产品动态
公告
监控指标名称 | 单位 | 指标说明 | 告警设置建议 |
写入请求次数 | 次 | 实例接收到写入请求的次数。 | - |
读取请求次数 | 次 | 实例接收到读请求的次数。 | - |
更新请求次数 | 次 | 实例接收到更新请求的次数。 | - |
删除请求次数 | 次 | 实例接收到删除请求的次数。 | - |
count 请求次数 | 次 | 实例接收到总请求的次数。 | - |
聚合请求次数 | 次 | 实例接收到聚合请求的次数。 | - |
成功请求次数 | 次 | 实例接收的请求执行成功的次数。 | - |
磁盘使用率 | % | 指当前磁盘已被使用的空间占总空间的百分比。 | 统计周期1分钟,>=90%,指标异常持续3个数据点,每30分钟告警异常 |
单位时间延迟次数(在10ms - 50ms) | 次 | 执行时间在10毫秒和50毫秒之间的请求次数。 | - |
单位时间延迟次数(在50ms - 100ms) | 次 | 执行时间在50毫秒和100毫秒之间的请求次数。 | - |
单位时间延迟次数(100ms以上) | 次 | 执行时间在100毫秒以上的请求次数。 | 统计周期1分钟,>=100,指标异常持续3个数据点,每30分钟告警异常 |
连接使用率 | % | 当前集群的连接数量占最大连接数的百分比。 | 统计周期1分钟,>=90%,指标异常持续3个数据点,每30分钟告警异常 |
每秒钟请求次数 | 次 | 实例每秒收到的请求次数。 | - |
command 请求次数 | 次 | 集群收到的 Command 请求的次数。Command 为除 insert、update、delete、query 以外命令的总称。 | - |
连接数 | 次 | 集群客户端的 TCP 的连接数量。 | - |
监控指标中文名称 | 单位 | 指标说明 | 告警设置建议 |
Cache 脏数据百分比 | % | 缓存中脏数据的大小(字节)与最大缓存的百分比。 | 统计周期1分钟,>=20%,指标异常持续3个数据点,每30分钟告警异常 |
Cache 使用百分比 | % | 缓存中实际占用的容量与配置的最大缓存之间的比例。 | - |
磁盘使用率 | % | 指当前磁盘已被使用的空间占总空间的百分比。 | 统计周期1分钟,>=90%,指标异常持续3个数据点,每30分钟告警异常 |
cache 命中率 | % | 指从缓存中获取数据的请求数与总请求数之间的比例 | - |
oplog 保存时间 | 小时 | Oplog 用于记录数据库的操作日志,该指标统计其保存时长。 | - |
主从单位时间内平均延迟 | s | 副本集架构中,从节点定期轮询主节点的 oplog(操作日志)来复制 Primary 节点的数据,该指标统计主从同步数据的时延。 | 统计周期1分钟,>=1800,指标异常持续3个数据点,每30分钟告警异常 |
监控指标中文名称 | 单位 | 指标说明 | 告警设置建议 |
CPU 使用率 | % | 指 CPU 正在执行进程所占用的时间占 CPU 总时间的百分比。 | 统计周期1分钟,>=80%,指标异常持续3个数据点,每30分钟告警异常 |
内存使用率 | % | 指当前内存中已被使用的空间占内存总容量的百分比。 | - |
网络入流量 | MB/s | 每秒节点入流量统计。 | - |
网络出流量 | MB/s | 每秒节点出流量统计。 | - |
Read 请求等待队列中的个数 | 个 | 队列中 Read 请求的等待个数。 | 统计周期1分钟,>=40,指标异常持续3个数据点,每30分钟告警异常 |
Write 请求等待队列中的个数 | 个 | 队列中 Write 请求的等待个数。 | 统计周期1分钟,>=40,指标异常持续3个数据点,每30分钟告警异常 |
连接数 | 个 | 连接客户端的数量。 | - |
节点磁盘用量 | MB | 节点磁盘已使用量。 | - |
WT 引擎的 ActiveRead | 个 | 数据在内存中被读请求的个数。 | 统计周期1分钟,>=40,指标异常持续3个数据点,每30分钟告警异常 |
WT 引擎的 ActiveWrite | 个 | 数据在内存中被写请求的个数。 | 统计周期1分钟,>=40,指标异常持续3个数据点,每30分钟告警异常 |
TTL 删除的数据条数 | 个 | 在 TTL 过期后,数据库自动删除的数据条数。 | - |
TTL 运转轮数 | 次 | 指在数据库中设置的 TTL 时间内,数据被检查的次数。 | - |
监控指标中文名称 | 单位 | 指标说明 | 告警设置建议 |
CPU 使用率 | % | 指 CPU 正在执行进程所占用的时间占 CPU 总时间的百分比。 | 统计周期1分钟,>=80%,指标异常持续3个数据点,每30分钟告警异常 |
内存使用率 | % | 指当前 Mongos 节点的内存已被使用的空间占内存总容量的百分比。 | - |
网络入流量 | MB/s | 每秒节点入流量统计。 | - |
网络出流量 | MB/s | 每秒节点出流量统计。 | - |



参数名称 | 参数解释 |
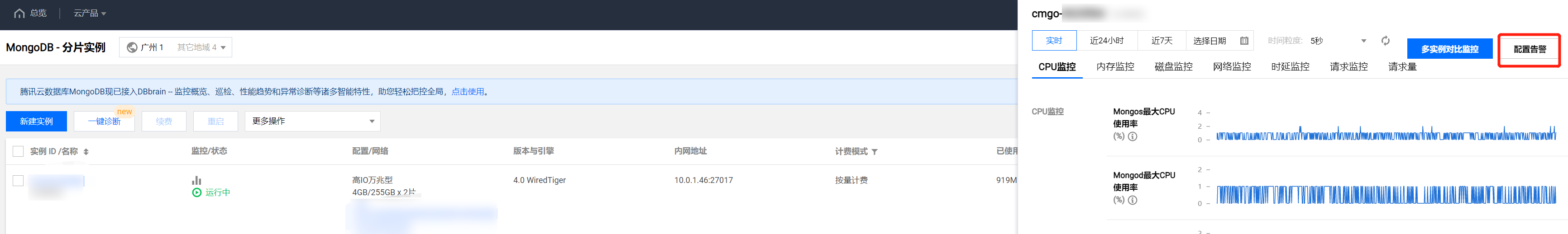
策略名称 | 给告警策略自定义名称,便于识别即可。 |
备注 | 简要描述告警策略,便于识别。 |
监控类型 | 请选择云产品监控。 |
策略类型 | 设置策略类型为云数据库 / MongoDB / 实例、云数据库 / MongoDB / Mongod节点、云数据库 / MongoDB / Mongos节点或云数据库 / MongoDB / 副本集。 |
策略所属项目 | 给告警策略指定项目,您可以在告警策略列表快速筛选该项目下的所有告警策略。 |
告警对象 | 选择实例 ID:则该告警策略绑定指定的数据库实例。 选择实例分组:则该告警策略绑定指定的数据库实例组。如何创建实例组,请参见 实例分组。 选择全部对象:则该告警策略绑定当前账号拥有权限的全部实例。 选择标签:则该告警策略绑定当前标签键与标签值所关联的全部实例。 |
触发条件 | 选择模板:在下拉列表选择模板文件,将根据模板文件预置的触发条件上报告警,具体配置,请参阅 配置触发条件模板 。 手动配置:需在下方指标告警区域,逐一配置每一条指标触发告警的阈值条件。指标告警区域的阈值类型: 选择静态:人为设定恒定阈值,在达到触发条件后发送告警。 选择动态:动态阈值基于机器学习算法算出的阈值边界来判断异常。 |
告警通知 |
API 接口名称 | API 接口功能描述 |
创建腾讯云可观测平台告警策略 |
文档反馈