IP Access Restrictions
Download
Focus Mode
Font Size
Introduction
This document describes how to use custom policy to restrict sub-accounts’ access IPs. After setting the policy, the set IPs will control the sub-accounts’ access to the root account resources.
Prerequisites
Directions
1. Go to the Policies management page and click New Custom Policy in the upper left corner.
2. In the selection window that pops up, click Create by Policy Generator.
3. In the Service and Action selection page, enter the following information:
Effect: Required. Select “Allow”. If you choose “Deny”, users or groups will not be able to obtain authorization.
Service: Required. Select the product you want to add.
Action: Required. Select product permissions according to your requirements.
Resources: Required. For more information on what to enter, see Resource Description Method.
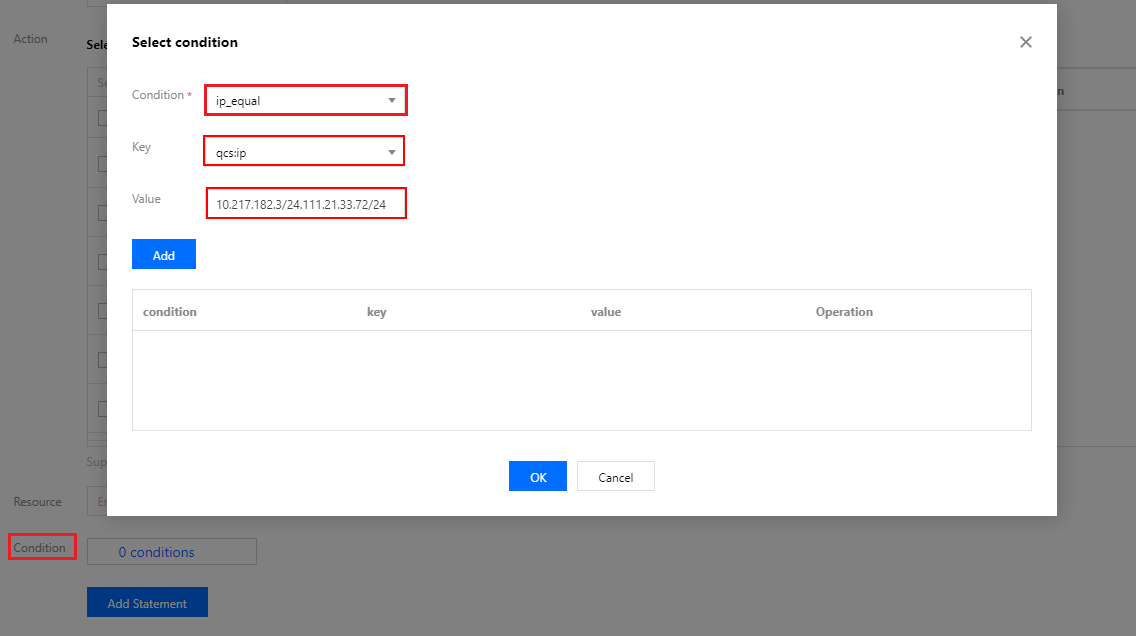
Conditions: Enter the IP address according to your needs. You can add multiple restrictions. For example, for effect, select Allow to only permit users or groups from this IP address to obtain authorization.
Use Case
In the following example, the user must be in the 10.217.182.3/24 or 111.21.33.72/24 IP ranges to invoke the cos:PutObject Cloud API call. This is shown in the following figure:
The policy syntax is as follows:
{"version": "2.0","statement": [{"effect": "allow","action": "cos:PutObject","resource": "*","condition": {"ip_equal": {"qcs:ip": ["10.217.182.3/24","111.21.33.72/24"]}}}]}
Help and Support
Was this page helpful?
You can also Contact sales or Submit a Ticket for help.
Help us improve! Rate your documentation experience in 5 mins.
Feedback