このドキュメントでは、新しいセキュリティグループの作成を例に、インスタンスのカスタマイズ設定の際に、Tencent Cloudが提供するセキュリティグループルールを使用してセキュリティグループの初回設定を行う方法についてご説明します。セキュリティグループに関するより多くの操作は、CVMコンソールのセキュリティグループ画面で行うことができます。詳細については、セキュリティグループの概要 をご参照ください。 セキュリティグループの設定
1. セキュリティグループの設定の際は、実際のニーズに応じて、下図のように新しいセキュリティグループを選択します。
説明:
使用できるセキュリティグループがすでにある場合は、既存のセキュリティグループを選択できます。
2. 実際のニーズに応じて、オープンにしたいIP/ポートにチェックを入れます。
セキュリティグループの新規作成には以下のルールを提供します。
ICMP:ICMPプロトコルをオープンにし、パブリックネットワークPingサーバーを許可します。
TCP:80:ポート80をオープンにし、HTTPによるWebサービスへのアクセスを許可します。
TCP:22:ポート22をオープンにし、SSHLのLinux CVMへのリモート接続を許可します。
TCP:443:ポート443をオープンにし、HTTPSによるWebサービスへのアクセスを許可します。
TCP:3389:ポート3389をオープンにし、RDPのWindows CVMへのリモート接続を許可します。
プライベートネットワークをオープン:プライベートネットワークをオープンにし、異なるクラウドリソース間のプライベートネットワークが互換性(IPv4)を有することを許可します。
説明:
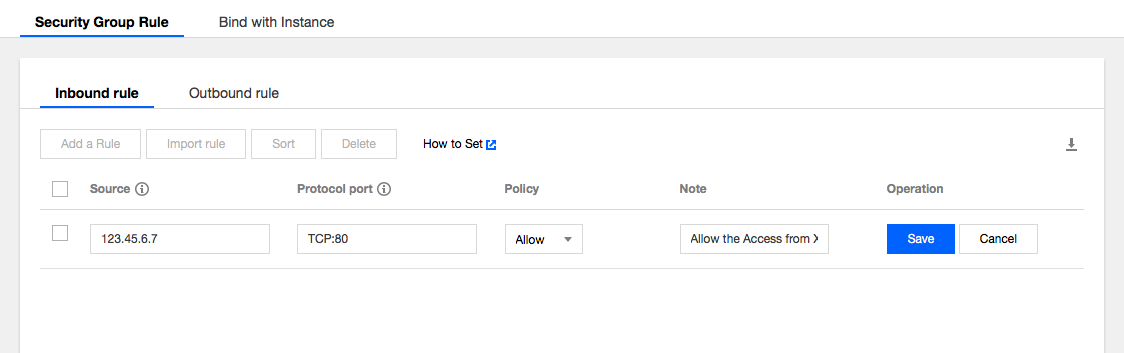
オープンにしたいIP/ポートにチェックを入れると、**セキュリティグループのルール**に詳細なセキュリティグループのインバウンド/アウトバウンドルールが表示されます。
業務上、他のポートをオープンにする必要がある場合は、セキュリティグループの応用例 を参照して セキュリティグループの新規作成 を行うこともできます。セキュリティ上の観点から、Tencent Cloudはなるべく業務に必要なポートのみをオープンにすることで不要なリスクを避けることをお勧めしています。 セキュリティグループのルール
インバウンドルール:セキュリティグループに関連付けられたCVMへの到達が許可されたインバウンドトラフィックを表します。
アウトバウンドルール:CVMから出るアウトバウンドトラフィックを表します。
セキュリティグループ内ルールの優先順位:位置が上のものほど優先順位が高くなります。
CVMがルールのないセキュリティグループにバインドされている場合、すべてのインバウンド、アウトバウンドトラフィックはデフォルトで拒否されます(ルールがある場合は、ルールが優先的に発効します)。
CVMが複数のセキュリティグループにバインドされている場合、セキュリティグループの優先順位は数字が小さいものほど優先順位が高くなります。
CVMが複数のセキュリティグループにバインドされている場合、優先順位が最も低いセキュリティグループのルール発効はデフォルトで拒否されます。
セキュリティグループの制限