tag editing window will pop up, where you can select a tag to bind. For detailed steps on binding tags to engines, refer to Associating Tag with Private Engine Resource.
2. Creating Custom Policies
Create a Custom Policy Policy_Dept_A1.
Go to the CAM Policy page and click Create Custom Policy.
Select Tag-based Authorization.
In the Tag Policy Generator, select Dept_A for the assigned user field, leave the user group field blank, and select the corresponding tag key and tag value defined before. Add services and operations as needed, then click Next.
Create the Policy_Dept_A1 policy. In the policy content, update the "action" and "resource" fields with the following content, and click Complete.
{"effect": "allow","action": ["dlc:CreateTask","dlc:CreateSparkApp"],"resource": ["*"],"condition": {"for_any_value:string_equal": {"qcs:resource_tag": ["tag_A&Dept_A","tag_B&Dept_B","tag_C&Dept_C","tag_D&Dept_D"]}}}
Note:
The content of the resource field should be entered based on the actual resources. For entry rules, refer to Resource Description Method.
3. Granting and Verifying Sub-user Permissions
On the User List page, locate the sub-user to whom you want to grant permissions, and click the Authorize button on the right. To create sub-users, refer to Creating Sub-user.
Select Policy_Dept_A1 and click Complete.
Log in as a sub-user to perform the verification. The sub-user will only be able to use and manage the test_A engine resources using the tag_A tag.
Scenario 2: Enforcing Tags During the DLC Engine Resource Creation
Scenarios
You want to ensure that your sub-account can only bind permissions to a specific tag key-value when purchasing DLC engine resources. The following conditions apply:
The enterprise account CompanyExample has a sub-account User A.
The enterprise account CompanyExample has a tag key-value Dept_A.
The enterprise account CompanyExample enforces that the sub-account User A should apply the Dept_A tag key-value when creating DLC engine resources.
Operation Steps
1. Log in to the CAM console using the enterprise account CompanyExample.
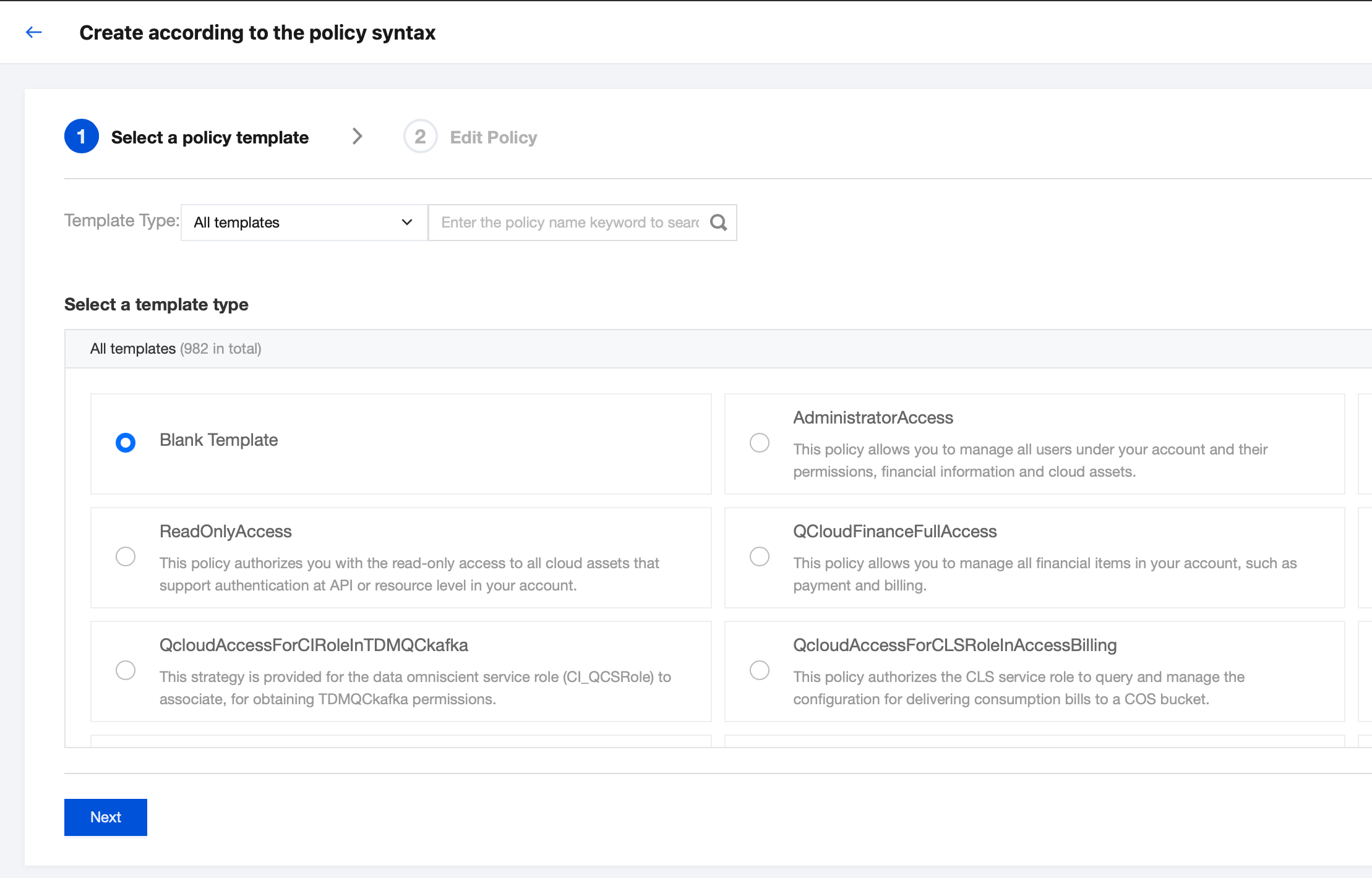
2. On the Policy page, click Create Custom Policy > Create by Policy Syntax.
3. In the Selecting Template Type section, select Blank Template, click Next, and go to the policy editing page.
4. On the policy editing page, enter the following content:
Policy name: By default, the name will be policygen-current date. It is recommended that you define a unique and meaningful policy name, such as Developer-request_tag.
Description: This is optional, and you can add a custom description.
Policy content: Copy the following content and enter the required information.
{"version": "2.0","statement": [{"effect": "allow","action": "dlc:CreateDataEngine","resource": "*","condition": {"for_any_value:string_equal": {"qcs:request_tag": ["Dept_A"]}}},{"effect": "allow","action": "dlc:*","resource": "*","condition": {"for_any_value:string_equal": {"qcs:resource_tag": ["Dept_A"]}}}]}
Note:
Control via qcs:resource_tag: Allow access to all resources bound with the Dept_A tag.
Control via qcs:request_tag: The Dept_A tag should be bound during the resource creation for the operation to succeed.
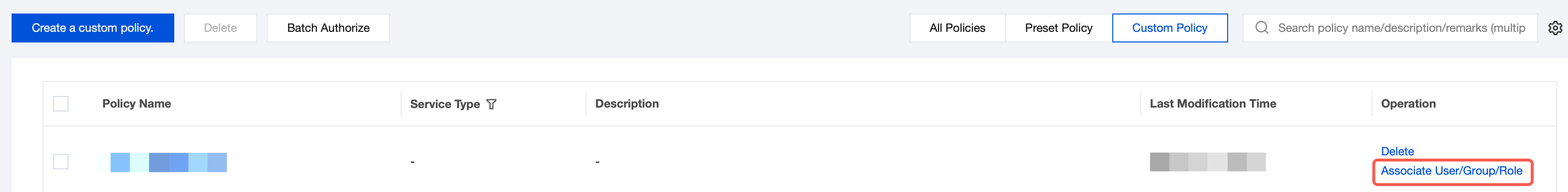
5. Click Complete to finish creating the policy. The created policy will be displayed on the Policy List page.
6. Search for the policy you just created in the policy list, and click Associate Users/User Groups/Roles in the operation column on the right.
7. In the Associating Users/User Groups/Roles pop-up window, search for and select the sub-account User A, and click OK to complete the authorization. The sub-account User A will have the permission to only bind the Dept_A tag key-value.
8. Log in as the sub-account User A. If no tag is set or if the tag is not set to Dept_A, any attempts to purchase DLC computing engines will fail.
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback