异常登录
Download
聚焦模式
字号
本文将为您介绍异常登录的功能和操作。
概述
当检测到存在不满足白名单(常用来源 IP、常用用户名、常用登录地、常用登录时间)的服务器登录行为,将产生异常登录告警。若异常登录来源 IP 属于境外 IP(含中国港澳台地区)或威胁情报中的恶意 IP,将被标记为“高危”,反之则标记为“可疑”。
限制说明
已安装主机安全客户端的主机(客户端在线),均会实时监控异常登录行为。
主机安全控制台仅保留近6个月的异常登录事件,过期的事件数据将不再展示。
操作指南
1. 登录 主机安全控制台。
2. 单击左侧导航中的入侵检测 > 异常登录,各功能说明如下。
事件列表
在事件列表中,可查看并处理主机安全监测到的异常登录风险。

字段说明:
服务器IP/名称:被异常登录的服务器。
来源 IP:登录来源 IP,一般是公司网络出口 IP 或网络代理 IP。
来源地:登录来源 IP 所在的地域。
登录用户名:成功登录服务器时使用的登录用户名。
登录时间:成功登录服务器的时间(服务器上的时区时间)。
危险等级:可疑/高危。
状态
异常登录:本次登录存在异常地域、异常用户名、异常登录时间或异常IP登录。
已加入白名单:登录来源已被添加为白名单(登录源 IP、登录用户名、登录时间及常用登录地)。
已处理:用户已手动处理,并将该事件标记为已处理。
已忽略:用户已忽略本次告警事件。
操作
处理
标记已处理:若您已人工对该风险事件进行处理,可将事件标记为已处理。
加入白名单:加入白名单操作后,当再次发生相同事件时将不再进行告警,请谨慎操作。
忽略:仅将本次告警事件进行忽略,若再有相同事件发生依然会进行告警。
删除记录:删除该事件记录,控制台将不再显示,无法恢复记录,请慎重操作。
白名单管理
在白名单管理中,可增/删/改/查异常登录的白名单。
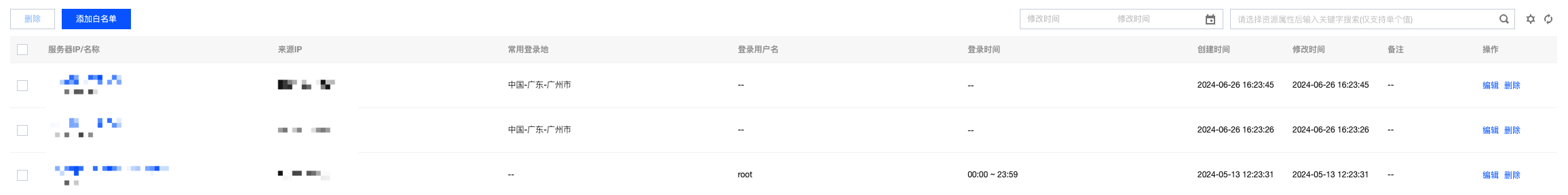
字段说明:
服务器IP/名称:该白名单生效的服务器。
来源IP:加白名单的来源IP。
常用登录地:加白名单的登录地。
登录用户名:加白名单的用户名。
登录时间:加白名单的时间。
创建时间:该白名单的创建时间。
修改时间:最近一次修改白名单的时间。
操作
编辑:可重新编辑登录源ip、登录用户名、登录时间、常用登录地、生效范围等。
删除:可对白名单进行删除操作。
热点问题
收到异常登录告警后该如何处理?
判断该登录行为是否自己操作。
若是自己的登录行为,且您不希望再看到告警,请单击处理选择加入白名单操作,对常见登录源 IP、登录用户名、登录地、登录时间、生效范围进行设置。

字段说明:
登录源 IP 为空:代表所有来源 IP 对服务器进行登录,均不产生告警。
登录用户名为空:代表对服务器的任何用户名进行登录,均不产生告警。
登录地为空:代表不论登录地域在哪,均不产生告警。
登录时间为空:代表不论何时登录,均不产生告警。
注意:
登录源 IP、登录用户名、登录地、登录时间不能同时为空。
若不是自己的登录行为,请立即修改服务器登录密码(建议修改为10位以上,包含大小写字母和特殊字符的强密码)。
服务器被异常登录,登录者很有可能已经入侵您的服务器并留下恶意文件。建议您立即进行 文件查杀、漏洞检测、基线检测 以加固您的服务器安全。
白名单怎么设置可以满足大部分用户需求?
场景1:固定 IP 网段登录源可以使用任一用户名对服务器进行登录,而不产生异常登录告警。
您可在登录源 IP 中输入 IP 段,选择生效服务器范围即可。


场景2:登录源 IP 是动态变化的,要支持登录地是中国香港地区的 IP 随时都可以使用任一用户名对服务器进行登录,而不产生异常登录告警。
您可在常用登录地中选择香港特别行政区,选择生效服务器范围即可。


说明:
登录条件支持组合。
如何关闭异常登录告警?


文档反馈