平台托管的速率限制规则(原 CC 攻击防护)
下载
聚焦模式
字号
概述
CC(Collapse Challenge)攻击,即 HTTP/HTTPS DDoS 攻击。攻击者通过占用 Web 服务的连接和会话资源,导致服务无法正常响应用户请求,拒绝服务。为避免 CC 攻击,EdgeOne 提供了预设的 CC 攻击防护策略,并默认开启,确保您的站点稳定在线。
EdgeOne 使用“干净流量”计费模式,即对于安全防护功能拦截的请求不进行计费,仅对通过安全防护功能处理后的流量和请求用量计费。对“干净流量”计费模式的定义请参见 关于“干净流量”计费说明。
使用平台托管的速率限制
平台托管的速率限制通过速率基线学习、头部特征统计分析和客户端IP情报等方式识别 CC 攻击,并进行处置。EdgeOne 提供了预设的三种 CC 攻击防护策略:
自适应频控:用于应对通过高频和大量并发的连接请求占用服务器资源的 CC 攻击行为,可基于单 IP 源限制访问频次。
慢速攻击防护:用于应对通过大量慢速连接请求占用服务器资源的 CC 攻击行为,可基于单会话限制访问连接最低速率,淘汰慢速连接客户端。
智能客户端过滤:融合了速率基线学习、头部特征统计分析和客户端 IP 情报,实时动态生成防护规则。针对来自高危客户端、或者携带高危头部特征的请求进行人机验证。智能客户端过滤默认开启且对符合规则的客户端执行 JavaScript 挑战。
自适应频控
自适应频控通过持续监控和分析您网站的流量模式来建立并更新速率基线。系统根据配置统计当前域名的请求速率,基于最近 7 天请求建立速率基线(每 24 小时更新),结合配置的限制等级,限制单个客户端访问该域名的请求速率。
注意:
操作步骤
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,进入服务总览,单击网站安全加速内需配置的站点。
2. 单击安全防护 > Web 防护。默认为站点级防护策略,若需为当前站点下特定域名配置差异化的防护策略,请进入域名级防护策略 Tab,单击相应域名进入域名级防护策略配置页,后续步骤一致。
3. 定位到速率限制卡片,单击自适应频控右侧的编辑。
4. 配置自适应频控的限制等级和处置方式,各限制等级及速率阈值说明如下:
限制类型 | 限制等级 | 适用场景 | 初始访问频次限制 |
自适应 | 宽松(默认配置,推荐) | 适用于大部分无需实时数据交互或查询的 Web 业务场景。 | 2000 次 / 5 秒 |
| 适中 | 适用于页面内容较为简单,动态数据或动态加载内容较少的业务场景。 | 200 次 / 10 秒 |
| 紧急 | 适用于仅提供静态内容为主的 Web 业务场景,当攻击发生时,或者其他限制等级防护有防护透传造成业务影响时,可选择该限制等级进行紧急防护。由于该等级的速率限制较为严格,可能存在误杀风险,不建议长期使用。 | 40 次 / 10 秒 |
说明:
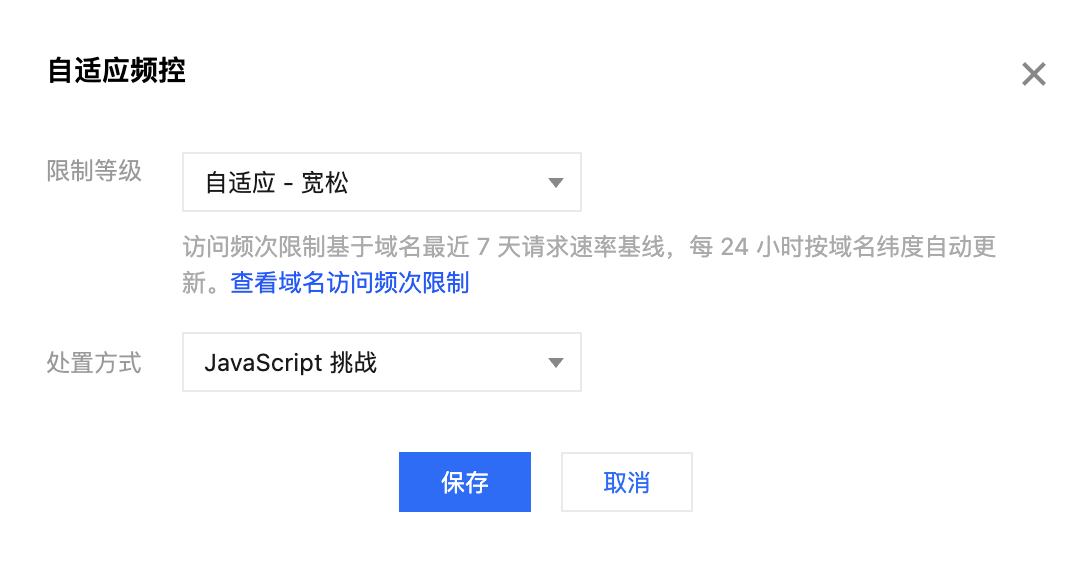
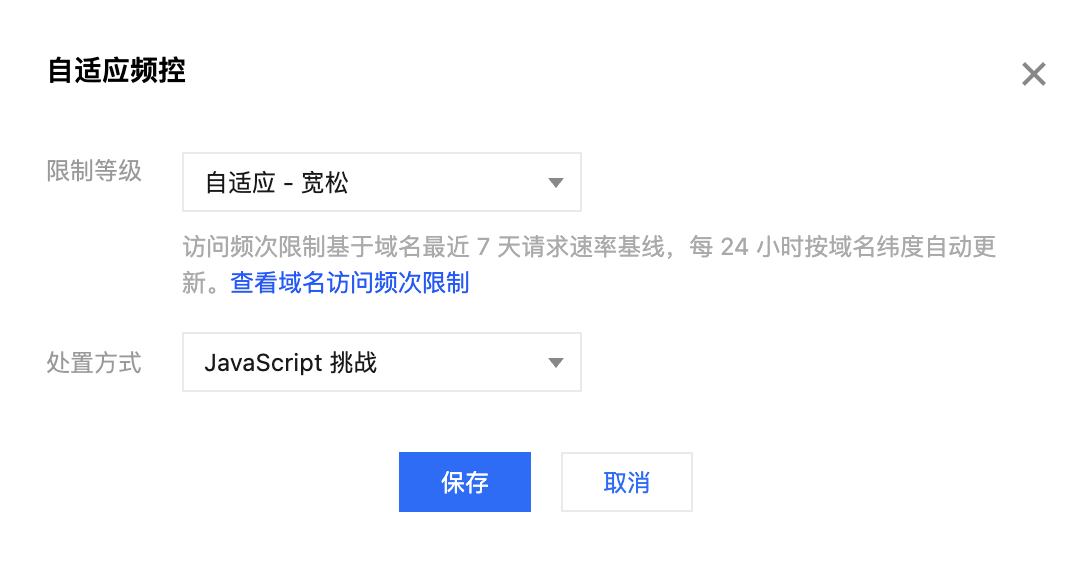
5. 单击保存,完成规则配置。
查看域名的访问频次限制
操作步骤
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,进入服务总览,单击网站安全加速内需配置的站点。
2. 单击安全防护 > Web 防护。默认为站点级防护策略,若需为当前站点下特定域名配置差异化的防护策略,请进入域名级防护策略 Tab,单击相应域名进入域名级防护策略配置页,后续步骤一致。
3. 定位到速率限制卡片,单击自适应频控左侧的查看。
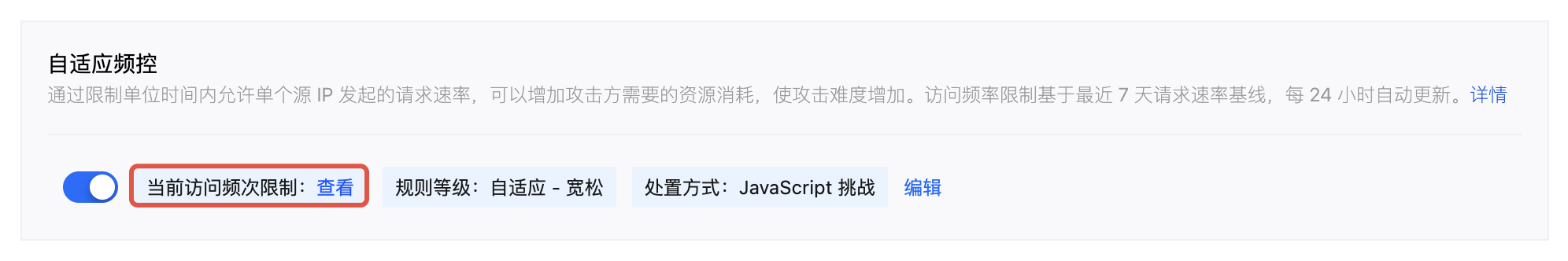
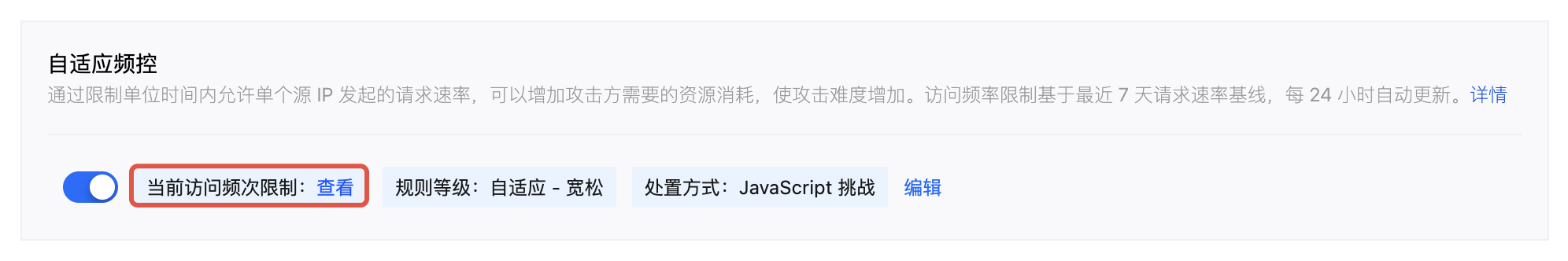
4. 在弹窗中查看当前防护策略所关联域名的对应访问频次限制。


说明:
基线计算和更新方式
自适应频控根据配置的限制等级,统计当前域名的请求速率,以近 7 天的每日峰值流量动态生成速率基线。基线每 24 小时更新一次,始终基于最近 7 天的流量数据进行计算。
自适应频控采用分布式统计方法,每个 EdgeOne 节点基于客户端 IP 统计访问请求速率,并依据当前限制等级对应的阈值范围执行限速。由于分布式统计特性,汇聚至源站的实际请求速率可能超过上限。
开启建议
为充分发挥自适应频控的优势,我们推荐您遵循以下渐进式启用方式:
1. 初始配置:启用自适应频控并选择“自适应 - 宽松”等级,处置方式为观察。宽松等级适用于大部分 Web 业务场景,其较高的初始访问频次限制值可以有效降低误拦截的风险,同时为系统学习您的流量模式提供足够的空间。
2. 学习期(建议 7 天):在这个阶段,系统将深入分析您的流量模式,以 24 小时的更新周期,基于历史访问流量统计源 IP 访问速率,逐步建立准确的速率基线。
3. 策略优化:经过学习,系统已经建立了相对准确的流量基线。您可以在 Web 安全分析 查看命中自适应频控的流量,根据防护效果和业务需求,决定是否需要调整收紧策略。
查看命中自适应频控的流量
要查看命中自适应频控规则的流量:
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,单击Web 安全分析。
2. 选择时间段为初始接入自适应频控后截止到当前时间的学习期。
3. 单击添加筛选,选择 Web 防护 - CC 攻击防护规则等于自适应频控。
4. 单击确定,应用筛选条件,在统计趋势和统计详情处观察防护效果。
功能限制及处理方案
自适应频控在某些特殊情况下可能需要额外调整:
1. 低频攻击:当攻击频率低于设定的限制等级对应的频次下限时,自适应频控可能无法有效拦截。此时,建议使用 Web 安全分析 对低频攻击行为进行特征识别和定位,如连续多次访问特定敏感页面/接口等,结合 自定义规则 或 自定义速率限制规则,对满足特征的访问请求进行拦截。
2. 合法高频访问:合法的高频访问(如 API 调用)可能超过自适应频控的频次上限而被误拦截。如零售、电商、游戏平台等需要客户端实时查询数据的业务类型,旅行、票务等开放第三方 API 服务等场景,建议关闭自适应频控功能,避免误拦截。
3. 特殊业务场景:游戏更新、活动促销、票务开售等重大事件时,自适应频控可能影响到短时间内业务的正常访问高峰。在短时间访问行为与常态有较大区别的情况下,建议关闭自适应频控功能,避免误拦截。可结合多维度特征,使用 自定义规则 和 自定义速率限制规则 进行精细化防护。
配置慢速攻击防护
通过限制最小请求速率和设置超时,缓解慢速传输等攻击场景对站点资源的消耗,避免服务可用性下降。EdgeOne 慢速攻击防护支持正文传输超时和正文传输最小速率选项,当正文传输速率缓慢,或长时间无数据传输时,对客户端进行处置。
操作步骤
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,进入服务总览,单击网站安全加速内需配置的站点。
2. 单击安全防护 > Web 防护。默认为站点级防护策略,若需为当前站点下特定域名配置差异化的防护策略,请进入域名级防护策略 Tab,单击相应域名进入域名级防护策略配置页,后续步骤一致。
3. 定位到速率限制卡片,单击慢速攻击防护右侧的编辑。
4. 配置慢速攻击防护规则的匹配方式,可选以下限制:
正文传输时长:缓解通过占用连接但不传输正文数据的慢速攻击方式。指定正文传输超时时长,超过配置时间未完成前 8KB 正文数据传输的客户端,将按指定方式处置;支持配置 5-120 秒。
正文传输最小速率:缓解通过极慢速传输正文占用连接和会话资源的攻击。可指定最低传输速率,在统计时间窗口内传输的请求正文小于配置速率时,按指定方式处置,传输速率配置最小支持 1 bps,最大 100 Kbps。


说明:
5. 单击保存,完成规则配置。
智能客户端过滤
智能客户端过滤融合了速率基线学习、请求头部特征统计分析和客户端 IP 情报,实时动态生成防护规则。针对来自高风险客户端或携带高风险请求头特征的流量执行实时人机识别。智能客户端过滤默认开启且对符合规则的客户端执行 JavaScript 挑战。
智能客户端过滤是一种高级防护机制,融合了速率基线学习、请求头特征分析和客户端 IP 信誉评估技术。该功能能够实时动态生成防护规则,并针对来自高风险客户端或携带高风险请求头特征的流量执行实时人机识别。智能客户端过滤默认开启,对符合规则的可疑客户端自动实施 JavaScript 挑战。
注意:
智能客户端过滤使用业务速率基线作为参考之一,在业务发生重大变更(新业务接入、流量切换、新功能上线或营销活动上线)时,基线变化可能导致误拦截,建议在此类情况下,暂时将处置方式调整为"观察",待业务流量恢复稳定后开启。
智能客户端过滤仅标准版及企业版套餐支持。
策略机制
智能客户端过滤采用实时学习算法,持续分析过去 1 - 12 小时的请求流量,建立并存储用户正常流量基线模型。当检测到流量异常时,系统会分析当前请求特征的聚集情况,并与历史流量进行对比,从而识别出潜在的异常流量并执行相应处置。
修改智能客户端过滤处置方式
如果您需要修改触发智能客户端过滤后的处置方式,您可以参照以下操作步骤:
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,进入服务总览,单击网站安全加速内需配置的站点。
2. 单击安全防护 > Web 防护。默认为站点级防护策略,若需为当前站点下特定域名配置差异化的防护策略,请进入域名级防护策略 Tab,单击相应域名进入域名级防护策略配置页,后续步骤一致。
3. 定位到速率限制卡片,单击智能客户端过滤右侧的编辑。
4. 配置处置方式。
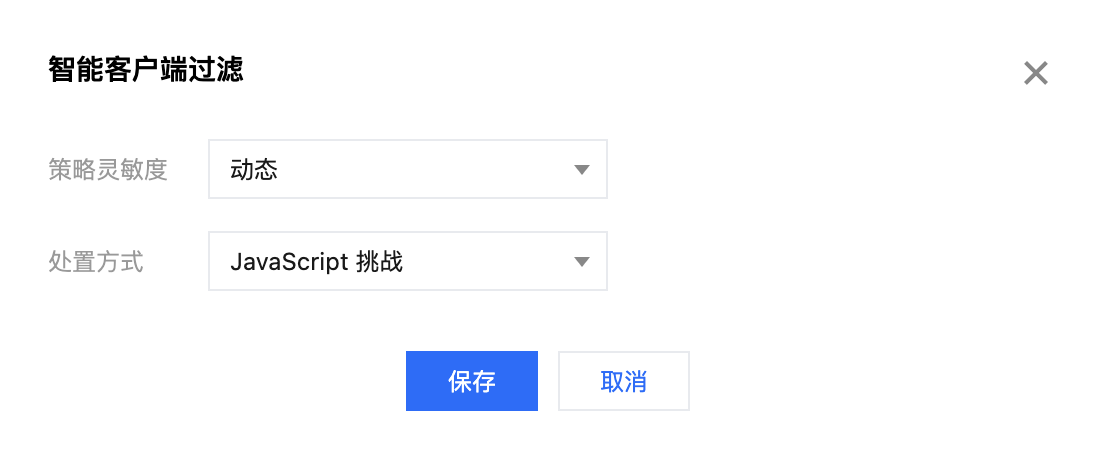
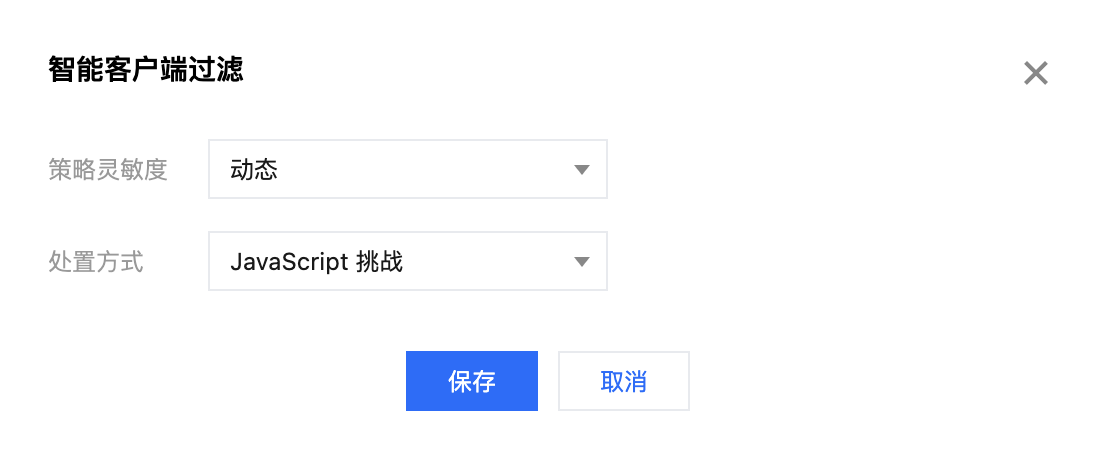
说明:
5. 单击保存,完成规则配置。
说明:
查看命中智能客户端过滤的流量
要查看命中智能客户端过滤规则的流量:
1. 登录 边缘安全加速平台 EO 控制台,在左侧菜单栏中,单击Web 安全分析。
2. 单击添加筛选,选择 Web 防护 - CC 攻击防护规则等于智能客户端过滤。
3. 单击确定,应用筛选条件,在统计趋势和统计详情处观察防护效果。
功能限制及处理方案
智能客户端过滤在某些特殊情况下可能需要额外调整:
文档反馈