权限边界
下载
聚焦模式
字号
概念
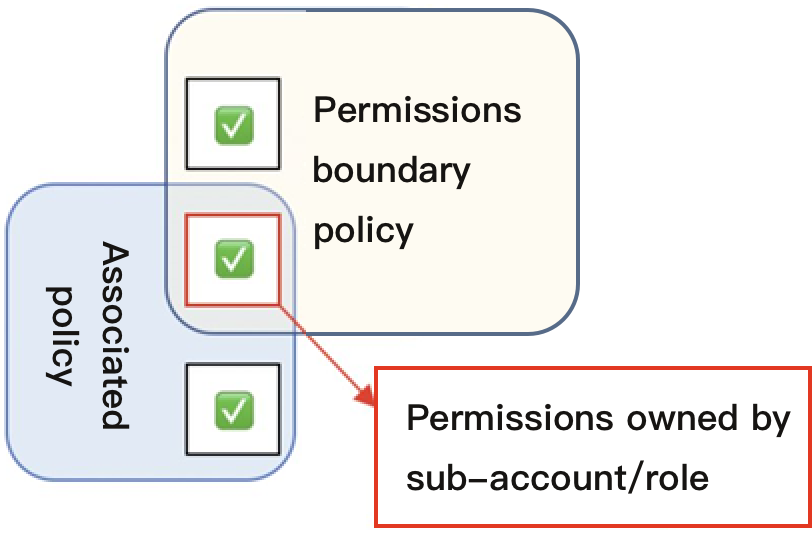
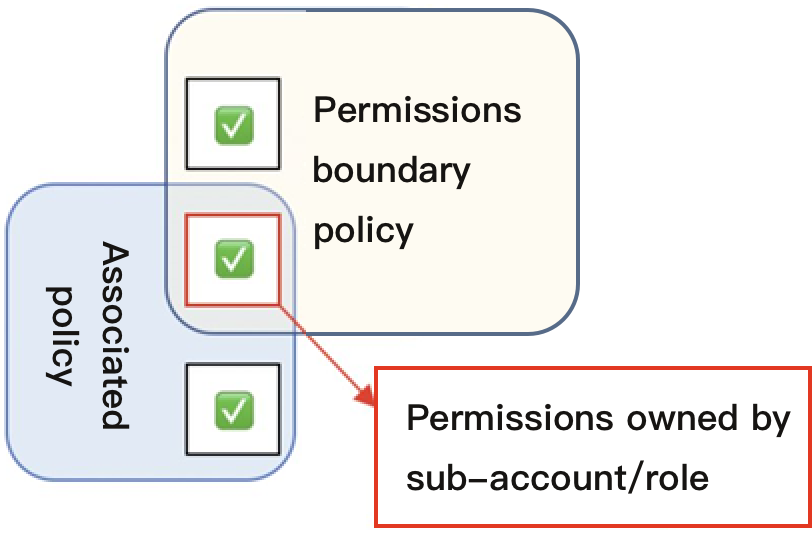
权限边界是腾讯云用于对子账号/角色设置权限边界的一种高级功能。当您设置子账号/角色的权限边界时,该子账号/角色只能执行子账号/角色关联策略和其权限边界同时允许的操作。权限边界仅限制子账号/角色拥有的最大权限范围,不能用于设置子账号/角色关联的权限,详细评估逻辑可参考下图:
使用场景
您可以使用预设策略或自定义策略为子账号/角色设置权限,该策略为子账号/角色的最大权限。本文档以一个典型案例让您轻松了解如何使用权限边界设置子账号的最大权限。
假设公司腾讯云资源管理员需要为运维员工设置权限,需满足以下需求:
公司有两个运维员工,分别拥有昵称为 test1、test2 的两个子账号。
拥有子账号 test1 的员工仅需要管理主账号下云数据库 MySQL 的所有权限。
拥有子账号 test2 的员工仅需要管理主账号下实例 ID 为 ins-1 的服务器操作权限。
公司规定所有子账号对于主账号下云服务器、 云数据库 MySQL 的相关的操作都必须在公司所在网段(10.217.182.3/24 或者 111.21.33.72/24 )操作。
操作步骤
子账号 test1 权限设置
1. 登录公司管理员账号,进入 用户列表页面。
2. 在用户列表页面,找到昵称为 test1 的子账号,单击用户昵称进入用户详情页面。
3. 在权限-权限策略操作栏,单击关联策略勾选 QcloudCDBFullAccess 策略 ,为子账号 test1 设置云数据库 MySQL 的所有权限。
4. 在权限-权限边界操作栏,单击设置边界,进入设置权限边界页面。
5. 在设置权限边界页面,单击新建自定义策略,进入新建自定义策略页面。
6. 在新建自定策略页面,策略名称设置为「policygen-1」。
7. 在可视化策略生成器栏,勾选补充以下信息:
效果(Effect):选择「允许」。
服务(Service):选择「云数据库 MySQL」。
操作(Action):选择「全部操作」,单击确定。
资源(Resource):默认为全部资源(*)。
条件(Condition):勾选来源 IP,补充IP值为「10.217.182.3/24,111.21.33.72/24」。
8. 单击创建,进入设置权限边界页面。
9. 在设置权限边界页面,策略列表操作栏下勾选创建的自定义策略。
10. 单击设置边界,完成为子账号 test1 权限设置。
子账号 test 2 权限设置
1. 登录公司管理员账号,参考以下策略语法创建策略名称为 policygen-2 的自定义策略语法,操作步骤可参阅按策略语法创建。
{"version": "2.0","statement": [{"effect": "allow","resource": ["qcs::cvm:gz::instance/ins-1"],"action": ["name/cvm:*"]}]}
2. 在 用户列表页面,找到昵称为 test2 的子账号,单击用户昵称进入用户详情页面。
3. 在权限-权限策略操作栏,单击关联策略勾选 policygen-2 策略 ,为子账号 test2 设置云服务器 ins-1 的操作权限。
4. 在权限-权限边界操作栏,单击设置边界,进入设置权限边界页面。
5. 在设置权限边界页面,单击新建自定义策略,进入新建自定义策略页面。
6. 在新建自定策略页面,策略名称设置为「policygen-3」。
7. 在可视化策略生成器栏,勾选补充以下信息:
效果(Effect):选择「允许」。
服务(Service):选择「云服务器」。
操作(Action):选择「全部操作」,单击确定。
资源(Resource):默认为全部资源(*)。
条件(Condition):勾选来源 IP,补充IP值为「10.217.182.3/24,111.21.33.72/24」。
8. 单击创建,进入设置权限边界页面。
9. 在设置权限边界页面,策略列表操作栏下勾选 policygen-3 策略。
10. 单击设置边界,完成为子账号 test2 权限设置。
文档反馈