SSL 单向认证和双向认证说明
下载
聚焦模式
字号
SSL(Secure Sockets Layer,安全套接字协议)是为网络通信提供安全及数据完整性的一种安全协议。本文主要介绍 SSL 单向认证和双向认证。
说明:
SSL 单向认证和双向认证的区别
SSL 单向认证相对于 SSL 双向认证的认证过程,无需在服务端验证客户端证书、以及协商加密方案,服务端发送给客户端也是未加密的密码方案(并不影响 SSL 认证过程的安全性)。
一般 Web 应用的用户数量众多,无需在通讯层做用户身份验证,因此配置 SSL 单向认证即可。但部分金融行业用户的应用对接,可能会要求对客户端做身份验证,此时就需要做 SSL 双向认证。
SSL 单向认证
SSL 单向认证只需要验证服务端的身份,无需验证客户端的身份。SSL 单向认证的流程如下图所示。
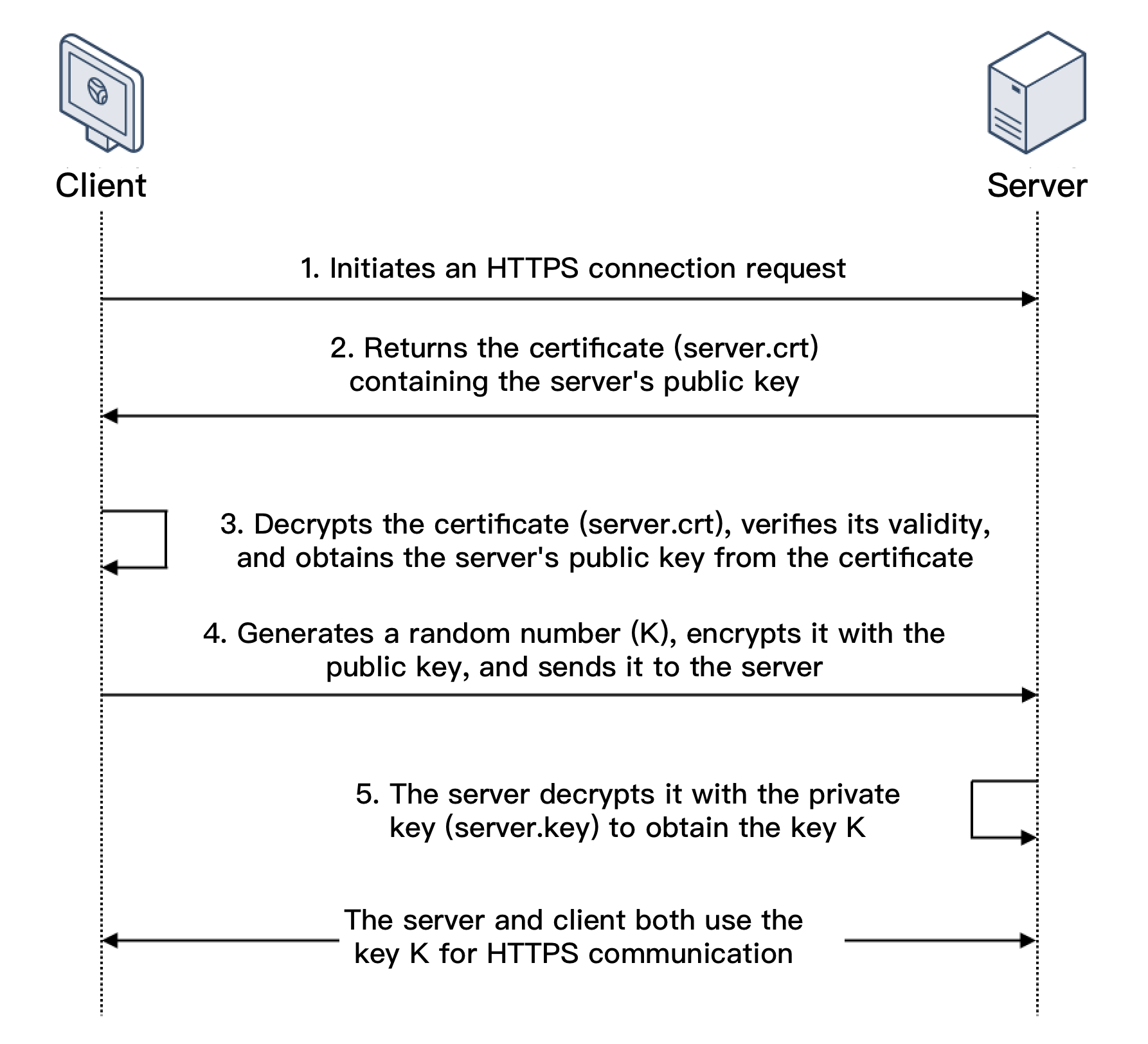
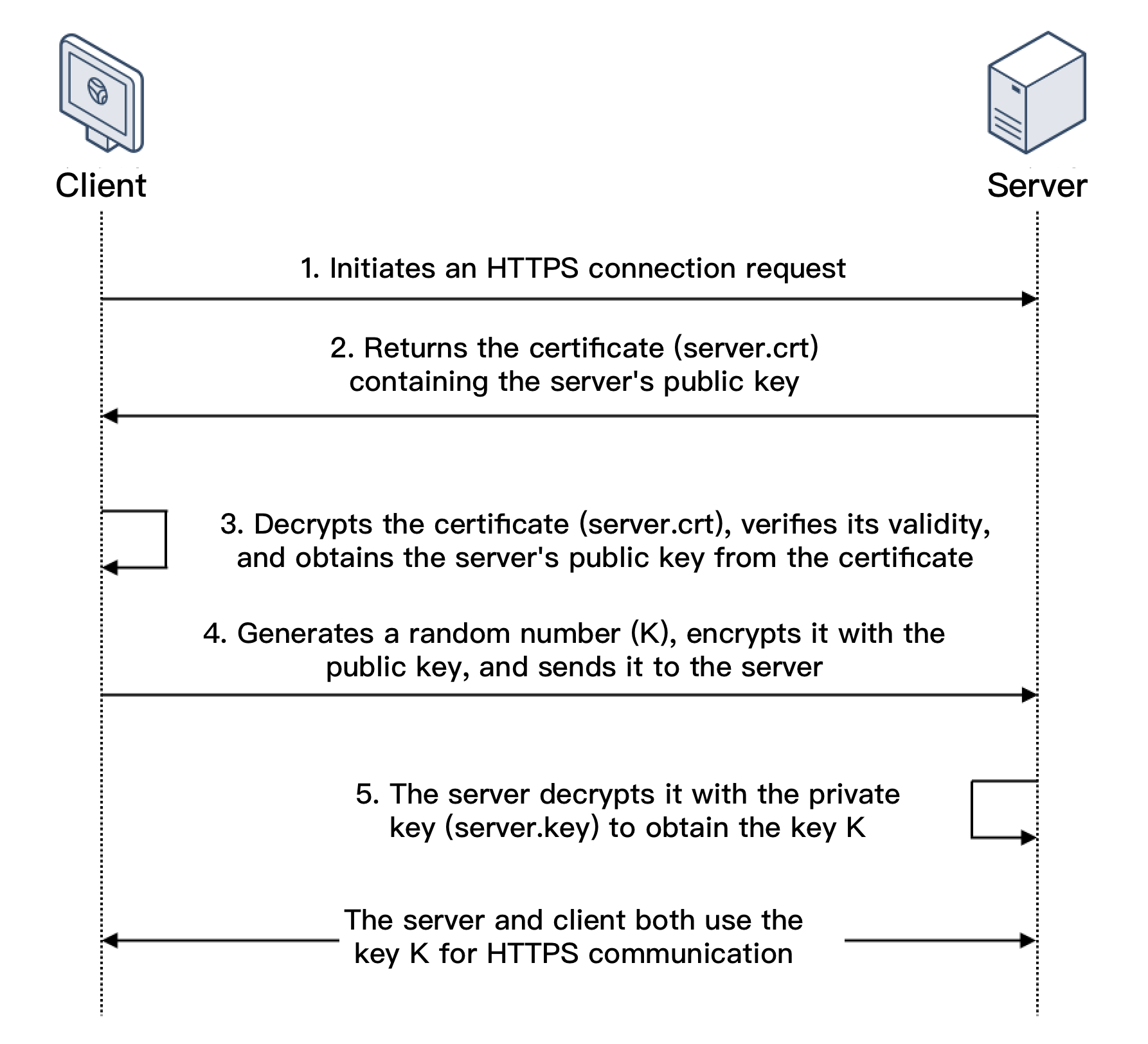
1. 客户端发起 HTTPS 建立连接请求,将客户端支持的 SSL 协议版本号、加密算法种类、生成的随机数等信息发送给服务端。
2. 服务端向客户端返回 SSL 协议版本号、加密算法种类、生成的随机数等信息,以及服务端的证书(server.crt)。
3. 客户端验证证书(server.crt)是否合法,并从此证书中获取服务端的公钥:
检查证书是否过期。
检查证书是否已经被吊销。
检查证书是否可信。
检查收到的证书中的域名与请求的域名是否一致。
4. 证书验证通过后,客户端生成一个随机数(密钥 K),作为通信过程中对称加密的密钥,并用服务端证书的公钥进行加密,然后发送给服务端。
5. 服务端收到客户端发送的加密信息后,使用私钥(server.key)进行解密,获取对称加密密钥(密钥 K)。
在接下来的会话中,客户端和服务端将会使用该对称加密密钥(密钥 K)进行通信,保证通信过程中信息的安全。
SSL 双向认证
SSL 双向认证需要验证客户端和服务端的身份。SSL 双向认证的流程如下图所示。
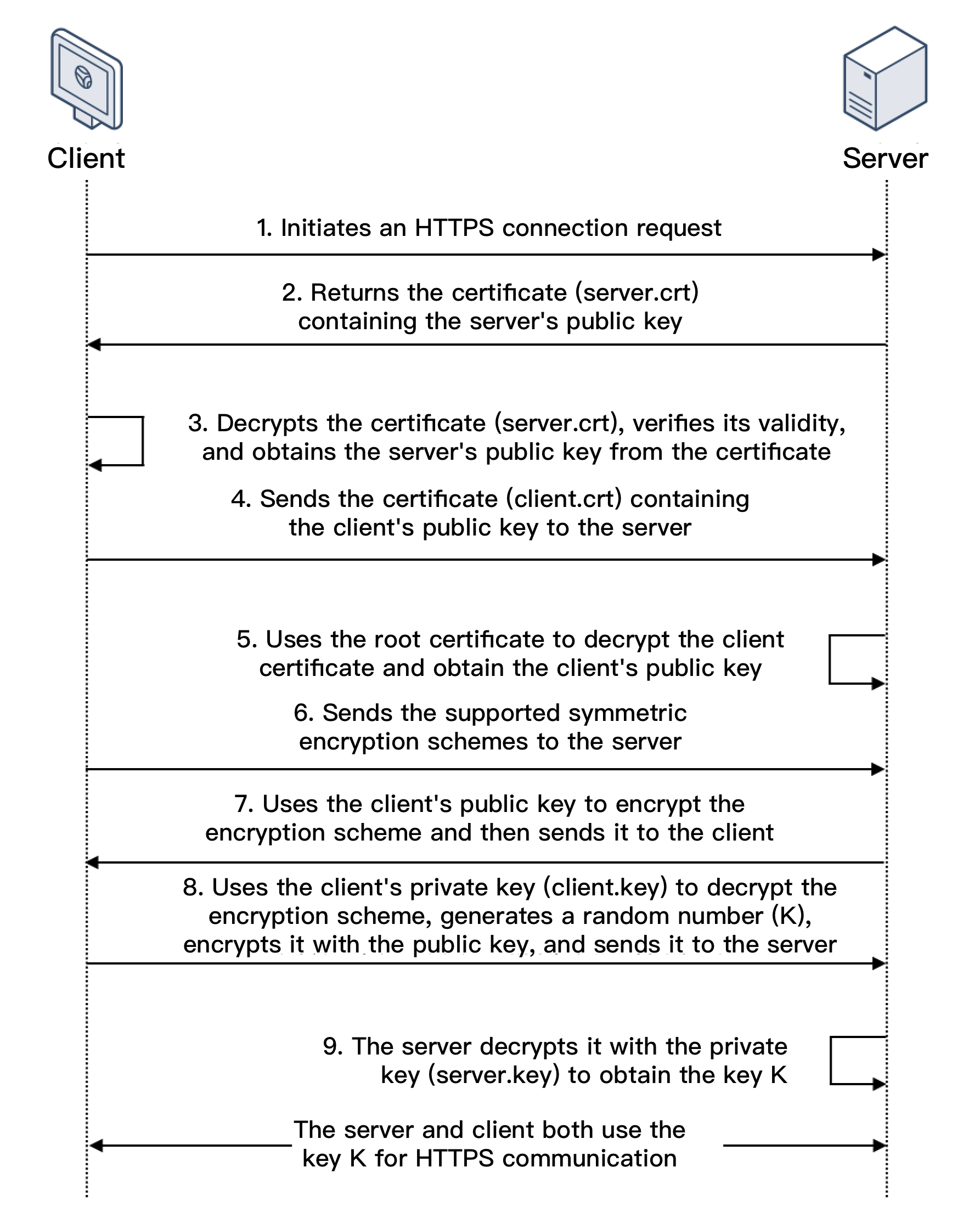
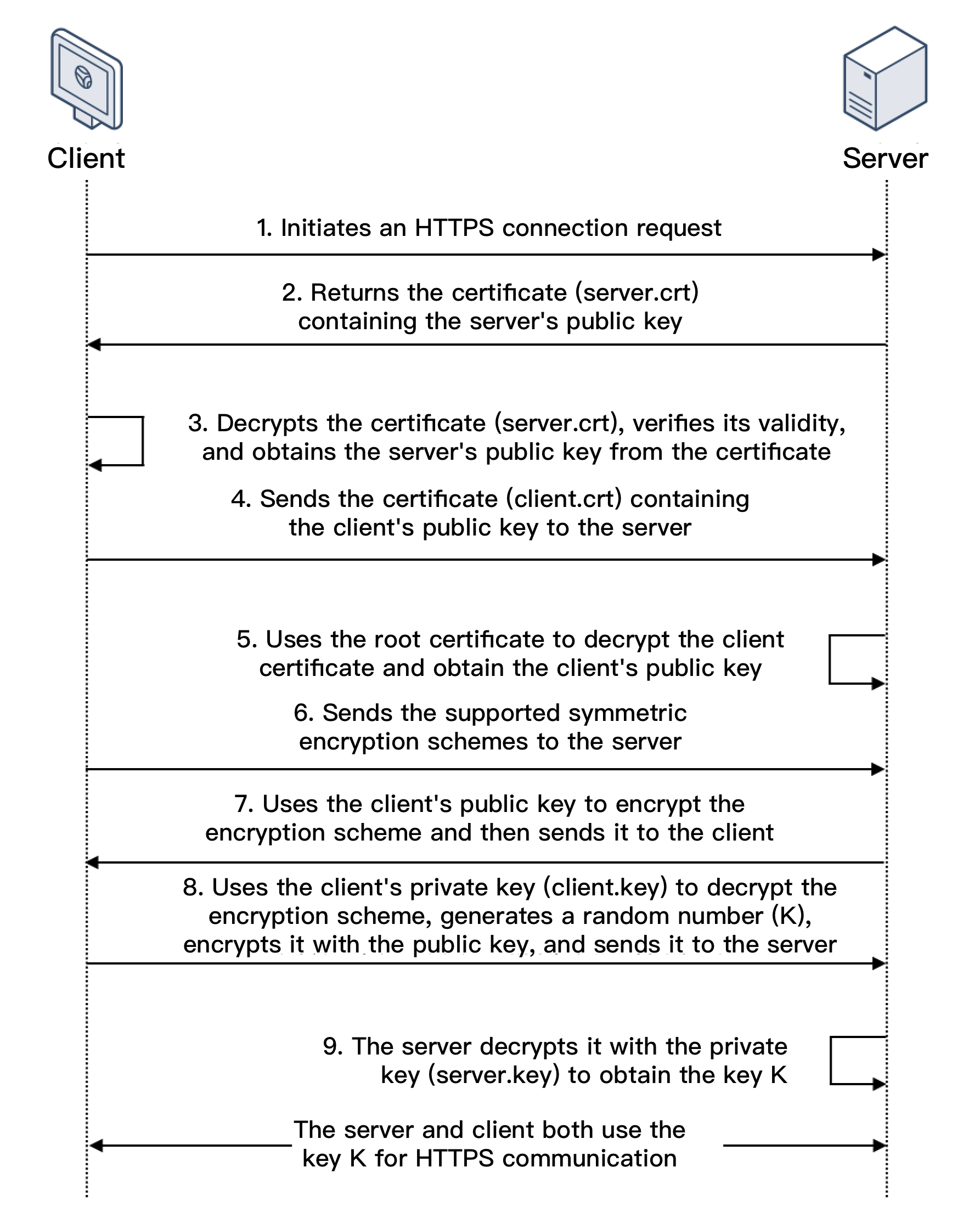
1. 客户端发起 HTTPS 建立连接请求,将客户端支持的 SSL 协议版本号、加密算法种类、生成的随机数等信息发送给服务端。
2. 服务端向客户端返回 SSL 协议版本号、加密算法种类、生成的随机数等信息,以及服务端的证书(server.crt)。
3. 客户端验证证书(server.crt)是否合法,并从此证书中获取服务端的公钥:
检查证书是否过期。
检查证书是否已经被吊销。
检查证书是否可信。
检查收到的证书中的域名与请求的域名是否一致。
4. 服务端要求客户端发送客户端的证书(client.crt),客户端将自己的证书发送至服务端。
5. 服务端验证客户端的证书(client.crt),验证通过后,服务端使用根证书(root.crt)解密客户端证书,然后获取客户端的公钥。
6. 客户端向服务端发送自己所支持的对称加密方案。
7. 服务端从客户端发送过来的对称加密方案中,选择加密程度最高的加密方式,并使用客户端公钥加密后,返回给客户端。
8. 客户端使用客户端的私钥(client.key)解密加密方案,并生成一个随机数(密钥 K),作为通信过程中对称加密的密钥,然后使用服务端证书的公钥进行加密后再发送给服务端。
9. 服务端收到客户端发送的加密信息后,使用服务端的私钥(server.key)进行解密,获取对称加密密钥(密钥 K)。
在接下来的会话中,客户端和服务端将会使用该对称加密密钥(密钥 K)进行通信,保证通信过程中信息的安全。
相关文档
文档反馈