ビデオ暗号化の概要
ダウンロード
フォーカスモード
フォントサイズ
eラーニングプラットフォームやOTTビデオポータルには、大量の良質なコンテンツが存在します。ユーザーは動画やカリキュラムを購入したり、会員パッケージを購入したりすることで、完全なコンテンツを視聴できる権利を獲得します。
しかしながら、著作権侵害行為が後を絶たない中で、著作権のセキュリティはオーディオビデオ業界のVOD分野における最大の課題となっています。


著作権侵害の主な形式
著作権侵害の形式には、主にリンク不正アクセス、クラッキング、不正録画・録音の3つがあります。
著作権侵害の形式 | リンク不正アクセス | クラッキング | 不正録画・録音 |
説明 | 再生URLが他のサイトにマウントされます。 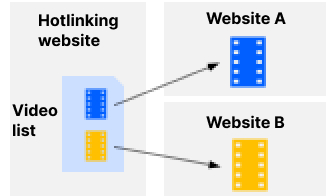 | 暗号化したビデオがクラックされて拡散されます。  | スクリーンキャプチャソフトで録画またはカメラで撮影されます。  |
著作権保護機能
Tencent Cloud VODは著作権保護の分野で長年にわたり豊富な経験を積み重ね、一連の完全な著作権保護機能をご提供しています。
カテゴリー | 機能項目 | VOD対応機能 |
コンテンツ保護 | メディアコンテンツ暗号化保護 | HLSプライベート暗号化、商用DRM |
| パケットキャプチャおよびクラッキングツールによるクラッキングの防止 | HLSプライベート暗号化、商用DRM |
| ブラウザプラグインによるクラッキングの防止 | HLSプライベート暗号化、商用DRM |
| ブラウザプラグインによるスクリーンキャプチャの防止 | HLSプライベート暗号化、商用DRM |
| システムソフトウェアおよびサードパーティソフトウェアによるスクリーンキャプチャの防止 | 商用DRM |
再生保護 | 再生可能な国および地域を制限 | Keyホットリンク防止 |
| 再生可能なサイトを制限 | Refererホットリンク防止 |
| 再生リンクの有効時間を制限 | Keyホットリンク防止 |
| 再生リンクの最大再生IP数を制限 | Keyホットリンク防止 |
| コンテンツのコンテンツプレビュー時間を制限 | Keyホットリンク防止 |
不正録画・録音の追跡 | 不正録画・録音者のIDを追跡 | フローティングウォーターマーク、トレーサビリティウォーターマーク |
メディア暗号化セキュリティレベルと互換度
VODのメディア暗号化には、HLSプライベート暗号化と商用DRMという2つの方式があります。
HLSプライベート暗号化
Tencent Cloud VODが自社開発したメディア暗号化です。デフォルトでは「標準」モードで動作し、標準モードをサポートしていない一部の再生端末では、プレーヤーが自動的に「ベーシック」モードでの再生を試行します。
商用DRM
VODは現在、FairPlay(Apple系プラットフォーム)とWidevine(Google系プラットフォーム)をサポートしています。このうち、WidevineはL1とL3という2つのレベルをサポートしており、L1の復号には専用のハードウェアTEE環境が必要で、再生端末に対する要件がより高いです。デバイス自体がL1をサポートしていない場合は、自動的にL3での再生を試行します。
コンテンツ保護方式 | セキュリティレベル | 互換度 |
HLSプライベート暗号化(標準) | 高い コンテンツの暗号化保護を行います。 パケットキャプチャ防止およびクラッキングツール対策機能が強力です。 ブラウザプラグインによるクラッキング、スクリーンキャプチャの防止機能が強力です。 システムおよびソフトウェアによるスクリーンキャプチャの防止機能は比較的弱いです。 | 高い モバイル端末Appによる再生をサポートしています。 PC端末は大部分のブラウザをサポートしています。 Android端末は大部分のブラウザをサポートしています。iOSブラウザは現時点ではサポートしていません。 |
HLSプライベート暗号化(ベーシック) | 中程度 コンテンツを暗号化して保護します。 クラッキングおよびスクリーンキャプチャツール対策機能は比較的弱いです。 | 非常に高い 既知の各端末での再生に基本的に対応しています。 |
FairPlay | 非常に高い 復号はハードウェアレベルです。 各種ツールおよびプラグインによるクラッキングの防止機能は非常に強力です。 システム、ソフトウェア、プラグインによるスクリーンキャプチャの防止機能は非常に強力です。 | 比較的高い iOS端末Appでの再生をサポートしています。 iOS端末およびPC端末で、Safariブラウザでの再生をサポートしています。 |
Widevine(L1) | 非常に高い 復号はハードウェアレベルです。 各種ツールおよびプラグインによるクラッキングの防止機能は非常に強力です。 システム、ソフトウェア、プラグインによるスクリーンキャプチャの防止機能は非常に強力です。 | 比較的低い ブラウザ再生をサポートしていません。 一部のAndroid端末Appでの再生をサポートしています。 |
Wiedvine(L3) | 高い 復号はソフトウェアレベルです。 各種ツールおよびプラグインによるクラッキングへの対策は強力です。 スクリーンキャプチャツール対策機能は比較的強いです。 | 中程度 Chromeブラウザおよび一部のChromiumカーネルブラウザでの再生をサポートしています。 一部のAndroid端末のApp。 |
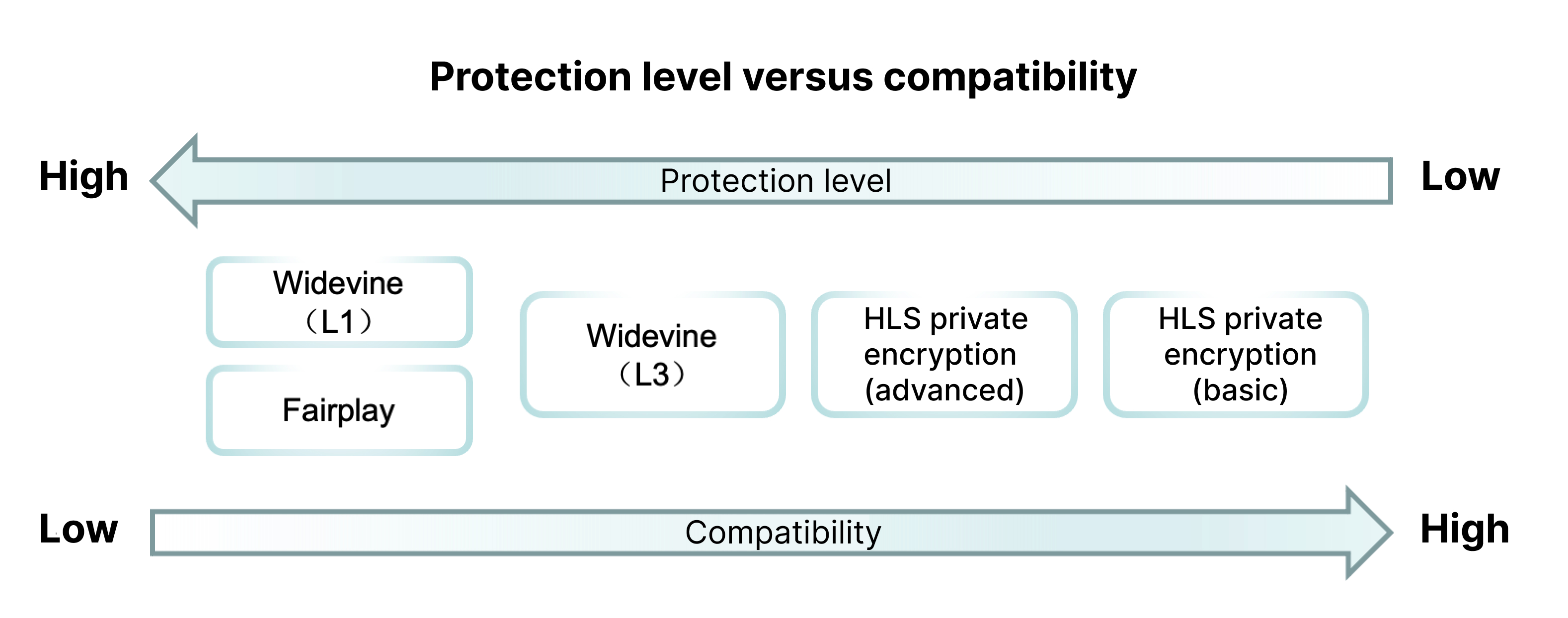
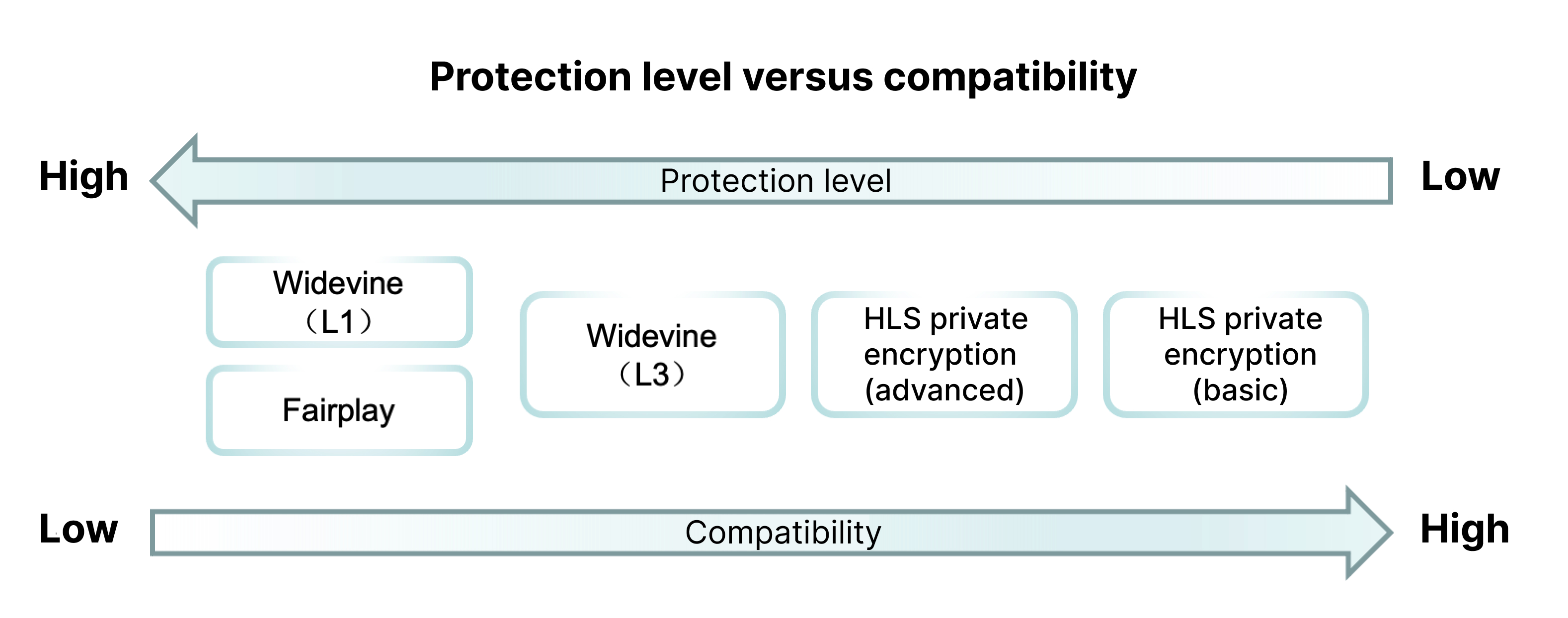
上の図からわかるように、コンテンツ保護方式(HLSプライベート暗号化、商用DRM)のセキュリティレベルと互換度は逆相関の関係にあります。つまり、通常セキュリティレベルが高いほど、再生端末に対する互換度は低くなります。このため、高いセキュリティレベルと高い互換度のバランスをどのようにとるかが、著作権保護において必ず考慮すべき問題となっています。
著作権保護の実施にあたっては、下記のベストプラクティスのパートをご参照ください。
ベストプラクティス
ベストプラクティスのパートでは、コンテンツ保護、不正録画・録音追跡、再生保護の3つの点から、最適な著作権保護ソリューションの構築方法についてご紹介します。
コンテンツ保護
コンテンツ保護のセキュリティレベルと再生端末の互換度が逆相関の関係にあることは上記の説明のとおりです。高いセキュリティレベルと互換度の両方を同時に実現するために、解像度のランクによって異なるコンテンツ保護方式を用いることをお勧めします。
HLSプライベート暗号化では、720P以下の仕様の再生のみ可能です。
WidevineとFairPlayで保護されたコンテンツは、すべての解像度仕様での再生が可能です。
VODのPlayer SDKは暗号化されたメディアコンテンツを再生する際、まずWidevineおよびFairPlayで保護された出力の再生を試みます。端末が商用DRMをサポートしていない場合は自動的にレベルを下げ、HLSプライベート暗号化で保護された出力を再生します。
上記の方式を用いることで、高価値のコンテンツ(解像度720P以上)を商用DRMのハードウェアレベルの暗号化・復号で保護することが可能になり、非常に強力なクラッキング防止、スクリーンキャプチャ防止機能を実現できます。一方、HLSプライベート暗号化は互換度がより高く、コンテンツがクラッキングや不正録画・録音の被害に遭った場合でも、漏洩するのは比較的低価値のコンテンツ(720P以下)というメリットがあります。
不正録画・録音の追跡
商用DRMは互換度の問題により、通常はHLSプライベート暗号化を併用する必要がありますが、プライベート暗号化での再生には不正録画・録音のリスクが存在します。このため、フローティングウォーターマークとトレーサビリティウォーターマークを有効化することが、不正録画・録音者のIDを追跡できる重要な手段となります。
フローティングウォーターマークは、クライアントでの再生の際に、ビデオ画面上にオーバーレイされるウォーターマークです。ウォーターマークの内容は、通常は視聴者のIDです。フローティングウォーターマークは使用コストが極めて低いですが、一定程度は不正録画の抑止効果があります。
トレーサビリティウォーターマークはデジタルウォーターマークの一種であり、画面または音声内にエンコードされます。オーディオビデオが不正録画・録音された場合、クラウド側で不正録画・録音者のIDを抽出することができます。トレーサビリティウォーターマークはフローティングウォーターマークに比べて見た目が美しく(肉眼で見えない)、より安全(ウォーターマークがエンコードされているため、削除やブロックができない)です。
このため、不正録画・録音行為を効果的に追跡できるように、フローティングウォーターマークおよびトレーサビリティウォーターマークを併用することをお勧めします。
再生保護
リンク不正アクセス防止によって、メディアリンクの再生保護を実現できます。次のことをお勧めします。
Refererホワイトリストを有効化し、サイトのドメイン名をホワイトリストに追加して、ホワイトリスト以外のサイトからのビデオへのアクセスを防止します。
KEYリンク不正アクセス防止で、再生リンクの有効時間をビデオの時間プラス30分に指定します。
KEYリンク不正アクセス防止で、再生リンクの再生を許可するIPの最大数を3に指定します。
KEYリンク不正アクセス防止で、再生リンクを、サイトの存在する国または地域での再生のみ許可するように設定します。
ベストプラクティスの操作例
上記のベストプラクティスについて、操作と体験の方法を以下の例で説明します。
FairPlay証明書の申請方法
ビデオの暗号化とトレーサビリティウォーターマーク付与の方法
ビデオをVODにアップロードし、HLSプライベート暗号化、FairPlayおよびWidevineで暗号化されたアダプティブビットレートストリーミングに出力します。
1. VODコンソールにログインし、アプリケーションからナビゲーションバーのメディア資産管理>オーディオビデオ管理に進み、オーディオビデオのアップロードをクリックしてビデオをアップロードします。
2. アップロード完了後、ご自身のビデオを選択し、タスクフローボタンをクリックし、「タスクフローテンプレート」でMultiDRMPresetタスクフローを選択し、OKをクリックして暗号化を開始します。
タスク実行が完了すると、HLSプライベート暗号化出力(480P以下の解像度のみ)、FairPlay暗号化出力およびWidevine暗号化出力が得られます。また、すべての暗号化出力にトレーサビリティウォーターマークが付与されています。
注意:
MultiDRMPresetタスクフローではHLSプライベート暗号化の出力にトレーサビリティウォーターマークを付与できますが、トレーサビリティウォーターマークを付与するには、ビデオの長さが6分以上必要です。ビデオが6分に満たない場合はタスクが失敗します。
リンク不正アクセス防止有効化の方法
Refererリンク不正アクセス防止の有効化と設定
1. VODコンソールにログインし、アプリケーションからナビゲーションバーの配信と再生の設定>ドメイン名管理に進み、使用するドメイン名の設定をクリックします。
2. アクセス制御メニューバーに進み、「Refererリンク不正アクセス防止」を有効化し、「リンク不正アクセス防止のタイプ」で「ホワイトリスト」を選択し、テキストボックスにビデオの再生を許可するサイトのドメイン名リストを入力し、OKをクリックします。
3. 「Keyリンク不正アクセス防止」を開き、リンク不正アクセス防止Keyを入力またはランダム生成し、OKをクリックします。
これで、ドメイン名のRefererリンク不正アクセス防止およびKeyリンク不正アクセス防止が有効になりました。
プレーヤー署名の構成方法
VODのプレーヤーを使用してビデオを再生する際は、プレーヤー署名を使用する必要があります。署名のパラメータ渡しのルールは次のとおりです。
1. appIdとfileIdにはご自身のappIdと、ビデオに対応するfileIdをそれぞれ入力します。
2. contentInfo内のaudioVideoTypeにはProtectedAdaptiveと入力します。
3. drmAdaptiveInfo内のprivateEncryptionDefinitionには14を、widevineDefinitionには21を、fairPlayDefinitionには12を入力します。
4. urlAccessInfo内のtには再生リンクの有効期限(現在時刻+ビデオ時間+30分)を、rlimitには3を、usにはランダム生成された文字列(毎回の署名生成の際にランダム生成されます)を、uvには視聴者の一意のIDをそれぞれ入力します。
暗号化されたビデオの再生
3. プレーヤーが業務サーバーからプレーヤー署名を取得し、再生を開始します。
上記の方法で操作を行うと、プレーヤーが暗号化されたビデオの再生を開始します。FairPlayおよびWidevineをサポートしている再生端末では、商用DRMで保護された出力が優先的に再生されます。FairPlayおよびWidevineをサポートしていない再生端末では、プライベート暗号化出力が再生されます。
フィードバック