Monitoring Rules Configuration
Download
Focus Mode
Font Size
The monitoring rules for core file monitoring are divided into system rules and custom rules. System rules are configurations set by Tencent CWPP operation experts and algorithm experts through multi-model refinement, suitable for most tamper-proof user configuration monitoring requirements. You can also create custom rules based on your business needs. Custom rules support editing, copying, and deleting.
Note:
Core file monitoring is a feature of Ultimate Edition of CWPP. It is recommended to upgrade to Ultimate edition to protect CWPP.
Currently, core file monitoring is only available on Linux operating systems with kernel versions 3.10 and above.
Adding Rules
1. Log in to the CWPP console. In the left sidebar, choose Cyber Defense > Corefile Monitor > Configure monitoring rules.
2. On the configure monitoring rules page, click Add Rule at the top left.
3. On the add rule page, configure the basic settings, rule content settings, and effective server range parameter in sequence.
Basic information
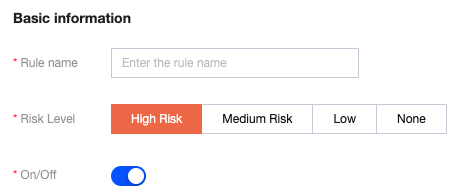
Parameter Description:
Rule Name: Custom name.
Risk Level: Depending on actual needs, you can select high-risk, medium-risk, low-risk, or none.
Enable/Disable: You can enable or disable this new rule.
Rule content settings: Click Add rule. You can add multiple lines, up to 20 lines.
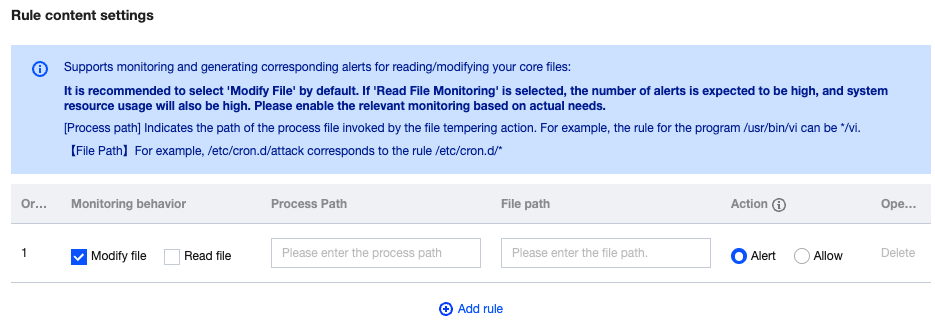
Parameter Description:
Monitoring Behavior: Modify file/Read file.
Process Path: The file path of the process initiating the file tampering action, such as the program /usr/bin/vi, with a corresponding rule that could be */vi.
File Path: For example, /etc/cron.d/attack corresponds to a rule that could be /etc/cron.d/*.
Action: An alarm refers to the automatic generation of an alarm event in response to file system changes, with detailed event logging. Allowing refers to the operation of allowing file system change events, also with detailed event logging.
Note:
When the alarm and allowing respectively apply to the process path or the accessed file path, and there is an overlap in the effective servers, the overlapping servers will not generate alarms (meaning the allowing takes precedence).
Effective host range: You can select all servers or selected servers based on actual needs.
4. After the configuration is completed, click Save.
Managing Rules
Editing Rules
1. On the core file monitor > Configure monitoring rules page, choose the required rule and click Edit in the action bar.
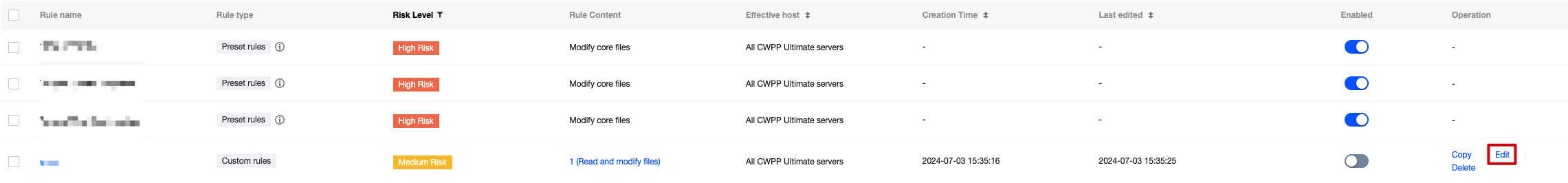
2. On the edit rule page, modify the relevant parameters and click Save.
Copying Rules
1. On the core file monitor > Configure monitoring rules page, choose the required rule and click Copy in the action bar.
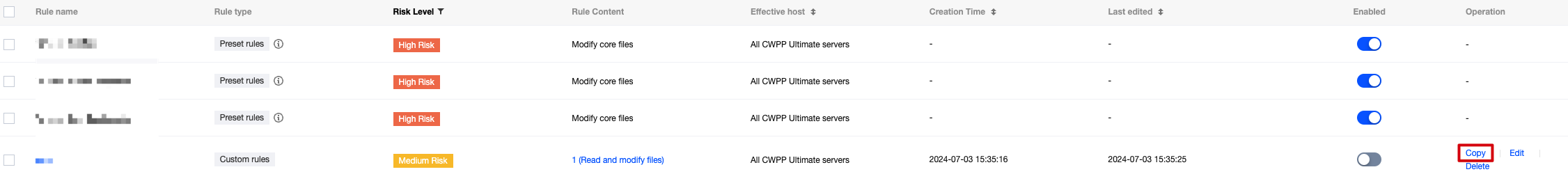
2. On the copy rule page, modify the relevant parameters and click Save.
Deleting Rules
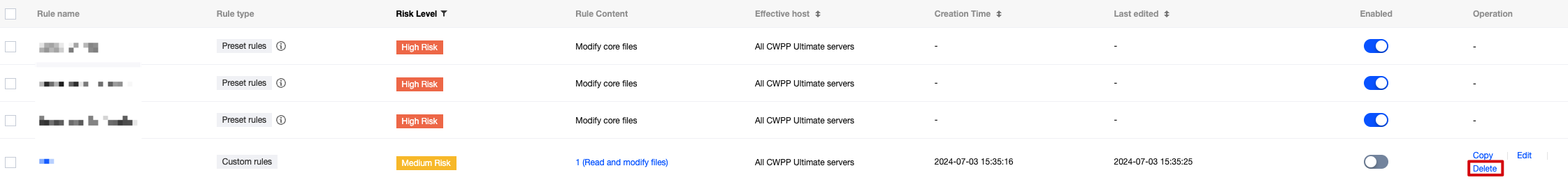
1. On the core file monitor > Configure monitoring rules page, single rule or batches of rules can be deleted as follows.
Single: Choose a single rule, and click Delete in the action bar. Then the Confirm Deletion dialog box pops up.
Batch: Select the required rules, and click Delete. Then the Confirm Deletion dialog box pops up.
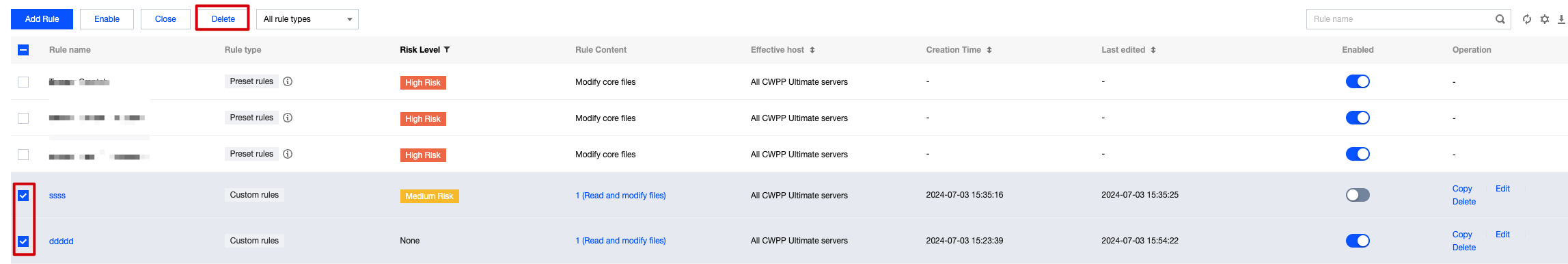
2. In the Confirm Deletion dialog box, click Confirm to complete the deletion of the rules.
Note:
After deletion, the rules cannot be recovered. Proceed with caution.
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback