概览
下载
聚焦模式
字号
概览页权限
具有 QcloudCamSummaryAccess 策略权限的用户登录控制台,可查看所有模块的信息。
没有 QcloudCamSummaryAccess 策略权限的用户登录控制台,只能查看登录链接和上次登录信息。
主账号、管理员用户(AdministratorAccess)均已包含该策略权限。
子账号可以联系主账号(在 用户列表 > 用户详情页面)查看其是否具有 QcloudCamSummaryAccess 策略权限。
主账号可以将 QcloudCamSummaryAccess 策略授权给需要的子账号,允许子账号查看控制台概览页的所有信息。授权方法请参考 授权管理。
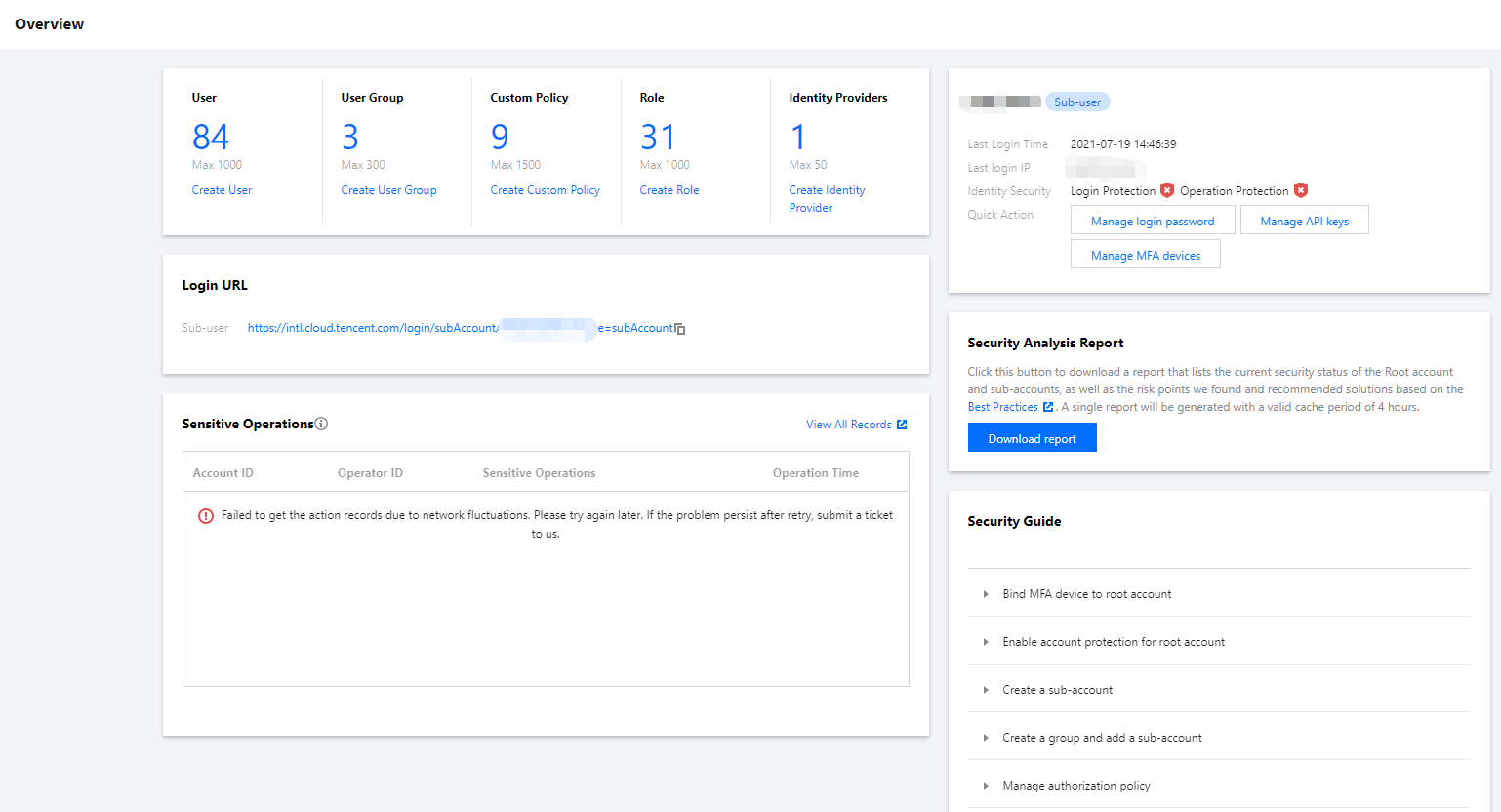
概览页模块
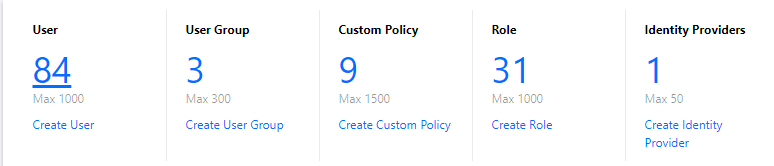
访问管理资源
访问管理资源模块展示当前主账号下所创建的用户、用户组、自定义策略、角色、身份提供商数量。您可以通过单击数量下方的按钮,进入对应的创建页面。
登录链接
登录链接模块展示了子用户的登录链接。主账号和子账号均可通过链接右侧的复制按钮复制链接。
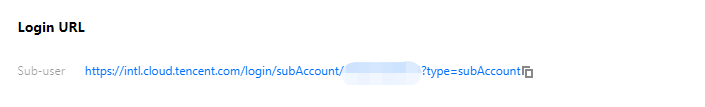
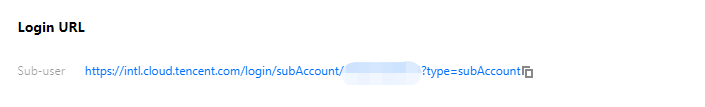
子用户登录链接:适用于子用户。
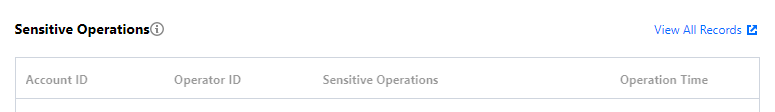
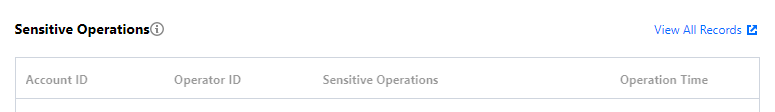
敏感操作
敏感操作模块展示最近3天(最高50条)当前主账号下所有敏感操作的概览信息,展示信息包括:账号 ID、操作者 ID、详细敏感操作和操作时间。用户还可以通过单击【查看所有记录】,进入云审计控制台,查看更详细的敏感操作记录。
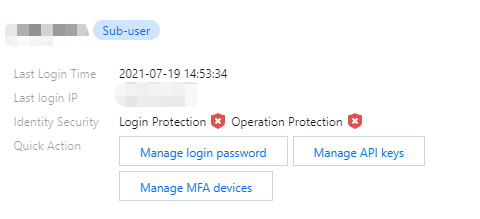
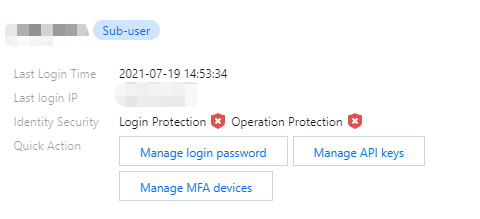
上次登录信息
上次登录信息模块展示当前账号的上次登录时间,上次登录 IP、身份安全状态、管理 API 密钥、管理 MFA 设置快捷操作入口。
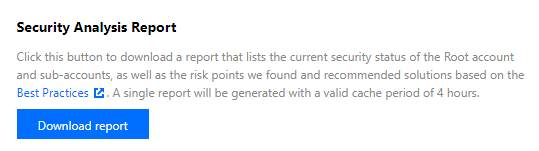
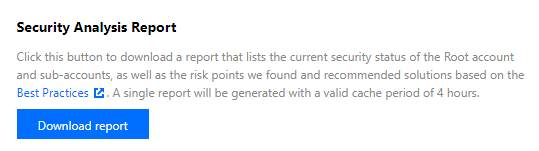
安全分析报告
安全指引
注意:
为了保障您的账户以及云上资产的安全,我们强烈建议您完成安全指引下的所有设置。
安全指引模块为用户提供基础 CAM 功能学习和必要的安全操作指引,包括主账号绑定 MFA 设备、主账号开启账号保护、创建子账号和创建组并添加子账号等。
操作权限:主账号绑定 MFA 设备 和 主账号开启账号保护 两项设置只有主账号具有操作权限;其余五项设置,获得授权的所有用户都可以进行操作。
指引状态:各指引项分为 未完成 和 已完成 两种状态。主账号登录控制台可以看到各指引项的状态,具有权限的子账号无法查看状态。
设置入口:具有权限的子账号可通过单击各指引项左侧的三角符号查看对应的功能介绍和相应的设置入口。下图是主账号登录控制台后的安全指引模块示例。
文档反馈